
[Type text]
1 | P a g e
Air Force Civil Engineer
Utility Energy Service Contract
(UESC) Playbook
2017
This Playbook is an electronic document. The only valid version is the latest version on the CE Portal. Click here to go to
the CE Portal. Publish Date: 02/20/2018

Air Force Civil Engineer Center
UESC Playbook
2 | P a g e
Table of Contents
Chapter 1 Introduction – Utility Energy Service Contract (UESC) ..................................................................4
Chapter 2 UESC Background, Authority, Financing and Funding ...................................................................5
2.1 Background ..................................................................................................................................................... 5
2.2 Authority ......................................................................................................................................................... 5
2.3 Financing UESCs .............................................................................................................................................. 6
2.3.1 Energy Cost Savings ............................................................................................................................. 6
2.3.2 Guaranteed Savings ............................................................................................................................ 7
2.3.3 Energy Costs ........................................................................................................................................ 7
2.3.4 Maintenance Responsibilities ............................................................................................................. 7
2.3.5 Annual Reconciliation ......................................................................................................................... 7
2.3.6 Buy-down ............................................................................................................................................ 8
2.4 Funding Requirements ................................................................................................................................... 8
2.4.1 Funding UESC Projects ........................................................................................................................ 8
2.4.2 Additional Funding Rules .................................................................................................................... 8
Chapter 3 UESC Roles and Responsibilities ................................................................................................ 10
3.1 AFCEC/CND Roles and Responsibilities ........................................................................................................ 10
3.2 BEM Roles and Responsibilities .................................................................................................................... 10
3.3 CO Roles and Responsibilities ....................................................................................................................... 10
3.4 COTR Roles and Responsibilities................................................................................................................... 11
3.5 Utility Contractor Roles and Responsibilities ............................................................................................... 11
Chapter 4 Types of UESC Contracts ........................................................................................................... 12
4.1 GSA AWC ...................................................................................................................................................... 12
4.2 BOA ............................................................................................................................................................... 13
4.3 Interagency Agreement ................................................................................................................................ 13
4.4. Stand Alone Contract .................................................................................................................................... 13
Chapter 5 UESC Contracting Processes ...................................................................................................... 14
5.1 Installation Contracting Process ................................................................................................................... 14
5.1.1 Phase 1: Project and Acquisition Process......................................................................................... 14
5.1.2 Phase 2: Project Development ......................................................................................................... 16
5.1.3 Phase 3: Final Design and Construction/Installation ....................................................................... 19
5.1.4 Phase 4: Post Project Installation ..................................................................................................... 20
Chapter 6 UESC Business Practices ............................................................................................................ 21
6.1 Baseline Development .................................................................................................................................. 21
6.2 Performance Tests ........................................................................................................................................ 21
6.3 Energy Savings Validation ............................................................................................................................. 22
6.4 Annual Reconciliation Plan (Audit of Savings) .............................................................................................. 23
6.5 Maintenance Related to the TO ................................................................................................................... 23
6.6 Pricing of TO Work ........................................................................................................................................ 23
6.7 Equipment Ownership .................................................................................................................................. 24
Appendix A - Acronym List ........................................................................................................................ 25
Appendix B - References and Master List of Links ....................................................................................... 27
Appendix C - Job Aids ................................................................................................................................ 32
UESC Planning Checklist ................................................................................................................................... 32
Risk/Responsibility Checklist ........................................................................................................................... 34
Appendix D - Guidance .............................................................................................................................. 37
AFCEC Guide to Annual M&V Activities ........................................................................................................... 37
UESC Considerations for the BEM ................................................................................................................... 38

Air Force Civil Engineer Center
UESC Playbook
3 | P a g e
JUSTIFICATION AND APPROVAL ....................................................................................................................... 40
EMSA/MODEL AGREEMENT ............................................................................................................................ 45
Basic Statement of Work (SOW) for the “Letter of Interest” .......................................................................... 62
UESC Task Order (TO) Sample .......................................................................................................................... 63
AFGM 2017-32-01 ............................................................................................................................................ 75
Engineering Technical Letter (ETL) 11-1: Civil Engineer Industrial Control System Information Assurance
Compliance ...................................................................................................................................................... 88
Table of Figures
Figure 1 Procurement Mechanisms ......................................................................................................................... 12
Figure 2 Phase 1: Project and Acquisition Process ................................................................................................. 14
Figure 3 Phase 2: Project Development .................................................................................................................. 16
Figure 4 Phase 3: Final Design and Construction/Installation ................................................................................ 19
Figure 5 Phase 4: Post Project Installation .............................................................................................................. 20
Table of Tables
Table 1 Authority Documents Mandating the AF UESC Program .............................................................................. 5

Air Force Civil Engineer Center
UESC Playbook
4 | P a g e
Chapter 1 Introduction – Utility Energy Service Contract (UESC)
The objective of the UESC Playbook is to provide the parameters and guidance for implementing a
UESC, replacing Engineering Technical Letter (ETL) 12-10: Utility Energy Service Contract (UESC) dated
3 April 2012. This Playbook contains a basic history of the UESC program, primary roles and
responsibilities, step-by-step instructions, job aids, and reference documents to ensure UESC
procedures are followed. This Playbook applies to all Air Force Installations considering using a UESC
including, but not limited to, General Services Administration (GSA), Energy Management Service
Agreements (EMSA), and individual installation contracts. Any deviations require written approval from
the Energy Savings Performance Contract (ESPC)/UESC Program Manager, Air Force Civil Engineer
Center (AFCEC/CND).
Job Aids, resources and reference materials are provided digitally in Links and can be modified as
required by AFCEC/CND.
Limitations: This Playbook does not replace, supersede, or circumvent existing Department of Defense
(DoD) or Air Force (AF) policy.
Applicability: This Playbook is written for the following personnel: AFCEC/CND, Base Civil Engineers
(BCE), Base Energy Managers (BEM), Base Financial Managers (BFM), and installation Contracting
Officers (CO).
Note: Must comply with AFGM2017-32-01, Air Force Guidance Memorandum (AFGM) Civil Engineer
Control Systems Cybersecurity (2 Feb 2017). The AFGM supersedes ETL 11-1, Civil Engineer Industrial
Control System Information Assurance Compliance (30 Mar 2011). However, the AFGM (12 pages)
does not address all items included in ETL 11-1 (32 pages). Therefore, those ETL 11-1 items not
addressed in the AFGM, are still in effect.

Air Force Civil Engineer Center
UESC Playbook
5 | P a g e
Chapter 2 UESC Background, Authority, Financing and Funding
2.1 Background
A UESC is a contract that allows utilities to provide their government customers with energy and
water efficiency improvements and demand-reduction services. UESCs leverage third-party funds
to identify and implement energy conservation measures (ECMs) for a financing term of up to 25
years by statute 10 United States Code (U.S.C.) 2913. AFCEC limits the financing term to the cost
effectiveness of the included ECMs. The AF can use UESCs for all buildings, excluding leased
buildings (unless leased from another Federal agency), where the AF pays the utility bill.
UESCs are typically considered to increase facility energy efficiency through improvements to
installation infrastructure, buildings, and building systems. Under a UESC, a serving or franchised
utility company identifies energy savings strategies that yield an economic return on the
investment. UESCs are used for the following:
1. Reducing energy use
2. Reducing water use
3. Installing high efficiency equipment and/or control systems
4. Re-commissioning or retro-commissioning energy consuming systems
The utility designs and installs the equipment. The capital costs can be paid with appropriated
funds or financed by the utility company. A UESC should be implemented with assurance that the
energy savings can be validated for the term of the UESC and meet the legal intent of the UESC.
Used effectively, a UESC can reduce energy consumption and improve facility infrastructure.
2.2 Authority
The following table lists the Executive Orders (E.O.), directives, and policies that mandate and
support the AF UESC program:
Authority Documents Mandating the AF UESC Program
10 U.S.C. 2911-13, Energy Performance Goals and Plans for Department of Defense
E.O. 13423, Strengthening Federal Environmental, Energy, and Transportation Management (revoked in 2015).
Replaced by: E.O. 13693, Planning for Federal Sustainability in the Next Decade
E.O. 13514, Federal Leadership in Environmental, Energy, and Economic Performance (revoked in 2015). Replaced by: E.O.
13693, Planning for Federal Sustainability in the Next Decade
Public Law (P.L.) 109-58, Energy Policy Act of 2005
10 Code of Federal Regulations (CFR) 436, Federal Energy Management and Planning Programs (10 CFR 436.18-19)
Energy Independence and Security Act (EISA) of 2007
10 U.S.C. 2866, Water Conservation at Military Installations
Air Force Policy Directive (AFPD) 32-10, Installations and Facilities
Table 1 Authority Documents Mandating the AF UESC Program

Air Force Civil Engineer Center
UESC Playbook
6 | P a g e
10 U.S.C. 2913 states that:
1. The Secretary of Defense may authorize the Secretary of a military department having
jurisdiction over a military installation to enter into agreements with gas or electric utilities
to design and implement cost-effective demand and conservation incentive programs
(including energy management services, facilities alterations, and the installation and
maintenance of energy saving devices and technologies by the utilities) to address the
requirements and circumstances of the installation.
2. If an agreement under this subsection provides for a utility to advance financing costs for
the design or implementation of a program referred to in that paragraph to be repaid by the
United States, the cost of such advance may be recovered by the utility under terms no less
favorable than those applicable to its most favored customer.
3. Subject to the availability of appropriations, repayment of costs advanced under paragraph
(2) shall be made from funds available to a military department for the purchase of utility
services.
4. An agreement under this subsection shall provide that title to any energy-saving device or
technology installed at a military installation pursuant to the agreement vest in the United
States. Such title may vest at such time during the term of the agreement, or upon
expiration of the agreement, as determined to be in the best interests of the United States.
2.3 Financing UESCs
UESC projects, funded or financed, must produce financial savings that are equal to or greater
than the cost of implementation, including the cost of financing. All UESC costs, including mid-
contract replacement of capital equipment, must be funded out of the UESC savings they
generate, unless funded using appropriated funds. An installation's post-UESC utility costs, such
as energy and Operations and Maintenance (O&M), plus the cost of the UESC project cannot
exceed the utility costs prior to the implementation of the UESC project. If the project is financed,
the energy cost savings are used to pay the utility.
2.3.1 Energy Cost Savings
Energy cost savings are annual recurring savings, including:
1. Recurring reductions in expenses (other than energy costs) related to energy-
consuming equipment, including costs associated with waste disposal.
2. One-time energy-related cost savings resulting from avoided expenditures because
of the UESC project.
3. Demand-related savings, such as peak shaving.
4. One-time utility rebates.
The utility contractor is responsible for the design, acquisition, installation, and
measurement and verification (M&V) of the project equipment or systems that produce
the savings is required. Refer to 2.3.5 Annual Reconciliation for more information. Refer
to the GSA Utility Contractors List to view approved contractors.

Air Force Civil Engineer Center
UESC Playbook
7 | P a g e
Certain risks are associated with implementing a UESC for the AF. It is essential the AF
does not assume any of the utility contractor’s risk, such as ECM performance. AF risks
include utility rates and mission changes.
Refer to the Risk/Responsibility Checklist job aid for guidance.
2.3.2 Guaranteed Savings
There are no guaranteed savings in a UESC contract. The equipment installed is
guaranteed to perform for one year and provisions shall be made for the labor, supplies,
parts, and materials to maintain the Energy Conservation Project (ECP) for the term of the
Task Order (TO). However, annual verification of energy savings must be accomplished.
This requirement includes an approved M&V plan (see 2.3.5).
As an exception, guaranteed savings can be negotiated into a TO if the local utility provider
offers it. If part of the TO, the utility company provides a guarantee of savings to the AF
and establishes payment schedules reflecting the guarantee.
The payment to the utility is based on an agreed upon percentage of the calculated
savings. These awarded TOs, like utility bills, are “must-pay” requirements and are
programmed into the annual utility budget process. Refer to 42 U.S.C. 8287, Section
801(a)(2)(A).
2.3.3 Energy Costs
Annual payments by the AF under a UESC cannot exceed the value of energy and O&M
savings relative to costs prior to the UESC. Refer to 42 U.S.C. 8287; Section 801(a)(2)(B).
Forecasted energy costs and the discount rate (present value of future cash flows) are
major factors in determining UESC savings. 10 CFR 436, Federal Energy Management and
Planning Programs, provides detailed instructions for UESCs, including the calculation of
life cycle costs. For example, 10 CFR 436.14 mandates the use of the annual supplement to
Life Cycle Costing Manual for the Federal Energy Management Program (National Institute
of Standards and Technology [NIST] 85-3273) to determine the discount rate and
forecasted energy costs. UESCs must use the NIST-published "implied long-term average
rate of inflation" with the appropriate regional fuel price indices. AF installations are
considered “industrial” for the purpose of calculating the NIST utility escalation rate. The
provisions in 10 CFR 436.14 are mandatory and failure to comply results in the contract
being found legally insufficient.
2.3.4 Maintenance Responsibilities
The installation is responsible for TO-required maintenance and repair. Maintenance and
repair are critical to sustain an ECM’s performance throughout the life of the TO. Ensure
provisions are made for the labor, supplies, parts, and materials to maintain the ECP for the
term of the TO. Refer to section 6.5 Maintenance Related to the TO for more information.
2.3.5 Annual Reconciliation
An annual reconciliation is required for a UESC. A verification of energy savings
reconciliation must be accomplished for each awarded TO annually. This requirement
includes an approved M&V plan using at a minimum the current International Performance
Measurement and Verification Protocol (IPMVP) at the time the TO is awarded. Measured

Air Force Civil Engineer Center
UESC Playbook
8 | P a g e
savings are required when using options B or option C metered savings, where a minimum
of one third savings are measured. During the annual reconciliation, the utility contractor
confirms the adequacy of maintenance. Refer to paragraph (a)(2)(A) of 42 U.S.C. 8287.
The BEM validates the utility company’s annual reconciliation follows the agreed upon
M&V plan.
2.3.6 Buy-down
UESC costs may be funded with installation funds used to buy down part of the TO, such as
end-of-year fallout funds. These one-time funds can be identified in the payment schedule
to the utility company upon acceptance of the ECM and commencement of the
performance period. This allows for a lower financed amount and shorter term, thereby
reducing interest costs over the term. Buy-down schedules are recommended for projects
with payment periods greater than 5 years. If, after award, O&M funds are used to buy
down a portion of the TO, several steps are necessary:
1. Use of these funds must be identified as soon as possible to the utility company.
2. Economics must be considered.
3. Prepayment penalties must be identified by the utility company.
2.4 Funding Requirements
2.4.1 Funding UESC Projects
Title 10 USC § 2913(d)(3) specifies that repayment of financed costs be made from funds
available to a military department for the purchase of utility services. UESC savings must be
real and verifiable so the installation doesn’t run the risk of a savings shortfall. Work that
encompasses O&M-type savings or other savings that do not eliminate actual costs or
produce actual savings versus avoided costs should not be included. Civilian personnel costs
are not allowed unless positions are deleted from manpower documents.
Use caution if applying anticipated cost avoidance to the UESC due to major
repair/replacement that may not be needed because of the UESC. Historical data may not be
able to back up expenditures, but the costs may be justified as a future expense; for
example, as an engineering analysis or as life cycle predictions. If these major expenditures
are included as captured savings, they become a “must-pay” bill from O&M funds. Before
these funds are included in a UESC, the installation and AFCEC/CND must agree to the
funding source and create a record of decision to justify the action and agreement.
2.4.2 Additional Funding Rules
Facilities under a UESC may require a buyout before non-UESC work is performed.
Government actions (post award) on a building that will impact, alter, or dismantle UESC
material or equipment, rendering that part of the UESC contract invalid, should buyout the
applicable portion of the contract. Examples include demolition, upgrades, construction
and privatization.
When possible, buyout funds should be programmed with the same fund source as the
project itself. Any demolition, upgrades, construction, or privatization shall be identified to
the CO for evaluating and determining appropriate contract action.

Air Force Civil Engineer Center
UESC Playbook
9 | P a g e
The following additional funding rules apply:
1. Military Construction (MILCON) funds cannot be applied to a UESC. MILCON
projects cannot be accomplished under a UESC. Use of MILCON funds for a
purpose outside appropriated use would result in a violation of the Purpose Act (31
U.S.C. 1301).
2. Non-appropriated Fund (NAF) functions may be authorized to use appropriated
O&M funds. NAF Category C ECPs must use savings only from other NAF ECPs to
avoid subsidizing or being subsidized by funds other than NAF-funded sources. All
actions affecting funding must be coordinated with the NAF funds manager.
3. Military Family Housing (MFH) funds are appropriated separately and used
specifically for MFH purposes. MFH ECPs must use savings only from other MFH
ECPs to avoid subsidizing or being subsidized by funds other than MFH-funded
sources. Use of MFH funds for a purpose outside their appropriated use would
result in a violation of the Purpose Act (31 U.S.C. 1301).
4. Reimbursable customers require separate accounting procedures to ensure that
adequate payments are being applied to their accounts. Reimbursable customers
must agree to a memorandum of agreement or equal to provide payments for the
term of the contract.

Air Force Civil Engineer Center
UESC Playbook
10 | P a g e
Chapter 3 UESC Roles and Responsibilities
This chapter provides an in-depth explanation of the roles and responsibilities associated with the UESC
process.
3.1 AFCEC/CND Roles and Responsibilities
a. Serves as the UESC Program Management Office (PMO) and centrally manages all UESCs.
Provides initial vetting, approves each stage of project development, manages the
evaluation process, and assists installations in the development of the UESC project through
completion of the TO term. Provides technical review and approval of all UESC projects.
b. Coordinates and supports the contracting office, as needed.
c. Develops UESC procedures/guidance and provides UESC training to appropriate installation
personnel, following the Department of Energy (DoE) Federal Energy Management Program
(FEMP) UESC guidelines.
d. Acts as the center of expertise for UESC contracts. Provides tools and expertise to assist in
implementing a UESC. Acts as a clearinghouse for UESC lessons learned.
e. Maintains oversight and compliance with AF policies and interprets guidance for the
installation’s UESC program.
3.2 BEM Roles and Responsibilities
a. The Defense Logistics Agency-Energy (DLA-Energy) is the execution contracting office for all
AF UESC Projects. Installation BCE and the local CO may submit a waiver request to
AFCEC/CND PMO to execute locally. AFCEC, in conjunction with the installation makes the
final determination for the office of execution.
b. Works with the CO to implement the UESC program. Compiles and provides required
project documentation, including site data packages and evaluation criteria to the CO.
Performs an analysis on all construction costs and provides a statement to the CO that all
costs are realistic for the work performed. Refer to Considerations for the BEM for more
information.
c. Completes UESC training before implementing a UESC program and ensures that assigned
personnel associated with the UESC program receive this training for the term of the UESC.
d. Assists the CO in ensuring the utility company complies with all requirements for the term
of the TO.
e. Determines if other funding sources such as Sustainment, Restoration and Modernization
(SRM) and the Energy Conservation Investment Program (ECIP) are available and more cost-
effective.
f. Ensures the CO is notified of mission changes, facility modifications, or demolition.
3.3 CO Roles and Responsibilities
a. Overall responsibility to ensure that ESPC projects serve the best interests of the AF and are
consistent with the terms and conditions of the ESPC contracts, legislation, and regulations.

Air Force Civil Engineer Center
UESC Playbook
11 | P a g e
b. Awards and administers all issued UESC TOs following AFCEC/CND technical review and
approval.
c. Assembles the UESC team and serves as chairperson for all meetings with the utility
company.
d. Evaluates and documents mission changes, facility modifications, and demolition for
appropriate contract action.
e. Appoints a Contracting Officer Technical Representative (COTR) to act as a liaison between
the utility contractor and the CO.
f. Provides the total contract cost for each phase of a UESC and a final signed copy of the TO
to AFCEC/CND.
3.4 COTR Roles and Responsibilities
a. Acts as technical representative for CO.
b. Identifies and supports project goals and development efforts.
c. Reviews all deliverables.
d. Provides oversight during construction and installation.
e. Reviews and approves technical aspects of the annual M&V reports, when applicable.
3.5 Utility Contractor Roles and Responsibilities
a. Develops and submits a Preliminary Assessment (PA) and Feasibility Study (FS).
b. Documents the baseline data and ensures the data adequately supports the baseline.
Simulation models are not acceptable baselining tools.
c. Provides funding for energy reduction project(s).
d. Implements the UESC project, including purchasing equipment, installing equipment, and
overseeing and completing construction during projects.
e. Performs metering and data collection to ensure energy reduction and provides the M&V
report.

Air Force Civil Engineer Center
UESC Playbook
12 | P a g e
Chapter 4 Types of UESC Contracts
The AF has several types of UESC contracts available to them, including, GSA Area-wide Contracts
(AWCs), Interagency Agreements and EMSAs. Basic Ordering Agreements (BOA) are not contracts, but
establish general terms and conditions for future TO or Delivery Order (DO). Agencies not covered by
such agreements may enter contracts with their servicing utility. If an AWC exists with a utility,
AFCEC/CND must approve the use of other procurement mechanisms. EMSAs serve as a template for
agencies to use in establishing UESC’s or as a Master Agreement Exhibit “C” within an AWC, EMSAs can
be used as a standalone contracting vehicle.
4.1 GSA AWC
Utility services can include electricity, natural or manufactured gas, water, sewage, thermal
energy, chilled water, steam, hot water, and high-temperature hot water. AWCs outline general
terms and conditions and authorize any agency in a utility’s franchised service territory to place
TOs for utility services and utility energy services offered under the contract. Refer to the GSA
Utility Contractors list to view the servicing area utility contractors.
The GSA has numerous active utility AWCs to procure energy, water, and renewable energy
systems projects. Installations develop an EMSA, which is provided as an attachment to the
existing GSA AWC. If more than one utility company can offer energy management services the
AF provides a fair opportunity and selects the one that provides the best value. If only one utility
is available, the CO prepares a justification and approval (J&A), prior to having negotiations that
lead to an award without full and open competition Federal Acquisition Regulations (FAR)
6.302.5. Refer to the Justification and Approval for Other Than Full and Open Competition sample
document.
Note: Financing is an option for Federal facilities.
GSA AWC contracts are
within a utility provider’s
service territory.
BOAs are used when
there is not an AWC.
BOAs contain terms,
conditions, and services
for future delivery orders.
EMSAs are used in
establishing UESCs. They
can be a Master
Agreement Exhibit “C”
within an AWC, BOA or as
a stand-alone agreement.
Figure 1 Procurement Mechanisms

Air Force Civil Engineer Center
UESC Playbook
13 | P a g e
4.2 BOA
A BOA is an agreement between the utility and the installation to establish general terms and
conditions that are incorporated into future firm fixed-price TOs and may be used when an AWC
does not exist. A federal agency can establish a BOA with their utility when specific items,
quantities, and prices are not known, but a substantial number of requirements are anticipated
and there is potential for more than one UESC TO. A TO placed under a BOA constitutes the
contract and details the services to be delivered.
A BOA does not guarantee future TOs to the utility and is not used to restrict competition if more
than one utility supports an installation. The agreement is reviewed annually and revised, as
necessary, to meet the requirements of the FAR 16.703. A modification to the agreement itself
does not retroactively affect any individual TOs issued under it.
The CO establishes the BOA with the utility employing normal contracting procedures in
accordance with FAR 16.703, DFARS 216.703, and Procedures, Guidance and Information (PGI)
217.703(d).
4.3 Interagency Agreement
Bonneville Power Administration (BPA) – Provides energy management services to their
customers within their service territory.
4.4. Stand Alone Contract
For installations where the utility does not have an AWC, an EMSA may be used as a template for
terms and conditions and award is made to the utility under the authority of 10 U.S.C. 2913.

Air Force Civil Engineer Center
UESC Playbook
14 | P a g e
Chapter 5 UESC Contracting Processes
5.1 Installation Contracting Process
5.1.1 Phase 1: Project and Acquisition Process
Figure 2 Phase 1: Project and Acquisition Process
Steps 1 & 2: Installation leadership decides to conduct a UESC project and requests
AFCEC/CND approval.
Prior to engaging with a utility, the CO and the BEM/BCE prepare a summary of the type of
ECMs being considered and relevant baseline information and submits them to AFCEC/CND
for initial vetting. AFCEC/CND works with the CO and BEM/BCE to determine if the UESC is
an appropriate choice for execution. Note: AFCEC serves as advisor through project life.
Refer to the UESC Planning Checklist job aid for guidance.
Steps 3 & 4: The CO develops the Statement of Work (SOW) and the acquisition strategy.
DLA-Energy is the execution contracting office for all AF UESC projects.
The CO and BEM review the utility agreement (AWC) to ensure it allows for energy and
demand-side management services. Refer to Considerations for the BEM for guidance on
implementing a successful UESC. The Energy Team is assembled and a date and time is
coordinated for an on-site meeting or teleconference with AFCEC/CND to explore potential
opportunities, develop the UESC criteria, and determine the acquisition strategy. The
Energy Team ensures the UESC contract adheres to appropriate, and confirms the scope
and pricing of the project are in the best interest of the AF. The key activities of an
acquisition strategy are:
1. Developing a clear scope with schedule.
2. Planning a sound and equitable business arrangement.
3. Managing risk of concurrent development/production.
4. Planning to support installed systems/equipment.
5. Ensuring competition.
6. Obtaining resources to award and administer the contract.
7. Developing the SOW. For an example, refer to the Sample SOW.

Air Force Civil Engineer Center
UESC Playbook
15 | P a g e
Steps 5 & 6: The CO sends a “Letter of Interest” to each eligible utility and provides each
utility with a fair opportunity to be considered.
The CO contacts each serving utility to determine interest in providing a UESC. The letter
should:
1. Clarify agency intention to use UESC to meet energy goals.
2. Describe the initial project scope.
3. Inform the serving utilities of the opportunity for consideration to all.
4. Provide evaluation method and criteria.
Refer to the GSA Utility Contractors list to view the servicing area utility contractors.
Step 7: The CO drafts the initial J&A.
The J&A is to be executed prior to negotiations leading to TO award without full and open
competition. J&As use guidance provided in the following regulations:
1. FAR 6.302‐5
2. 10 USC 2304(c)(5)
3. Competition in Contracting Act (CICA)
J&As are initiated during acquisition planning and establishes the contractor meets the
definition of a utility. The J&A describes services offered by the utility and why
performance by the utility is required, indicating the agreement will be cost effective, fair,
and reasonable. J&As are finalized before awarding the TO.
Refer to the Justification and Approval for Other Than Full and Open Competition form for
an example.
Note: If more than one utility company can offer energy management services, all must be
provided a fair opportunity to participate and select the one that provides the best value;
no J&A required. However, if only one utility is available, the CO must prepare a J&A prior
to negotiations, leading to an award without full and open competition.
Steps 8 & 9: The CO notifies the servicing utilities of the selection results.
In selecting a utility, the following evaluation factors may be used:
1. Is this a multi‐year project with multiple TOs or will this have a single TO?
2. What experience does the utility have doing UESC projects?
3. What types of projects has the utility done in the past?
a. How complex were previous projects compared to current project?
b. What was the size and scope of the previous projects?
c. How was their past performance?
d. What are their staff qualifications?

Air Force Civil Engineer Center
UESC Playbook
16 | P a g e
4. Is their pricing clear?
a. Do they provide an explanation of fees and markups?
b. Do they provide expectation of payment and cost recovery for assessments?
c. Do they have the ability to secure financing at reasonable terms?
5. What is the AF’s history and experience with the utility?
5.1.2 Phase 2: Project Development
Step 10: The CO requests a PA from the utility and evaluates the utility’s response.
The PA is a high-level assessment that:
1. Provides a baseline for existing conditions.
2. Identifies potential water and energy efficiency and renewable energy
opportunities.
3. Estimates the cost to implement the opportunities.
The CO develops a Master Agreement Exhibit “C”, checks the appropriate box and provides
details of specific base requirements. The Master Agreement Exhibit “C” must be signed by
the utility representative and CO. Typically, a PA is at no cost to the government. If there
is a cost to the government, the cost should be negotiated with the utility and included in
the Master Agreement Exhibit “C”.
Note: If a long-term project or multiple projects are anticipated, use the EMSA. The EMSA
is a template for developing a Master Agreement Exhibit “C” and contains terms and
conditions essential to a UESC. It can be used to issue single or multiple TOs for the four
phases:
1. Preliminary Audit
2. Feasibility Study
3. Engineering/Design
4. Construction/Implementation
If the EMSA is not used, each phase will have a separate Master Agreement Exhibit “C”.
Figure 3 Phase 2: Project Development

Air Force Civil Engineer Center
UESC Playbook
17 | P a g e
Once the utility completes the PA and delivers a proposal, the Energy Team reviews the
proposal and provides written comments to the CO. A government-only meeting and/or
teleconference is held to discuss the comments and determine if recommended measures
will be pursued in a FS. The CO ensures all parties have reviewed the proposal. Once
AFCEC/CND approves, the CO prepares authorization for the utility to begin an FS.
Note: If the government decides to terminate at this point and the PA costs were
negotiated, the CO documents the decision and provides an invoice to pay the utility.
Step 11: The CO requests the FS and evaluates the utility’s response.
Unless the EMSA was used at the PA, the CO develops a Master Agreement Exhibit “C” and
checks the appropriate box for the FS. The CO clarifies the ECMs from the PA to be
included and negotiates the development cost of the FS prior to obtaining signatures. If
financing, the cost is rolled into the next phase. The CO may require that the development
cost of the FS be obligated before proceeding to that step.
The FS is a detailed analysis that:
1. Identifies and describes a technically viable and cost-effective project scope.
2. Develops a baseline of energy and water consumption, equipment inventory and
conditions, and operational schedules.
3. Provides a plan for training, O&M, and performance assurance.
4. Provides a project design sufficient to support a firm-fixed price for design and
implementation (D&I).
The utility should provide a detailed, open‐book cost estimate with the FS.
Note: The FS is commonly referred to as an “Investment Grade Audit” (IGA).
The utility completes an in-depth FS of the selected ECMs and delivers a feasibility proposal
to the Energy Team. The Energy Team reviews the proposal and provides written
comments to the CO to consolidate. Prior to sending comments to the utility, a
government-only meeting and/or teleconference is held to discuss the consolidated
comments and determine if recommended measures will advance to the
Engineering/Design phase. The CO ensures all parties have reviewed the proposal. Once
AFCEC/CND approves, the CO prepares authorization for the utility to begin an
engineering/design study.
Note: If the government decides to terminate the FS at this point, the CO documents the
decision and provides invoice to pay the negotiated FS costs.
Note: If the installation requests to cancel the project after the completion of the FS, the
installation must provide a letter of cancellation to the AFCEC/CND Program Manager on
the installations letterhead detailing the reason for the requested termination of the
project. The letter is required to be signed by the BCE and can be transmitted
electronically.
Steps 12 & 13: The CO submits a firm-fixed price Request for Proposal (RFP) for design
and Energy Team evaluates the utility’s proposal.

Air Force Civil Engineer Center
UESC Playbook
18 | P a g e
The CO sends a letter requesting a firm‐fixed price for D&I. The utility responds with the
following information:
1. A letter showing the firm‐fixed price offer.
2. An updated design schedule.
3. An updated installation schedule.
4. Finalized financing terms.
Step 14: The installation CO finalizes the J&A.
Refer to the Justification and Approval for Other Than Full and Open Competition form for
an example.
Step 15: The installation CO issues the Award of Task Order for design and
implementation.
The award letter:
1. States the TO executes a contract under the AWC.
2. Provides authorization to proceed with the project.
3. Lists attachments, which include:
a. Scope of work, specifications, and performance standards.
b. Terms and conditions.
c. Agency‐specific clauses not in AWC or Master Agreement Exhibit “C”.
d. Templates for invoicing, price schedule and termination schedule.
4. Requests confirmation or update of schedule for D&I.
5. Sets time and location for kick‐off meeting.
6. Provides name and contact information of the CO and the COTR.
Refer to the Task Order Sample for an example TO.
UESCs are subject to the requirements of part 17.1 of the FAR, which requires federal agencies
to notify Congress at least 30 days prior to the award of certain proposed multiyear contracts.
FAR part 17.1 establishes the Congressional notification requirement for multiyear contracts
that include a cancellation ceiling in excess of $125 million. See 48 C.F.R. § 17.108(b). The
Congressional notification requirement need not be burdensome or result in undue delay.
Notification can be provided when a reasonable estimate of the underlying project’s
cancellation ceiling is obtained, which generally occurs well in advance of contract award.
Such early notification may also be provided on a periodic basis (e.g., semiannually, quarterly,
etc.) and for multiple UESCs.

Air Force Civil Engineer Center
UESC Playbook
19 | P a g e
5.1.3 Phase 3: Final Design and Construction/Installation
Figure 4 Phase 3: Final Design and Construction/Installation
Step 16: The utility submits engineering designs and the CO reviews/approves.
The CO develops the Master Agreement Exhibit “C” and checks the appropriate box for ECP
Engineering/Design Study and clarifies the ECMs from the FS proposal. The CO directs the
use of all appropriate AF design and construction standards and negotiates the
development cost for engineering/design prior to obtaining signatures. If financing, the
development costs are rolled into the TO.
The utility provides the final design, plans, and specifications with detailed pricing
consistent with the FS and provides a final proposal to the Energy Team. The Energy Team
reviews the final proposal and provides written comments to the CO to consolidate. Prior
to sending comments to the utility, a government-only meeting and/or teleconference is
held to discuss consolidated comments and determine if recommended measures will
progress to the construction/installation phase. The utility addresses the consolidated
comments. The Energy Team reviews the comments and determines if a TO should be
issued for the construction phase. The CO negotiates any revisions and prepares internal
documentation required prior to award.
The utility submits a final proposal with all negotiated changes and the final financing
schedule. Once internal approval is obtained, the CO awards the TO and provides copies to
AFCEC/CND. The CO provides a copy of the TO award with the executed Master
Agreement Exhibit “C” to the GSA regional office within 30 days after execution.
Steps 17 & 18: The utility constructs/installs the ECMs and the installation CO and COTR
provides oversight. The utility provides O&M training, performance assurance,
commissioning, etc.
During construction/installation, AF oversight is critical. Due diligence requires the AF to
trust and verify to ensure the installed ECMs meet design and performance requirements.
The utility begins construction/installation in accordance with (IAW) the TO. Once the utility
performs the work, prior to government acceptance, the utility will provide:
1. ECM training
2. O&M manuals
3. As-built drawings/specifications
4. Testing of each ECM IAW the commissioning plan.
The BEM or COTR witnesses the utility’s commissioning activities.

Air Force Civil Engineer Center
UESC Playbook
20 | P a g e
Note: If no award is made, the CO documents the decision and provides an invoice to pay
the negotiated engineering/design costs.
Steps 19 & 20: The CO accepts the ECM projects and reports project details to FEMP and
GSA.
After all of the ECMs are installed, tested, and commissioned and all deliverables are
received, the CO signs a Certificate of Completion that includes a checklist and statement
allowing payments to begin.
5.1.4 Phase 4: Post Project Installation
Figure 5 Phase 4: Post Project Installation
Step 21: The CO submits invoices & payments.
Timely payment to the utility is critical. Payment frequency is defined in the TO. Invoices
can be paid as part of the utility bill. Payments should be made using proper accounting,
budgeting, and invoicing procedures.
Step 22: The utility provides services (such as performance assurance, etc.) per the TO.
The performance assurance plan prescribes the post‐acceptance activities, i.e., AF
responsibilities and utility responsibilities.
Reporting should be done IAW the performance assurance plan and FEMP/GSA
guidelines. GSA and FEMP must be notified of the TO award. The notification includes:
1. Report on the use of AWC and service agreements including the Authorization
for Energy Management Services.
2. FEMP UESC Data Collection.
3. Annual Agency reports include UESC project information.
Step 23: The installation closes out the contract at the end of the TO.
Note: AFCEC/CND reserves the right to use the Defense Logistics Agency-Energy (DLA-
Energy) as the contracting office for UESC projects.

Air Force Civil Engineer Center
UESC Playbook
21 | P a g e
Chapter 6 UESC Business Practices
The following business practices help the installation implement a UESC, translate the legislative
requirements, and apply the lessons learned to achieve a successful ECM. Each TO includes mutually
agreed upon procedures defining how to verify ECM performance post-installation.
6.1 Baseline Development
An energy baseline is the amount of energy that would have been used if no energy conservation
equipment had been installed. The utility contractor must clearly document the baseline data.
M&V is part of a UESC contract, metering and data collection are performed by the utility
contractor and verified by the installation to ensure the baseline reflects realistic energy
consumption upon which the savings calculations are based. Data collection requirements vary
by ECP and M&V method, but metered data is required for weather-impacted ECPs. Existing
meters should be used as much as possible to collect this data. The M&V plan must be
measurement-based. If the utility contractor and AFCEC/CND determine that model by
simulation is the only valid methodology, the models must be validated/calibrated by the utility
contractor and verified by installation personnel. Refer to the AFCEC Guide to M&V Activities for
more information on M&V requirements.
Note: It is important that equipment controlled by ambient temperature devices have valid
measurements. Savings validation and future baseline adjustments will require this data before
modifications can be applied to the existing baseline.
All assumptions made in the preliminary audit should be validated in the FS by the utility
contractor. Validation includes documenting all pertinent data and formulas used to compute the
energy savings so the BEM can easily explain these savings in the future. AFCEC/CND review and
endorsement of the baseline is required.
6.2 Performance Tests
A performance test is a process for achieving, verifying, and documenting the performance of
equipment installed or modified as part of an ECP. This process begins in the FS phase with the
development and approval of a performance test plan that is implemented after the TO award.
Performance tests are completed post construction to certify that all equipment is functioning
and operating properly. The results are approved by AFCEC/CND before conducting the energy
savings verification tests.
A performance test plan is developed as part of the FS phase and is prepared for each ECP. The
performance test plan describes all aspects of the test process, including:
1. Schedules
2. Responsibilities
3. Documentation requirements
4. Functional performance test requirements
The functional performance tests describe:
1. The conditions or loads the tests are performed.

Air Force Civil Engineer Center
UESC Playbook
22 | P a g e
2. The location of test sensors.
3. The frequency of measurements.
4. The type of test equipment.
5. The test methods.
6. The acceptable range of results.
The level of detail depends on the complexity of the ECP. The performance test plan is detailed
enough so the installation knows exactly what tests will be performed, prior to signing the TO
award.
The final acceptance report is submitted after all functional performance tests are completed.
The final acceptance report is submitted for approval in writing to the CO and BEM. The final
acceptance report includes:
1. The executive summary.
2. ECP descriptions.
3. The performance plan.
4. Test results.
The CO approves the performance test results after coordination and verification of results by the
BEM.
6.3 Energy Savings Validation
A formal set of test procedures with the acceptable range of results are developed to validate
energy savings. These test procedures are submitted by the utility contractor during the FS and
approved before awarding the TO. The test procedures describe:
1. The conditions or loads for the tests being performed.
2. The location of test sensors.
3. The frequency of measurements.
4. The type of test equipment used.
5. Test methods.
6. The acceptable range of test results.
The test procedures shall verify all energy savings intended under the ECP/ECM.
After the BEM/CO approves the performance test results for each ECP, the utility contractor
performs the approved energy savings test procedures to validate the energy savings for each
ECP.
Once the validated energy savings have been approved for all ECPs, the utility contractor submits
an invoice for payment the first full month after acceptance of the ECM.

Air Force Civil Engineer Center
UESC Playbook
23 | P a g e
6.4 Annual Reconciliation Plan (Audit of Savings)
Each ECM in the TO has, at a minimum, a detailed annual reconciliation plan approved before the
TO award. The plan describes:
1. A formal set of test procedures.
2. An acceptable range of results.
3. A schedule of how reconciliation payments will be assessed if savings fall below the
guarantee.
4. A certification by the utility that all O&M requirements and conditions have been met for
each ECP in the TO.
The procedures should be similar to those developed to validate energy savings. The purpose is
to test, validate, and document the energy savings. The CO must approve the annual
reconciliation of savings after coordination and verification of savings by the BEM.
6.5 Maintenance Related to the TO
Maintenance is the responsibility of the BCE. Similar to a construction contract, the Utility is
responsible for a 1-year warranty period, unless other conditions are negotiated. Refer to section
2.3.4 Maintenance Responsibilities for more information.
6.6 Pricing of TO Work
The BEM/CO requests that the utility company provide detailed documentation needed to
determine the reasonableness of the price. Utility company estimates for each ECP identify all
major costs, including:
a. Equipment
b. Labor
c. Design
d. Maintenance
e. Repair
f. Parts
g. Overhead and profit
h. Travel
i. M&V, as required in the ECP
The government prepares an independent government estimate (IGE).
Ancillary savings are any savings attributable to the project other than energy savings, such as
manpower, materials, or eliminating contract-operated functions. Maintenance, repair, or
operations costs for tasks currently being performed by the government or government
contractor are ancillary savings if the utility:
1. Assumes the tasks
2. Reduces the tasks
3. Eliminates the tasks.

Air Force Civil Engineer Center
UESC Playbook
24 | P a g e
Savings must be real and verifiable. The BEM determines whether a utility-proposed task
elimination or reduction would be considered an ancillary savings available for sharing. The AF
provides the dollar value of the ancillary savings.
Government civilian positions must be deleted from the official manpower rosters before related
savings are added to the UESC proposal. The BEM/CO must work the request through
AFCEC/CND and Air Staff so the funds can be reprogrammed to the UESC account. A provision is
included in the package to capture the lost manning in at least one Program Objective
Memorandum (POM) cycle prior to the end of the UESC TO.
Note: O&M funds may need to be expended to pay the utility until the reprogramming action is
completed.
The final negotiated savings shall be applied to the UESC contract. The cost of elimination
contract-operated functions are not negotiated until after TO award. These costs are estimated
and added into the TO.
6.7 Equipment Ownership
Generally, the AF owns the equipment post-construction and must update real property records
to show ownership of the utility installed equipment. The utility is required to provide to the AF,
prior to contract completion, O&M manuals, maintenance training, and the Material Inspection
and Receiving Report (DD-250 Form). However, due to taxes and/or rebates, occasionally the
utility retains ownership post-construction. In either case, the ownership determination is
defined and agreed upon within the TO.

Air Force Civil Engineer Center
UESC Playbook
25 | P a g e
Appendix A - Acronym List
Acronym
Definition
AF
Air Force
AFCEC/CND
Air Force Civil Engineer Center, Energy Program Development Division
AFPD
Air Force Policy Directive
AWC
Area-wide Contract
BCE
Base Civil Engineer
BEM
Base Energy Manager
BFM
Base Financial Managers
BOA
Basic Ordering Agreements
BPA
Bonneville Power Administration
CE
Civil Engineer
CFR
Code of Federal Regulations
CICA
Competition in Contracting Act
CO
Contracting Officer
COTR
Contracting Officer Technical Representative
D&I
Design and Implementation
DLA
Defense Logistics Agency
DO
Delivery Order
DoD
Department of Defense
DoE
Department of Energy
ECIP
Energy Conservation Investment Program
ECM
Energy Conservation Measure
ECP
Energy Conservation Project
EISA
Energy Independence and Security Act
EMSA
Energy Management Service Contract
EO
Executive Order
ESCO
Energy Services Company
ES&H
Environmental, Safety & Health
ESPC
Energy Savings Performance Contract
ETL
Engineering Technical Letter
FAR
Federal Acquisition Regulation
FEMP
Federal Energy Management Program
FFP
Firm Fixed Price
FIO
Facilities Improvements Office
FS
Feasibility Study
GHG
Greenhouse Gas
GSA
General Services Administration
HAZMAT
Hazardous Material
HMI
Human Machine Interface
IAW
In Accordance With
IES
Illuminating Engineering Society
IGA
Investment Grade Audit
IGE
Independent Government Estimate
IPMVP
International Performance Measurement and Verification Protocol
J&A
Justification and Approval
JB
Joint Base
M&O
Maintenance and Operations
M&V
Measurement and Verification
MFH
Military Family Housing
MILCON
Military Construction
NAF
Non-appropriated Fund
NIST
National Institute of Standards and Technology
O&M
Operations and Maintenance

Air Force Civil Engineer Center
UESC Playbook
26 | P a g e
Acronym
Definition
ODC
Ozone Depleting
ORCA
Online Representation and Certifications Application
OSHA
Occupational Safety and Health Administration
PA
Preliminary Assessment
PGI
Procedures, Guidance and Information
P.L.
Public Law
PLC
Programmable Logic Controller
PMO
Project Management Office
POM
Program Objective Memorandum
QAE
Quality Assurance Evaluator
RFP
Request for Proposal
SOW
Statement of Work
SRM
Sustainment, Restoration and Modernization
TO
Task Order
U.S.C.
United States Code
UESC
Utility Energy Service Contracts

Air Force Civil Engineer Center
UESC Playbook
27 | P a g e
Appendix B - References and Master List of Links
Section
Type
Name of Item
Linked
Link
Chapter 2, 4,
Justification and
Approval for
Other Than Full
and Open
Competition
External
10 U.S.C. 2913
https://www.gpo.gov/fdsys/pkg/USCODE-2010-title10/pdf/USCODE-2010-
title10-subtitleA-partIV-chap173-subchapI-sec2913.pdf
Chapter 2
External
10 United States
Code (U.S.C.) 2911-
13, Energy
Performance Goals
and Plans for
Department of
Defense
https://www.gpo.gov/fdsys/granule/USCODE-2010-title10/USCODE-2010-
title10-subtitleA-partIV-chap173-subchapI-sec2911
Chapter 2
External
E.O. 13423,
Strengthening
Federal
Environmental,
Energy, and
Transportation
Management
https://www.fedcenter.gov/programs/eo13423/
Chapter 2,
Justification and
Approval for
Other Than Full
and Open
Competition
External
E.O. 13693,
Planning for
Federal
Sustainability in the
Next Decade
https://energy.gov/lm/downloads/executive-order-13693-planning-federal-
sustainability-next-decade
Chapter 2
External
E.O. 13514, Federal
Leadership in
Environmental,
Energy, and
Economic
Performance
https://www.fedcenter.gov/programs/eo13514/
Chapter 2,
Justification and
Approval for
Other Than Full
and Open
Competition
External
Public Law (P.L.)
109-58, Energy
Policy Act of 2005
https://www.gpo.gov/fdsys/pkg/PLAW-109publ58/pdf/PLAW-109publ58.pdf
Chapter 2
External
10 Code of Federal
Regulations (CFR)
436, Federal Energy
Management and
Planning Programs
(10 CFR 436.18-19)
https://www.gpo.gov/fdsys/search/pagedetails.action?collectionCode=CFR&b
rowsePath=Title+10%2FChapter+II%2FSubchapter+D%2FPart+436%2FSubpart
+A%2FSection+436.18&granuleId=CFR-2002-title10-vol3-sec436-
18&packageId=CFR-2002-title10-vol3&collapse=true&fromBrowse=true
Chapter 2
External
Energy
Independence and
Security Act (EISA)
of 2007
https://www.gpo.gov/fdsys/pkg/PLAW-110publ140/pdf/PLAW-
110publ140.pdf

Air Force Civil Engineer Center
UESC Playbook
28 | P a g e
Section
Type
Name of Item
Linked
Link
Chapter 2,
Justification and
Approval for
Other Than Full
and Open
Competition
External
10 U.S.C. 2866,
Water
Conservation at
Military
Installations
https://www.law.cornell.edu/uscode/text/10/2866
Chapter 2
External
Air Force Policy
Directive (AFPD)
32-10, Installations
and Facilities
http://static.e-publishing.af.mil/production/1/af_a4_7/publication/afpd32-
10/afpd32-10.pdf
Chapter 2
Bookmark
2.3.5 Annual
Reconciliation
Bookmarked to Section 2.3.5 Annual Reconciliation
Chapter 2, 4, 5
Internal
GSA Utility
Contractors list
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/GSA%20Utili
ty%20Contractors%20List.doc
Chapter 2
Bookmark
Risk/Responsibility
Checklist
Bookmarked to the Risk/Responsibility Checklist
Chapter 2
External
42 U.S.C. 8287,
Section
801(a)(2)(A)
https://www.gpo.gov/fdsys/pkg/USCODE-2010-title42/html/USCODE-2010-
title42-chap91-subchapVII.htm
Chapter 2
External
42 U.S.C. 8287;
Section
801(a)(2)(B)
https://www.gpo.gov/fdsys/pkg/USCODE-2010-title42/html/USCODE-2010-
title42-chap91-subchapVII.htm
Chapter 2
External
10 CFR 436, Federal
Energy
Management and
Planning Programs
https://www.gpo.gov/fdsys/granule/CFR-1999-title10-vol3/CFR-1999-title10-
vol3-part436
Chapter 2
External
10 CFR 436.14
https://www.gpo.gov/fdsys/granule/CFR-2011-title10-vol3/CFR-2011-title10-
vol3-sec436-14
Chapter 2
External
Life Cycle Costing
Manual for the
Federal Energy
Management
Program (National
Institute of
Standards and
Technology [NIST]
85-3273)
https://energy.gov/eere/femp/building-life-cycle-cost-programs
Chapter 2
Bookmark
6.5 Maintenance
Related to the TO
Bookmarked to Section 6.5 Maintenance Related to the TO
Chapter 2
External
Title 10 USC §
2913(d)(3)
http://uscode.house.gov/view.xhtml?req=granuleid:USC-prelim-title10-
section2913&num=0&edition=prelim
Chapter 2
External
Purpose Act (31
U.S.C. 1301)
https://www.gpo.gov/fdsys/granule/USCODE-2010-title31/USCODE-2010-
title31-subtitleII-chap13-subchapI-sec1301
Chapter 3, 5
Internal
Considerations for
the BEM
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/UESC%20Co
nsiderations%20for%20the%20%20BEM.docx
Chapter 4, 5
External
FAR 6.302.5
http://www.farmaster.com/farmaster/data/idx/FAR84/0603020005.htm
Chapter 4, 5
Internal
Justification and
Approval for Other
Than Full and Open
Competition
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/JandA%20Fo
rm.docx

Air Force Civil Engineer Center
UESC Playbook
29 | P a g e
Section
Type
Name of Item
Linked
Link
Chapter 4,
Justification and
Approval for
Other Than Full
and Open
Competition
External
FAR 16.703
https://www.acquisition.gov/far/html/Subpart%2016_7.html
Chapter 4
External
DFARS 216.703
http://www.acq.osd.mil/dpap/dars/dfars/html/current/216_7.htm
Chapter 4
External
Procedures,
Guidance and
Information (PGI)
217.703(d)
http://www.acq.osd.mil/dpap/dars/dfars/html/current/216_7.htm
Chapter 4, 5
Internal
EMSA
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/MODEL%20
AGREEMENT.docx
Chapter 4
Bookmark
UESC Planning
Checklist
Bookmarked to the UESC Planning Checklist
Chapter 5
Internal
Sample SOW
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/Sample_SO
W.docx
Chapter 5
External
10 USC 2304(c)(5)
http://uscode.house.gov/view.xhtml?req=10+USC+2304%28c%29%285%29&f
=treesort&fq=true&num=22&hl=true&edition=prelim&granuleId=USC-prelim-
title10-section2304c
Chapter 5
External
Competition in
Contracting Act
(CICA)
http://www.cohenseglias.com/federal-contracting-database/competition-in-
the-contracting-act
Chapter 5
Internal
Task Order Sample
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/UESC%20Ta
sk%20Order%20Sample.docx
Chapter 6
Internal
AFCEC Guide to
M&V Activities
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/AFCEC%20G
uide%20to%20MandV%20Activities.docx
Chapter 6
Bookmark
2.3.4 Maintenance
Responsibilities
Bookmarked to Section 2.3.4 Maintenance Responsibilities
AFCEC Guide to
Annual M&V
Activities
External
Guide to
Government
Witnessing and
Review of Post-
Installation and
Annual M&V
Activities
https://www.energy.gov/eere/femp/downloads/guide-government-
witnessing-and-review-measurement-and-verification-activities
AFCEC Guide to
Annual M&V
Activities
External
Reviewing Post-
Installation and
Annual Reports for
Federal ESPC
Projects
https://energy.gov/eere/femp/downloads/reviewing-post-installation-and-
annual-reports-federal-espc-projects
AFCEC Guide to
Annual M&V
Activities
External
FEMP webpage
https://energy.gov/eere/femp/federal-energy-management-program
UESC
Considerations
for the BEM
Internal
AFCEC Guide to
M&V Activities
https://cs2.eis.af.mil/sites/10041/CEPlaybooks/UESC/References/AFCEC%20G
uide%20to%20MandV%20Activities.docx
Justification and
Approval for
Other Than Full
and Open
Competition
External
10 U.S.C. 2913
(D)(3)
https://www.gpo.gov/fdsys/pkg/USCODE-2010-title10/pdf/USCODE-2010-
title10-subtitleA-partIV-chap173-subchapI-sec2913.pdf

Air Force Civil Engineer Center
UESC Playbook
30 | P a g e
Section
Type
Name of Item
Linked
Link
EMSA/Model
Agreement
External
48 CFR 9.404
https://www.law.cornell.edu/cfr/text/48/9.404
EMSA/Model
Agreement
External
FAR, Part 36,
Subpart 36.511
https://www.acquisition.gov/sites/default/files/current/far/html/Subpart%20
36_5.html
EMSA/Model
Agreement
External
FAR, Part 52,
Subpart 52.301
https://www.gpo.gov/fdsys/granule/CFR-2011-title48-vol2/CFR-2011-title48-
vol2-sec52-301
EMSA/Model
Agreement
External
Energy Prices and
Discount Factors
for Life-Cycle-Cost
Analysis
http://nvlpubs.nist.gov/nistpubs/ir/2017/NIST.IR.85-3273-32.pdf
EMSA/Model
Agreement
External
FAR 52.203-3,
Gratuities
https://www.acquisition.gov/sites/default/files/current/far/html/52_200_206
.html
EMSA/Model
Agreement
External
FAR 52.203-5,
Covenant Against
Contingent Fees
https://www.acquisition.gov/sites/default/files/current/far/html/52_200_206
.html
EMSA/Model
Agreement
External
FAR 52.203-7, Anti-
Kickback
Procedures
https://www.acquisition.gov/sites/default/files/current/far/html/52_200_206
.html
EMSA/Model
Agreement
External
FAR 52.222-3,
Convict Labor
https://www.acquisition.gov/sites/default/files/current/far/html/52_222.html
EMSA/Model
Agreement
External
FAR 52.222-25,
Affirmative Action
Compliance
https://www.acquisition.gov/sites/default/files/current/far/html/52_222.html
EMSA/Model
Agreement
External
FAR 52.222-26,
Equal Opportunity
https://www.acquisition.gov/sites/default/files/current/far/html/52_222.html
EMSA/Model
Agreement
External
FAR 52.223-6, Drug
Free Workplace
https://www.law.cornell.edu/cfr/text/48/52.223-6
EMSA/Model
Agreement
External
FAR 52.233-1,
Disputes
https://www.acquisition.gov/sites/default/files/current/far/html/52_233_240
.html
EMSA/Model
Agreement
External
FAR Part 52,
Subpart 52.246-20
https://www.govregs.com/regulations/title48_chapter1_part52_subpart52.2_
section52.246-20
EMSA/Model
Agreement
External
FAR Part 32,
Subpart 32.903
http://federal.elaws.us/cfr/title48.part32.section32.903
EMSA/Model
Agreement
External
FAR Part 32,
Subpart 32.907
https://www.acquisition.gov/sites/default/files/current/far/html/Subpart%20
32_9.html#wp1033041
EMSA/Model
Agreement
External
FAR Part 33,
Subpart 33.2
https://www.acquisition.gov/sites/default/files/current/far/html/Subpart%20
33_2.html
EMSA/Model
Agreement
External
FAR Part 36,
Subpart 36.502
https://www.acquisition.gov/sites/default/files/current/far/html/Subpart%20
36_5.html#wp1076711
EMSA/Model
Agreement
External
FAR Part 42,
Subpart 42.13
https://www.law.cornell.edu/cfr/text/48/part-42/subpart-42.13
EMSA/Model
Agreement
External
10 USC Section
2912
https://www.law.cornell.edu/uscode/text/10/2912
EMSA/Model
Agreement, UESC
Task Order (TO)
Sample
External
FAR Part 17
https://www.acquisition.gov/sites/default/files/current/far/html/FARTOCP17.
html
EMSA/Model
Agreement, UESC
Task Order (TO)
Sample
External
FAR Part 52,
Subpart 52.249-2
https://www.acquisition.gov/sites/default/files/current/far/html/52_248_253
.html

Air Force Civil Engineer Center
UESC Playbook
31 | P a g e
Section
Type
Name of Item
Linked
Link
EMSA/Model
Agreement, UESC
Task Order (TO)
Sample
External
FAR Part 52,
Subpart 52.232.23
https://www.acquisition.gov/sites/default/files/current/far/html/52_2
32.html#wp1152984
EMSA/Model
Agreement, UESC
Task Order (TO)
Sample
External
FAR Part 32,
Subpart 32.8
https://www.law.cornell.edu/cfr/text/48/part-32/subpart-32.8
EMSA/Model
Agreement
External
FAR Part 42,
Subpart 42.12
https://www.acquisition.gov/sites/default/files/current/far/html/Subpart%20
42_12.html
EMSA/Model
Agreement
External
FAR Part 42,
Subpart 42.1204
https://www.acquisition.gov/sites/default/files/current/far/html/Subpart%20
42_12.html
EMSA/Model
Agreement
External
42 U.S.C. §9601
https://www.law.cornell.edu/uscode/text/42/9601
EMSA/Model
Agreement
External
49 CFR Part 172
https://www.gpo.gov/fdsys/pkg/CFR-1998-title49-vol2/xml/CFR-1998-title49-
vol2-part172.xml
EMSA/Model
Agreement
External
FAR Part 52,
Subparts 52.236-2
https://www.acquisition.gov/far/html/52_233_240.html#wp1113365
EMSA/Model
Agreement
External
52.236-3
https://www.acquisition.gov/sites/default/files/current/far/html/52_2
33_240.html#wp1113375
UESC Task Order
(TO) Sample
External
10 CFR 851
https://www.gpo.gov/fdsys/granule/CFR-2012-title10-vol4/CFR-2012-title10-
vol4-part851
UESC Task Order
(TO) Sample
External
FAR 52.246-21
http://www.farmaster.com/farmaster/data/idx/FAR84/5202460021I.htm
UESC Task Order
(TO) Sample
External
FAR 52.236-13
https://www.gpo.gov/fdsys/pkg/CFR-2010-title48-vol2/pdf/CFR-2010-title48-
vol2-sec52-236-13.pdf
UESC Task Order
(TO) Sample
External
FAR 52.228-5
http://farmaster.com/farmaster/data/idx/FAR84/5202280005.htm
Air Force Civil Engineer Center
UESC Playbook
32 | P a g e
Appendix C - Job Aids
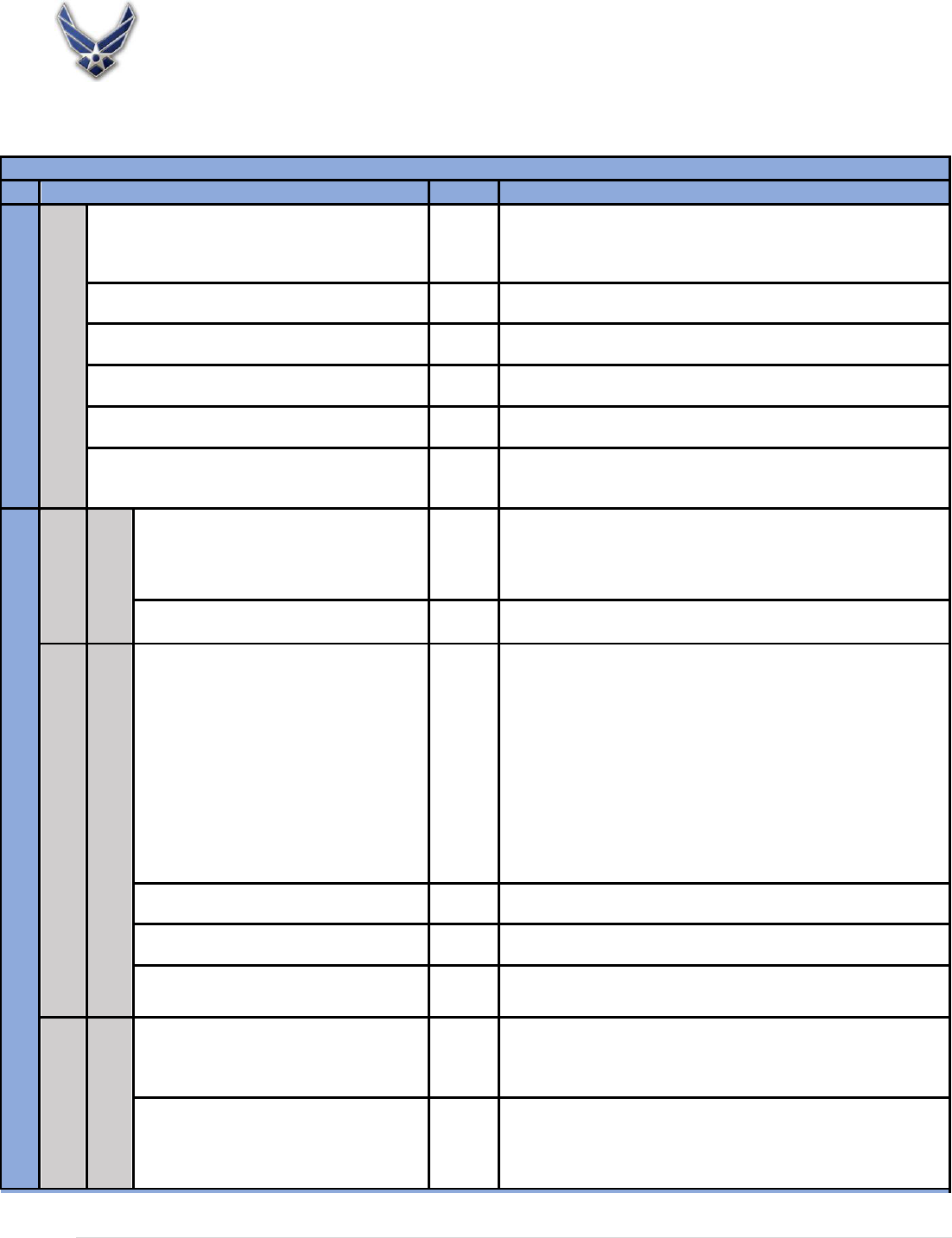
UESC Planning Checklist
UESC Planning and Document Development Checklist
Process Step/Resource Name
Type
Objective
Step 1 Acquisition Planning
2 - 4 weeks
Agency (e.g., installation) develops initial SOW and
submits all proposed UESC projects to AFCEC/CND
as PMO for initial vetting prior to any UESC
engagement with the utility provider.
Sample
Ensure the Agency obtains AFCEC approval to start an UESC prior
to any UESC engagement with the utility provider.
Acquisition Strategy/Planning
Limited Acquisition Plan
Template
Establishes the agency’s strategy for the acquisition of the project.
Survey interest of eligible Utilities
Letter of Interest
Template
Used to determine which servicing utilities are interested and
capable.
Provide fair consideration to interested utilities
Utility Selection Evaluation Factors
Sample
Detailed utility selection sample for a $60M UESC Project.
Draft Initial J&A
J&A
Sample
A sample justification to use a “limited source” contract.
Agency selects utility and notifies all utilities of
selection
Utility Selection Letter
Template
Notifies all serving utilities of the selection.
Step 2 Project Development
Preliminary
Assessment
2 - 4 Weeks
EMSA for PA
EMSA
Letter of Request for PA
PA SOW
Sample
Template
Template
Establishes bilateral agreement for PA.
Cover letter for EMSA or may replace EMSA when no cost PA is
offered.
Provides site information and expectations for PA.
Utility Conducts PA/Agency supports and
evaluates
Feasibility Study
4 - 8 Weeks
EMSA for FS
EMSA
Letter of Request for FS
FS SOW
Performance Assurance Plan
Notice to Proceed to FS
FAR Clauses for UESC not in AWC
AWC
EMSA under AWC
EMSA/Model Agreement
UESC Task Order
Sample
Template
Template
Template
Sample
Sample
Sample
Sample
Sample
Establishes bilateral agreement for FS.
Cover letter for EMSA.
Describes requirements for in-depth analysis of selected ECMs.
Provide to utility an attachment the FS SOW.
Provides instructions, contracts, and official notice to proceed with
FS.
Lists FAR Clauses included by reference in the AWC.
Lists FAR clauses included in the sample EMSA.
Lists FAR Clauses included in the EMSA/Model Agreement.
Shows examples of FAR Clauses listed in sample TO.
Utility Conducts FS/Agency Supports and
evaluates
Agency requests FFP for D&I.
Letter Requesting an FFP Offer for D&I.
Template
CO requests FFP offer for D&I of selected ECMs.
Finalize J&A
Business Clearance Memorandum
Sample
Gives recommendation for contract award with supporting
documentation
Award for Design and
Installation
1 - 3 Weeks
Notify Congress 72 hours before awarding
TOs> $4M
Award D&I TO
Standard Form 26
TO for D&I
EMSA
Sample
Sample
Sample
FAR calls out Form 26; use form to award the contract.
A group of documents that make up the TO.
Establish bilateral agreement for D&I.

Air Force Civil Engineer Center
UESC Playbook
33 | P a g e
UESC Planning and Document Development Checklist
Process Step/Resource Name
Type
Objective
Step 3 Project Implementation
Design
3 - 8
Weeks
Utility submits designs. Agency reviews and
approves
Installation
4 - 8 Weeks
Utility installs ECMs/Agency Monitors
Utility performs/Agency receives O&M
training, commissioning, etc.
ECM Performance Verification
Checklist.
Utility proves ECM Performance
Agency accepts project
Letter of Final Acceptance.
Report project details to FEMP and GSA
UESC Project Reporting
Sample
Template
Template
Lists items to ensure installation/performance meets design intent.
Agency approves work performed by Utility under contract.
Shares project details with FEMP.
Step 4 Post Acceptance
Term of the Contract
Invoices and Payments
Invoice Approval/Payment Process
UESC Invoice
Agency Project Announcement
Implement performance assurance plan and
report annual ECM savings.
Close out contract at end of term.
Template
Sample
Sample
Agency approves and pays invoice.
UESC sample invoice.
Announce project success.

Air Force Civil Engineer Center
UESC Playbook
34 | P a g e
Risk/Responsibility Checklist
Risk/Responsibility Checklist
Risk/Responsibility Description
Does the utility have an
acceptable approach to
deal with the
risk/responsibility?
Has AFCEC/CND assessed
the utility’s approach?
Financial
Interest Rates
Neither the utility nor the AF has significant control over prevailing
interest rates. Interest rates will change with market conditions during all
phases of the project. Higher interest rates will increase project cost,
financing/project term, or both. The timing of the delivery order signing
may impact the available interest rate and project cost. Clarify when the
interest rate is locked in, and if it is a fixed or variable rate.
Energy Prices
Neither the utility nor the AF has significant control over actual energy
prices. For calculating savings, the value of the saved energy may either
be constant, change at a fixed inflation rate, or float with market
conditions. If the value changes with the market, falling energy prices
place the utility company at risk of failing to meet cost savings
guarantees. If energy prices rise, there is a small risk to the AF that
energy-saving goals might not be met while the financial goals are. If the
value of saved energy is fixed (either constant or escalated), the AF risks
making payments in excess of actual energy cost savings.
Construction Costs
The utility is responsible for determining construction costs and defining a
budget. In a fixed-price design/build contract, the AF assumes little
responsibility for cost overruns. If construction estimates are significantly
greater than originally assumed, however, the utility company may find
that the project or measure is no longer viable and drop it. In any
design/build contract, the AF loses some design control. Clarify design
standards and the design approval process (including changes) and how
costs will be reviewed.
M&V Costs
The AF assumes the financial responsibility for M&V costs directly or
through the utility. If the AF wishes to reduce M&V costs, it may do so by
accepting less-rigorous M&V activities with more uncertainty in the
savings estimates. Clarify what performance is being guaranteed
(equipment performance, operational factors, energy cost savings) and
that the M&V plan is detailed enough to satisfactorily verify it. Note: This
only applies if M&V is required.
Delays
Both the utility and the AF can cause delays. Failure to implement a viable
project in a timely manner costs the agency in the form of lost savings,
and can add costs to the project. Clarify the schedule and how delays will
be handled.
Major
Changes in
Facility
The AF (or Congress) controls major changes in facility use, including
closure. Clarify responsibilities in the event of a premature facility closure,
loss of funding, or other major change.

Air Force Civil Engineer Center
UESC Playbook
35 | P a g e
Risk/Responsibility Checklist
Responsibility Description
Does the utility have an
acceptable approach to
deal with the
risk/responsibility?
Has AFCEC/CND assessed
the utility’s approach?
Operational
Operating Hours
The AF generally has control over the operating hours. Increases and
decreases in operating hours can show up as increases or decreases in
"savings," depending on the M&V method (e.g., operating hours,
improved efficiency of equipment vs. whole building, utility analysis).
Clarify if operating hours are to be measured or stipulated and what the
impact will be if they change. If the equipment loads are stipulated, the
baseline should be carefully documented and agreed to by both parties.
Load
Equipment loads can change over time. The AF generally has control
over hours of operation, conditioned floor area, and intensity of use (e.g.,
changes in occupancy or level of automation). Changes in load can show
up as increases or decreases in "savings," depending on the M&V
method. Clarify if equipment loads are to be measured or stipulated and
the impact if they change. If the equipment loads are stipulated, the
baseline should be carefully documented and agreed to by both parties.
Weather
A number of energy efficiency measures are affected by weather.
Changes in weather can increase or decrease "savings" depending on the
M&V method (e.g., equipment run hours x efficiency improvement vs.
whole building utility analysis). If weather is "normalized," actual savings
could be less than payments for a given year but will "average out" over
the long run. Weather corrections to the baseline or ongoing
performance should be clearly specified and understood.
User
Participation
Many energy conservation measures require user participation to
generate savings (e.g., control settings). The savings can be variable and
the utility may be unwilling to invest in these measures. Clarify what
degree of user participation is needed and utilize monitoring and training
to mitigate risk. If performance is stipulated, document and review
assumptions carefully and consider M&V to confirm the capacity to save.

Air Force Civil Engineer Center
UESC Playbook
36 | P a g e
Risk/Responsibility Checklist
Responsibility Description
Does the utility have an
acceptable approach to
deal with the
risk/responsibility?
Has AFCEC/CND assessed
the utility’s approach?
Performance
Equipment
Performance
Generally, the utility has control over the selection of equipment and is
responsible for its proper installation and performance. The utility also
has overall responsibility to demonstrate that the new improvements
meet expected performance levels, including standards of service and
efficiency. Clarify who is responsible for initial and long-term
performance, how performance will be verified, and what will be done if
performance does not meet expectations.
Operations
Responsibility for operations is negotiable, and it can impact
performance. Clarify how proper operation will be assured. Clarify
responsibility for operations and the implications of taking on the
operation of the equipment.
Maintenance and
Repair
Responsibility for maintenance and repair is negotiable; however, it is
often tied to performance. Clarify how long-term maintenance and repair
will be assured, especially if the party responsible for long-term
performance is not responsible for maintenance. Clarify who is
responsible for ECM overhaul and component or equipment repair
required to maintain operational performance throughout the contract
term.
Equipment
Replacement
Responsibility for replacement of contractor-installed equipment is
negotiable; however, it is often tied to ECM performance. Clarify who is
responsible for replacing failed components or equipment throughout the
term of the contract. Specifically address potential impacts on
performance due to equipment failure. Life of equipment is critical to ECM
performance during the contract term. Specify equipment life expected
for all installed equipment and specify warranties proposed for the
installed ECMs.

Air Force Civil Engineer Center
UESC Playbook
37 | P a g e
Appendix D - Guidance
AFCEC Guide to Annual M&V Activities
1. The BEM and/or COTR witness the utility contractor’s M&V activities. This requires a thorough
understanding of the awarded M&V plan to ensure the utility contractor is following the agreed
upon contractual methods, procedures, calculations, and other elements of the approved M&V
plan.
2. FEMP has written guidance, Guide to Government Witnessing and Review of Post-Installation
and Annual M&V Activities, which is required when using a DoE UESC contract. The document
addresses:
a. Witnessing baseline metering and data collection.
b. Post-installation M&V activities.
c. First-year M&V inspections and analysis.
d. Annual M&V inspections and analysis.
e. Commissioning of installed energy conservation projects/measures (ECP/ECM) by a
utility.
In addition, it recommends agencies designate an individual(s) to observe these inspections,
review the resulting M&V reports, and certify, in writing, that the reports are acceptable and
validate the actual savings. This guidance may help the installation pass an audit.
3. FEMP has published Reviewing Post-Installation and Annual Reports for Federal ESPC Projects to
assist agencies when reviewing post-installation and annual M&V reports received from the
utility contractor.
4. Refer to the FEMP webpage for more information.

Air Force Civil Engineer Center
UESC Playbook
38 | P a g e
UESC Considerations for the BEM
The following considerations can help the BEM implement a successful UESC project.
1. The BEM submits all proposed UESC projects to AFCEC/CND for initial vetting. Projects will only
be considered when they make good business sense and are necessary to achieve energy goals.
AFCEC/CND approves each stage of the project and assists in awarding and administering the
TO.
2. Though the utility company brings technical energy expertise to the installation’s energy
program, the BEM should have a plan to improve the energy efficiency of the buildings, and
determine how to most efficiently plan and schedule the work to be accomplished. Ask local
facility managers and operations staff for ideas on improving their building’s operational
characteristics. The local staff often knows what equipment is failing or not operating properly
due to design defects, age, or other factors. Keep in mind the overall energy goals. UESCs are
not meant to be used as “wish lists” for building managers, nor are they opportunities for
contractors to only choose the most profitable projects, leaving the less-economical work for
others. If that happens, the other work will never be completed, and installations will be
saddled with undesirable systems in their present condition.
a. The utility company’s costs and overhead will be greater for widely-scattered buildings
than it will be for facilities that are clustered together. Structure packages of buildings
to take maximum advantage of project economics. Include the less-desirable projects
with the more attractive projects, and ensure that the utility company takes them as a
package. Use the attractive savings from rapid payback projects, such as lighting
retrofits, to help support and subsidize the less-economical work, such as chiller and
cooling tower replacement.
b. Do not accept a preliminary report that addresses only technology that the utility
company elected to consider. If the BEM is interested in the viability of a specific
technology, and the UESC contractor states that the proposed technology is not
economical, request the contractor explain why in writing.
3. Use a multidisciplinary team to evaluate proposals. Consider the cost of maintenance and
repairs after equipment is installed and items such as the equipment’s noise level. Each ECP
should be evaluated on a life-cycle cost basis and energy-efficient or “Energy Star” equipment
should be used in the project where possible.
4. Where practicable, consider having building energy management or advance pulse interval
metering and load profile data recording devices installed as part of the contract. It is often
difficult to assign energy savings value to such equipment, so be prepared for these issues. The
importance of having advanced metering technology available for obtaining the best energy
procurement prices cannot be overstated.
5. Ensure a clear understanding with the UESC contractor regarding expectations and goals.
6. Keep the terms and provisions of the UESC TO as straightforward and clear as possible, without,
for example, all sorts of added O&M savings or escalators for cost of fuel and services. Look at
each ECM and determine how it contributes to the overall project, including its length of payoff
and the impact of its removal or inclusion on the overall project economics. Make the
appropriate business trade-offs and establish an optimal scope of work for the project. A project

Air Force Civil Engineer Center
UESC Playbook
39 | P a g e
may be modified later to include some O&M savings to accomplish a desired goal; however,
before making this kind of modification, make sure the O&M savings are real and can be
demonstrated to be obtainable.
7. Obtain load profiles and tour the building during peak energy use and make observations about
the operation of energy-using equipment. Determine if any equipment use or power loads can
be shifted to a non-peak period of energy use. If not, explore peak shaving, thermal load
shifting, and other means of saving energy and costs that could be used to cut expenses.
Consider using automated building management systems and timed-out electronic locks on
non-essential equipment so it cannot be operated during periods of peak demand.
8. The importance of coordination cannot be overstated. Pay attention to detail and follow-up on
everything. Be sure to involve installation engineering, AFCEC/CND, construction, contracting,
finance, and legal functions before awarding the TO.
9. Coordinate with the local utility service providers. If you are considering a project that would
allow you to go from a firm natural gas service rate to an interruptible service rate, check first to
make sure an interruptible service rate is available or that one can be obtained from another
service provider.
10. A common area of contention is the contract language addressing M&V issues. Make sure there
is a clear understanding and clear contract language addressing how much M&V is to be
performed, if required by the contract. Become familiar with the latest version of the IPMVP
and make use of the M&V protocols in your contract. The AFCEC Guide to M&V Activities
provides guidance and links to additional guidance on witnessing baseline, post-installation,
first-year, and annual M&V inspections and analyses, as well as commissioning installed
equipment. After construction completion and acceptance, the BEM and/or COTR will provide
the date of construction acceptance to AFCEC/CND.
11. All MFH ECPs should be thoroughly evaluated against future MFH renovations or new housing
initiatives for possible reduction or elimination of projected UESC savings. When ECM savings
are eliminated or greatly reduced, a buyout may be required. The installation programming
function should include the cost of the ECP buyout on DoD form (DD) 1391, Military
Construction Project Data. Before proceeding with any UESC project in MFH, coordinate with
the installation housing office and the Office of the Civil Engineer, Housing Division (A7/A7CH)
to identify and eliminate any potential conflict with current or planned MFH projects.

Air Force Civil Engineer Center
UESC Playbook
40 | P a g e
JUSTIFICATION AND APPROVAL FOR
OTHER THAN FULL AND OPEN COMPETITION
1.
Contracting Activity: (FACILITY NAME), ATTN:
(LOCATION)
2.
Description of Action: This action will establish a new Basic Ordering Agreement (BOA) between
the (SITE NAME AND UTILITY NAME) and will establish terms and conditions to receive energy
management services by issuing separate task orders or contracts. The task orders will be funded
by (FUNDS Account). The task orders will each be fixed- price type contracts.
3.
Description of Supplies/Services: The (UTILITY NAME) will provide energy and water conservation
and demand side management type projects and services to reduce energy consumption, directly
or indirectly reduce the peak period demand, and provide energy related operations,
maintenance, and repair services for natural gas, steam, electric power, water, or waste water at
(SITE NAME) facilities. The energy conservation projects will be amortized for a term not to exceed
10 years and the monthly payment will be included on the utility bill. The energy conservation
projects will be required to show a net overall savings and thus the cost of the projects will be
covered by the utility savings.
4.
Authority Cited:
a. Energy Policy Act of 2005 (Public Law 109-58 109th Congress)— Legislation regarding
energy-savings goals, directives and regulations.
b. Energy Savings Contracts and Activities (10 U.S.C. Section 2913) — Legislation regarding
energy-saving goals and plans at military facilities.
c. Water Conservation at Military Installations (10 U.S.C. Section 2866) — Legislation regarding
water-saving goals and plans at military facilities.
d. Federal Acquisition Regulations (FAR) 6.302-5—FAR, Subpart 6.3 – Other than Full and Open
Competition.
e. Executive Order 13693: Planning for Federal Sustainability in the Next Decade — Legislation
regarding greenhouse gas emissions reduction.
5.
Reason for Authority Cited
Energy Policy Act of 2005 (Public Law 109-58 109th Congress) directed the Architect of the Capitol
to develop and implement a cost-effective energy conservation and management plan for all
facilities administered by Congress. Agencies are authorized and encouraged to participate in
programs to increase energy efficiency and for water conservation or the management of
electricity demand conducted by gas, water, or electric utilities and generally available to
customers of such utilities.
The Energy Savings Contracts and Activities (10 U.S.C. Section 2913) states that The Secretary of
Defense shall permit and encourage each military department, Defense Agency, and other
instrumentality of the DoD to participate in programs conducted by any gas or electric utility for
the management of electricity demand or for energy conservation or by any utility for water
conservation activities.

Air Force Civil Engineer Center
UESC Playbook
41 | P a g e
The Water Conservation at Military Installations (10 USC Section 2866) states that The Secretary of
Defense shall permit and encourage each military department, Defense Agency, and other
instrumentality of the DoD to participate in programs conducted by a utility for the management
of water demand or for water conservation.
The Federal Acquisition Regulation (FAR) 6.302-5 provides that full and open competition is not
required where a statute; i.e., 10 U.S.C. 2913 (D) (3), expressly authorizes that an acquisition be
made from a specified source; i.e., the servicing gas or electric utility.
Executive Order 13693 states that agencies shall increase efficiency and improve their environmental
performance and encourages the use of utility energy-efficiency service contracts to meet the goals
set out in the order.
6.
Efforts to Obtain Competition: Not applicable. Per authorities cited above, these types of
agreements are limited to either the servicing gas or electric utilities, or both.
7.
Actions to Increase Competition: Not applicable. Per authorities cited above, these types of
agreements are limited to either the servicing gas or electric utilities, or both.
8.
Market Research: Not applicable. Per authorities cited above, these types of agreements are
limited to either the servicing gas or electric utilities, or both.
9.
Interested Sources: Not applicable. Per authorities cited above, these types of agreements are
limited to either the servicing gas or electric utilities, or both.
10.
Other Facts:
11.
Technical Certification: I certify that the supporting data under my cognizance which are included
in the justification are accurate and complete to the best of my knowledge and belief.
Name:
Title
Signature:
Date:
12.
Requirements Certification: I certify that the supporting data under my cognizance which
are included in the justification are accurate and complete to the best of my knowledge and
belief.
Name:
Title
Signature:
Date:
13.
Fair and Reasonable Cost Determination: I hereby determine that the anticipated cost to
the Government for contracts issued under this BOA action will be fair and reasonable. The
basis for this determination is
.
Name:
Title
Signature:
Date:

Air Force Civil Engineer Center
UESC Playbook
42 | P a g e
14.
Contracting Officer Certification: I certify that this justification is accurate and complete to
the best of my knowledge and belief.
Name:
Title
Signature:
Approval
Based on the foregoing justification, I hereby approve the establishment of the BOA with (Utility
name) authority for energy and water conservation and demand side management services on
another than full and open competition basis, pursuant to the authority of 10 U.S.C. 2913, and
the Energy Policy Act of 2005 (Public Law 109-58 109th Congress), subject to the availability of
funds, and provided that the services herein described have otherwise been authorized for
acquisition.
Name:______________________________
Title
Signature: __________________________
Date:

Air Force Civil Engineer
ESPC Playbook
43 | P a g e
Master Agreement Exhibit “C”
Contractor’s ID #_____________________(Optional)
Ordering Agency’s ID #_____________________(Optional)
Authorization for Energy Management Services Contract # ____________________
Ordering: _________________________________________________________________________
Agency: __________________________________________________________________________
Address: __________________________________________________________________________
Pursuant to Contract #____________________between the Contractor and the United States
Government and subject to all the provisions thereof, service to the United States Government under
such contract shall be rendered or modified as hereinafter stated. Contract Articles 2 and 4 shall be
followed for the initiation of service under this contract.
Premises to be served: ______________________________________________________________
_________________________________________________________________________________
Service Address: ___________________________________________________________________
_____________________________________________________________________________________
Nature of Service:
Preliminary Energy Audit
ECP Engineering & Design Study
Energy Conservation Project (ECP) Installation
Demand Side Management (DSM)
Project
ECP Feasibility Study
Special Facilities
Other (See below)
SERVICE HEREUNDER shall be provided consistent with the Contractor’s applicable tariffs, rates, rules,
regulations, riders, practices, and/or terms and conditions of service, as modified, amended or
supplemented by the Contractor and approved, to the extent required, by the Commission. (See Article
5 of this contract.)
Estimated Project Cost:
$_________________________
Capital Cost:
$_________________________
Percentage of Cost
Financed:
_________________________%
Rebate Amount (If
Applicable):
$_________________________
Simple Payback (Years)
______________________Years
Accounting and Appropriation Data: ___________________________________________________
_________________________________________________________________________________

Air Force Civil Engineer
UESC Playbook
44 | P a g e
Energy Conservation Measures:
Mechanical Systems Upgrades
Lighting
Steam Systems Upgrades
Renewables
Controls
Water Conservation
Cogeneration
Others
List of Attachments:
General Conditions
Historical Data
Certifications
Facility Site Plans
Design Specifications
Economic Analysis
Design Drawing
Special Requirements
ECP Feasibility Study
Payments Provisions
Utility Usage History
Commission Schedules
Remarks: _________________________________________________________________________
_________________________________________________________________________________
Accepted:
_______________________________________
______________________________________
(Ordering Agency)
(Contractor)
By: ____________________________________
By: ___________________________________
(Authorized Signature)
(Authorized Signature)
Title: __________________________________
Title: __________________________________
Date: __________________________________
Date: __________________________________
NOTE: A fully executed copy of this Authorization shall be transmitted by the Contracting Officer to
General Services Administration, WPE, Washington, DC 20407.

Air Force Civil Engineer
UESC Playbook
45 | P a g e
EMSA/MODEL AGREEMENT
AGREEMENT FOR ENERGY CONSERVATION AND DEMAND SIDE MANAGEMENT SERVICES BETWEEN
THE UNITED STATES OF AMERICA AND ________________________ UTILITY COMPANY
This Agreement for implementation of Energy Conservation Measures (ECMs) is entered into this day
of____________________, 20_____, by and between_____________________ Utility Company
(Utility) and the United States of America (Government), represented by the Contracting Officer
executing this Agreement. The signatories to this Agreement will be sometimes collectively referred to
as the “Parties” and individually as a “Party”. This Agreement (when signed by the Parties), any Task
Orders (TO) executed pursuant to this Agreement, and any other associated agreements shall
constitute the entire Contract between the Parties with respect to a particular ECM. A term or
condition contained in this Agreement may be amended at any time by mutual written agreement of
the Parties. However, termination, modification, or expiration of a term or condition shall not
retroactively affect TOs previously entered into under this Agreement. The Parties agree to the
following principles, concepts and procedures.
GENERAL CONDITIONS
GC.1 Purpose
The Government desires assistance in accomplishing ECMs at an Installation (may substitute at
all Installations within the Utility Company’s service area, to include [list the installations by
name] (hereinafter, Installations). The purpose of this Agreement is to facilitate the
implementation of ECMs through TOs. This Agreement sets forth the terms and conditions
under which subsequent TOs may be entered into between the Parties.
GC.2 Definitions
Terms used in this Agreement shall have the following definitions:
a. Acceptance: Written acceptance by the authorized representative of the Government of an
individual Phase or completed ECM pursuant to a TO.
b. Carrying Charge: For the purpose of this Agreement, Carrying Charge shall be an interest
rate applied to all ECM Costs incurred by the Utility until permanent financing is put in place
or the Government pays the ECM Cost. Accrued interest shall be considered an ECM Cost.
c. Contracting Officer: A Government official authorized to enter into, administer, and/or
terminate a contract on behalf of the Government, and who is authorized to make related
determinations and findings within the limits established pursuant to Government
regulations.
d. Contracting Officer Representative (COR) or Contracting Officer Technical Representative
(COTR): A local or project site representative of the Contracting Officer delegated specific
limited authority, as set forth in a formal delegation letter signed by the Contracting Officer,
for a given TO, including the feasibility study, engineering and design, operation and
maintenance, and/or implementation of one or more ECPs.
e. Energy Conservation Measure Cost (ECM Cost): The total cost may include, but is not
limited to the Work, finance charges and overhead and profit, for the feasibility study,
engineering and design, implementation and operation and maintenance of an ECM, less
any financial incentive or rebates, if provided by the Utility. Payment for completed ECMs

Air Force Civil Engineer
UESC Playbook
46 | P a g e
shall be calculated based upon the ECM Cost.
f. Energy Conservation Project (ECP): A specific project intended and designed to provide any
of the following: energy savings, demand reduction, efficiency improvements and water
conservation. ECPs are described in more detail in Section GC 17.
g. Occupied Period: Hours during which a facility or building is occupied or used in the normal
course of business.
h. Quality Assurance Evaluator (QAE): A functionally qualified person who evaluates or
inspects the contractor’s performance of service in accordance with the quality assurance
surveillance plan written specifically for the contracted service to be evaluated. The QAE
performs technical monitoring of contractor actions, is responsible for requesting products
and services through a government contract, and manages the day-to-day tasks of the
contract.
i. Quality Control: A management function whereby control of quality of raw or produced
material is exercised for the purpose of preventing production of defective material. For
purposes of this Agreement, quality control is those actions taken by a contractor to control
the production of outputs to ensure that they conform to the contract requirements.
j. Possession: When the Government takes beneficial occupancy of an ECP (Possession of an
ECP) or an ECM (Possession of an ECM).
k. Subcontractor: Any corporation, partnership or individual hired directly by the Utility to
perform a service or provide a product under this Agreement and TOs resulting from this
Agreement.
l. Task Order (TO): A binding contractual action entered into under this Agreement for the
feasibility study, engineering and design, implementation, and/or operation and
maintenance of, or any activity related to, an ECM. (A TO can also be identified as a
Delivery Order [D.O.].)
m. Termination Schedule: A schedule developed for each financed ECM specifying the lump
sum payment necessary at any time during the contract period following the initial
Government payment for the complete repayment of the ECM costs, including any finance
costs accrued to that point.
n. Work: All labor, materials, tools, equipment, services, transportation and/or other items
required for the completion of the ECM.
GC.3 Term
This Agreement shall have a term of years. This Agreement may be terminated in its entirety by
either Party upon 30 days’ written notice to the other Party. Thereafter, no new TOs shall be
entered into under this Agreement. Termination, modification or expiration of this Agreement
shall not affect in any way TOs previously entered into under this Agreement. This Agreement
shall be effective from the date it is signed by both Parties. In the event the Parties sign this
Agreement on different dates, then the effective date shall be the latter of the two dates.

Air Force Civil Engineer
UESC Playbook
47 | P a g e
GC.4 Services to be Provided by the Utility
The Utility shall provide preliminary audits, feasibility studies, engineering and design studies,
and all initial capital, labor, material, supplies and equipment to the Agreement. These services
may be ordered individually, as a group or in any combination under a single TO.
GC.5 Information
Subject to national security constraints and unless otherwise prohibited by law, the
Government shall provide the Utility with any information requested by the Utility to comply
with regulatory commission requirements.
GC.6 Relationship of Parties
The Government acknowledges the Utility and/or its Subcontractors shall each perform their
work as independent contractors and the Government shall have no direct control and
supervision of Utility or Subcontractor employees, who shall not be considered employees or
agents of the Government for any purpose. The Utility, in negotiations with its Subcontractors,
will ensure that the Government will be the direct beneficiary of any and all product and service
guarantees and warranties.
GC.7 Subcontractor Selection
The Utility may perform some or all of the Work under a TO itself or through Subcontractors.
When practical, the Utility shall competitively select Subcontractors for the purpose of
determining the reasonableness of Subcontractor prices. When competition is not practical,
price reasonableness may be determined by comparing proposed prices with those obtained for
the same or similar work, prices published in independent cost guides, published in competitive
price lists, or developed by independent sources.
Subcontractor selection shall be based on cost, experience, past performance, reliability, and
such other factors as the Utility may deem appropriate, as long as such factors are practicably
related to the Government's minimum needs. In no event may such services be provided by
Subcontractors listed as excluded from Federal Procurement Programs, which list is maintained
by GSA pursuant to 48 CFR 9.404. For any TO, the Utility may submit the names of proposed
Subcontractors to the Government Contracting Officer to ensure they are not excluded
pursuant to 48 C.F.R. 9.404.
GC.8 Authority of Contracting Officer
The Government’s Contracting Officer shall be the only Government official authorized to enter
into and/or modify a TO entered into under this Agreement.
GC.9 Ownership of Work Product
The Government may elect not to use the Utility to implement the ECM. If the Government so
elects, it will pay for any accepted work, including any equipment, completed studies, and
engineering and design work. Title to any work done by the Utility for the Government under a
TO shall become the property of the Government at the time of acceptance of the work.

Air Force Civil Engineer
UESC Playbook
48 | P a g e
GC.10 Responsibility for Operation and Maintenance
The operations and maintenance of the equipment installed pursuant to any TO executed
under this Agreement shall be the responsibility of the Utility during the payment term unless
otherwise provided in the TO.
GC.11 Government Projects
The Government shall not be restricted from implementing equipment installation,
construction projects and ECMs independent of work performed under this Agreement,
including installing new energy conservation equipment, removing existing energy consuming
equipment, or adding new energy consuming equipment. The Government will notify the
Utility prior to implementing projects that may affect ECMs under this Agreement.
GC.12 ECM Performance Verification
Each TO shall include procedures that are mutually agreeable to the parties to verify ECM
performance following installation.
GC.13 Emission Credits
All on-site Government emission credits earned by virtue of TOs entered into hereunder shall
be the property of the Government.
GC.14 Order of Precedence
The Government and Utility shall determine in this Agreement or subsequent TOs the
precedence given to the TO, this Agreement or other documents, exhibits and attachments, in
the event an inconsistency arises among these documents.
GC.15 Preliminary Audits
At the request of the Government or the Utility and upon the mutual consent of both parties,
the Utility will conduct, at no cost to the Government, an audit consisting of an on-site building
investigation and evaluation for a mutually agreeable facility to determine if any significant
energy conservation opportunities exist and whether further detailed energy analysis is
warranted. Government buildings/facilities plans will be made available upon request.
Requests for plans shall be made to the COR at least fifteen (15) calendar days in advance of
the audit start date. The Utility will provide a written report of the audit to the Government,
typically at no cost. The Utility will utilize historical building data, utility data, and information
obtained by the Utility to identify ECPs. Using this information, the Utility will generate a
prioritized list of recommendations, in sequence of implementation that are life-cycle cost-
effective and can be implemented in the facility being audited. The preliminary audit, to the
extent applicable, shall include, but not be limited to, the following information:
a.
Preliminary estimated energy and water savings.
b.
Preliminary estimated cost savings, including reduced maintenance costs.
c.
Current utility rates.
d.
Preliminary retrofit cost.
e.
Utility financial incentive/rebate, if any.
f.
Description of existing equipment.

Air Force Civil Engineer
UESC Playbook
49 | P a g e
g.
Description of the proposed retrofit equipment.
h.
Overview of the general environmental impact and potential hazardous wastes
identified through existing facility records, if any.
GC.16 ECM Proposal
After reviewing the preliminary audit, the Government may request a proposal from the
Utility, for the evaluation of an ECM. The Utility shall submit an ECM proposal, setting forth a
prioritized list of the recommended ECPs within the ECM, a preliminary estimate of the cost to
implement each ECP, the total costs for implementing the ECM (including estimated feasibility
study, engineering and design, and implementation costs), and estimated cost savings.
GC.17 Energy Conservation Projects
The Utility may propose ECMs which include one or more ECPs. ECPs that substitute one
energy type for another (e.g., natural gas in lieu of electricity) will not be considered for
implementation unless a net overall energy or cost reduction can be demonstrated based on
current market energy prices. Potential ECPs include, but are not limited to:
a. Interior and exterior lighting replacement.
b. Transformer replacement.
c. Lighting control improvements.
d. Motor replacement with high efficiency motor.
e. Construction of alternative generation or cogeneration facilities.
f. Boiler control improvements.
g. Packaged air conditioning unit replacement.
h. Cooling tower retrofit.
i. Economizer installation.
j. Energy management control system (EMCS) replacement/alteration.
k. Occupancy sensors.
l. LED exit sign installation.
m. Fans and pump replacement or impeller trimming.
n. Chiller retrofit.
o. Upgrade of natural gas-fired boilers with new controls (low NOX burners).
p. Solar domestic hot water system.
q. Solar air preheating system.
r. Steam trap maintenance and replacement.
s. Insulation installation.
t. Variable speed drive utilization.
u. Weatherization.

Air Force Civil Engineer
UESC Playbook
50 | P a g e
v. Window replacement.
w. Window coverings and awnings.
x. Reflective solar window tinting.
y. Fuel cell installation.
z. Photovoltaic system installation.
aa. Faucet replacement (infrared sensor).
bb. Replacement of air conditioning and heating unit with a heat pump.
cc. Addition of liquid refrigerant pump to a reciprocating air conditioning unit.
dd. High efficiency refrigerator replacement.
ee. High efficiency window air conditioner replacement.
ff. (Water conservation device installation (e.g., flow restrictors, low flow flush valves,
waterless urinals, horizontal axis washing machines).
gg. Installation, maintenance and operation of power quality and reliability measures including
UPS systems, back-up generators, emergency generators.
hh. Fuel switching technology.
ii. Infrared heating system.
jj. Heat pipe dehumidification.
kk. Flash bake commercial cooking.
ll. Thermal energy storage system.
mm. Operation, maintenance, modification and/or extension of utility distribution and collection
system.
nn. Training that will result in reduced energy costs.
oo. Power factor correction measures and equipment.
pp. Installation, maintenance and operation of standby propane facility.
qq. Installation, maintenance and operation of gas distribution system and associated
equipment.
rr. Water distribution system leak detection, and cost-effective repair.
ss. Any other ECP that is cost effective using the then-current DoD-prescribed procedures and
standards, and which encourages the use of renewable energy, reduces the Government’s
energy consumption or energy demand, or results in other energy infrastructure
improvements.
GC.17.1 ECM Restrictions
The Government shall not consider ECMs which include:
a.
Measures which could jeopardize existing agency missions.

Air Force Civil Engineer
UESC Playbook
51 | P a g e
b.
Measures which could jeopardize the operation of, or environmental
conditions of computers or computer rooms.
c.
Unless waived by the Contracting Officer, measures that would result in
increased water consumption (e.g., once-through fresh water cooling
systems).
d.
Measures which would violate any federal, state, or local laws or regulations.
e.
Measures which degrade performance or reliability of existing Government
equipment.
f.
Unless waived by the Contracting Officer, measures that would reduce
energy capacity currently reserved for future growth, mobilization needs,
safety, emergency back-up, etc.
g.
Measures that violate the then-current versions of the National Electric
Code, the National Electric Safety Code, the Uniform Building Code, or the
Uniform Mechanical Code.
h.
Utility-financed measures that do not result in savings in the base utility
expenditures sufficient to cover the project costs.
GC.17.2 Facility Performance Requirements of ECMs
ECMs proposed by the Utility shall conform to the following facility performance
standards:
a. Lighting levels shall meet the minimum requirements of the then-current
Illuminating Engineering Society (IES) Lighting Handbook.
b. Heating and cooling temperature levels shall meet Government design
standards.
c. ECMs shall permit flexible operation of energy systems for changes in
occupancy levels and scheduling of facilities. In proposing an ECM, the
Utility may assume the building function will remain constant unless
otherwise indicated by the Government.

Air Force Civil Engineer
UESC Playbook
52 | P a g e
GC.18 TOs
Following the evaluation of the ECM proposal, the Government may elect to execute a TO with
the Utility for the evaluation, implementation, or operation and maintenance of the ECM. If
requested by the Government, the Utility will provide or obtain financing on terms at least as
good as those available to customers in a comparable service class, or with a comparable risk
profile, considering the nature of the security interests to be granted, if any, and other
conditions affecting the cost of financing.
The TO may have five phases; Audit (when applicable), Feasibility Study Phase, Engineering and
Design Phase, Implementation Phase, and Operation and Maintenance Phase. Because the
extent of all the work is unlikely to be known at the time the TO is entered into, these phases
shall be line items under the TO, and shall be issued with an estimated Termination Schedule
at the time the TO is executed. However, work will not commence on a particular phase unless
and until a statement of work and a price for that phase have been agreed upon.
Following completion and acceptance of the Feasibility or Engineering and Design Phases, the
Government may elect to (i) pay the ECM Cost for each completed Phase within thirty (30)
calendar days of being invoiced; or (ii) defer payments for that Phase until the end of the next
Phase, at which time the Government shall pay the ECM Cost for each completed Phase within
thirty (30) calendar days of invoice; or (iii) include such amounts in the ECM Cost, if the
Government elects to proceed with the Implementation Phase. If the Government elects not
to proceed with the next Phase, it shall pay the Utility the ECM Cost for the prior completed
Phases, plus a Carrying Charge as negotiated by the parties in the TO. A decision to proceed or
not to proceed with the next Phase must be made within 60 days of receipt of a written
request from the Utility. Only the Contracting Officer shall be authorized to exercise the
Government’s option to proceed to the next Phase, and such exercise shall be provided in
writing within sixty (60) days of receipt of a statement of work and price. Government finance
payments for the Implementation Phase shall begin on the date of the first Utility bill following
the 30-day period after the Government takes possession of all or part of the ECM as provided
in FAR, Part 36, Subpart 36.511, and a satisfactory ECM Performance Verification as defined in
the TO and pursuant to Section GC.12 of this Agreement. The timing and amount of
Government payments of appropriated funds for the Operation and Maintenance Phase shall
be determined in the TO. The TO is subject to any legally-required Federal Acquisition
Regulations. Because services may vary widely from one TO to another, the Contracting
Officer will insure that the appropriate FAR clauses from the FAR matrix found at FAR, Part 52,
Subpart 52.301, are incorporated into any contract entered into by the parties for services
provided by the Utility under the TO.
GC.19 ECM Feasibility Study Phase
The TO shall set forth a scope of work feasible (the Feasibility Study). The TO shall specify the
terms for the completion of the Feasibility Study and establish a price for the Feasibility Study.
The Government will pay the Utility the agreed-upon price for the Feasibility Study in
accordance with the TO. If the Government elects to proceed with the Engineering and Design
Phase as set forth below in Paragraph GC.20, the cost of the Feasibility Study shall be rolled
into the Engineering and Design Phase ECM Cost. The Feasibility Study will provide, at a
minimum, the following information:

Air Force Civil Engineer
UESC Playbook
53 | P a g e
Technical Factors:
a.
Audits of energy consumption of existing equipment and facilities, including estimated
energy and cost savings, and proposed retrofit costs and financial incentives/rebates.
b.
Water audits of supply and utilization facilities, if specified by the Government.
c.
Equipment to be removed or replaced, and new equipment to be installed.
d.
Specifications, including catalog cuts, for new equipment. Specifications should include
(as applicable): power rating, estimated energy consumption, input/output, power
ratio, lighting level, and estimated equipment life.
e.
Operation and maintenance procedures required after ECM implementation (if
significantly altered by the ECM).
f.
Training that will be provided for the proper operation and maintenance of ECPs,
including details on how many hours of training will be provided and how many people
will be trained.
g.
Electrical and mechanical sketches for all ECPs that involve changes to existing systems
(sketches will not be required for ECPs involving only component replacement).
h.
Government support (e.g., minor changes in Government operation, movement of
equipment) required during implementation of the ECM.
i.
Utility interruptions needed for implementation of each ECP by type (gas, electricity,
water, etc.), extent (room number, entire building, etc.) and duration.
j.
Identification of potential adverse environmental effects.
k.
Any documentation required to comply with applicable environmental laws.
l.
Estimated construction time in calendar days, showing significant milestones.
m.
Estimated annual energy savings in kilowatt-hour and kilowatt demand of electricity,
dekatherms of natural gas, and cubic feet of water for the life of each ECP, including all
assumptions and detailed calculations showing how savings were determined.
n.
Estimated equipment life for each ECP.
o.
A proposed method to verify energy savings at the time of ECM Acceptance which shall
be subject to Government approval.
p.
Documentation that each proposed ECP has been recommended and selected without
regard to fuel source.
Cost Factors:
a.
Estimated annual operation costs (e.g., increased use of alternate fuel sources,
replacement filters) and increased maintenance costs (e.g., re-lamping with a higher
cost product).
b.
Total estimated ECM Cost to the Government.
c.
Estimated breakdown of financial incentives/rebates for each ECM (if any) in a format
mutually agreeable to the Parties.
Air Force Civil Engineer
UESC Playbook
54 | P a g e
d.
Estimated cost-of-money rate (percent).
e.
Estimated annual energy and operation and maintenance cost savings including details
on estimated annual savings for each area of savings, such as lighting, controls, motors
and transformers.
f.
Estimated breakdown of implementation costs for each area of energy savings, such as
lighting, controls, motors and transformers.
g.
Estimated costs for replacing existing components and installing new
components/systems, listed separately.
h.
Estimated unit costs for major components and systems.
i.
An estimated life cycle cost analysis prepared in accordance with the then- current
edition of the Energy Prices and Discount Factors for Life-Cycle-Cost Analysis, published
as the annual supplement to the National Institute of Standards and Technology (NIST)
Handbook 135.
GC.20 ECM Engineering and Design Phase
After evaluation and acceptance of the feasibility study, the Government may elect to proceed
with the Engineering and Design Phase. Prior to proceeding, the Parties shall agree upon a
statement of work for all engineering and design services necessary for the implementation of
a particular ECM, a time frame for completion of the work, and a price or cost cap for
engineering and design work for the ECM. If the Government elects to proceed with the
Implementation Phase as set forth below, the cost of the engineering and design work shall be
rolled into the total ECM Cost. This TO shall include an estimated amortization schedule for
the ECM.
GC.20.1 Verification of Floor Plans
The Utility will verify the accuracy of any floor plans provided by the Government.
GC.20.2 Government Design Review
TOs shall permit adequate time for Government review of engineering and design
work at 35% and 95% design completion, or at any other stage, as negotiated in the
TO.
GC.20.3 Site Plans
If proposed ECMs require installation outside existing buildings or structures, a site
plan showing recommended siting of ECMs shall be prepared for Government review
and approval. Site plans shall be submitted as part of the Utility's proposal. It is
recommended that the Utility propose alternate sites for review in case the primary
site is unavailable.
GC.20.4 ECM Implementation Proposal
Upon completion and Acceptance of the Engineering and Design Phase, the Utility
will submit to the Government an ECM implementation proposal (the “Proposal”). If
requested by the Contracting Officer, the Utility will be required to present a briefing
to the Government explaining the Proposal. At a minimum, the Proposal shall

Air Force Civil Engineer
UESC Playbook
55 | P a g e
include all pertinent technical and cost factors listed in paragraph GC.19 of this
Agreement, plus a copy of subcontractor(s) bid(s). The Proposal shall also set forth
negotiated pricing criteria that describe the method for determining the prices to be
paid to the Utility for supplies or services. The Government shall evaluate the
Proposal for technical soundness and price reasonableness. If the Government elects
to proceed with the ECM, the Utility and Government shall agree upon a complete
scope of work with specifications, time for performance, ECM Cost, source and cost
of capital or financing, payment terms, amortization schedule, and final Termination
Schedule. If the Contracting Officer deems it appropriate, the Utility will provide
acceptable performance and payment bonds.
GC.21 ECM Implementation Phase
The Utility shall perform work in accordance with the TO. The following provisions shall apply
to ECM implementation work performed pursuant to TOs executed under this Agreement,
unless exceptions are provided in the TO.
GC.21.1 Pre-Work Requirements
Prior to commencing ECM implementation Work on a TO, the Utility shall meet with
the Contracting Officer or COR at a time mutually agreeable to the Utility and the
Contracting Officer, to discuss and develop mutual understandings relative to safety,
scheduling, performance, obtaining necessary permits, and administration of the
Implementation Phase. Prior to commencement of on-site work, written approval of
the following shall be obtained from the Contracting Officer by the Utility:
a.
The utility's proposed implementation schedule, indicating the installation
period and time required for delivery of equipment.
b.
Evidence that the required insurance has been obtained.
GC.21.2 Interruptions
The Utility shall arrange on-site work to minimize interference with normal
Government operation. All interruptions shall be made outside occupied periods
whenever possible and coordinated with the Contracting Officer or COR. The Utility
shall endeavor to keep the duration of utility interruptions to a minimum. Requests
for utility outages shall be submitted for approval, in writing, as specified in the TO.
The request shall include the approximate duration, date, time, and reason for the
interruption. Utility interruptions include, but are not necessarily limited to, the
following systems:
a. electrical
b. natural gas
c. sewer
d. steam
e. water
f. telephone
g. computer cables

Air Force Civil Engineer
UESC Playbook
56 | P a g e
GC.21.3 Construction Documentation
The Utility shall provide construction drawings and specifications, certified by a
registered engineer or architect, as applicable, to ensure compliance with all
applicable federal, state and local codes and regulations as required by individual
TOs.
GC.21.4 Standardization of Materials
All materials proposed to be installed pursuant to this Agreement shall be readily
commercially available, and as similar in form, fit, and function to each other as is
practicable to allow efficient provisioning of replacement parts.
GC.21.5 Water Conservation Measures
The Utility will consider water conservation in all ECMs. The Utility will obtain
rebates from the local water utility if available. Rebates, if any, shall be applied to
the cost of the project.
GC.21.6 Operation and Maintenance Manuals
At the time of Government Acceptance of a completed ECM, the Utility shall furnish,
for the equipment specified, operation and maintenance manuals and recommended
spare parts lists identifying components adequate for competitive supply
procurement for operation and maintenance of ECM equipment. The operation and
maintenance manuals shall include maintenance schedules for all equipment. The
scope of each manual shall be agreed upon in the TO.
GC.21.7 Government Personnel Training for ECPs
The Utility shall train Government personnel, as required, to operate, maintain, and
repair ECM equipment and systems. The date and time of training shall normally be
coordinated with the Contracting Officer or COR prior to Acceptance of the ECM. The
cost for such training shall be included in the ECM Cost.
GC.21.8 As-Built Drawings
Within 45 calendar days after Government Acceptance of each installed ECM, the
Utility shall submit as-built drawings to the Contracting Officer or COR. Drawings will
not be required for component replacement. Drawings shall include at a minimum:
a.
Installation (i.e., form, fit, and attachment details) of the interface between
ECM equipment and existing Government equipment.
b.
Location and rating of installed equipment on building floor plans.
GC.21.9 Installation
The Utility will arrange for the installation of approved ECMs and construction
oversight and verify that the designed and specified energy efficiency equipment
and/or system modifications are properly supplied or installed in a manner that will
give the intended long term demand and energy reductions. The Utility will select
Subcontractors in accordance with paragraph GC.7 above.

Air Force Civil Engineer
UESC Playbook
57 | P a g e
GC.22 Operation and Maintenance Phase
The Government may elect to have the Utility perform the operation and
maintenance on part or all of the ECM. Before exercising its option for this Phase,
the Government and Utility shall agree upon a complete scope of work with
specifications, schedules, warranties, and cost.
GC.23 Required FAR Clauses
The following FAR clauses are required to be included in any contract with the
Government:
52.203-3, Gratuities; 52.203-5, Covenant Against Contingent Fees; 52.203-7, Anti-
Kickback Procedures; 52.222-3, Convict Labor; 52.222-25, Affirmative Action
Compliance; 52.222-26, Equal Opportunity; 52.223-6, Drug Free Workplace; 52.233-1,
Disputes.
WARRANTIES AND REMEDIES
WR.1 Warranties
The Utility shall pass through to the Government all warranties on equipment installed pursuant
to a TO. In addition, the Utility shall provide, from the date of Acceptance or Government
Possession of an ECP, whichever is earlier, a one- year comprehensive wrap-around warranty
guaranteeing that the equipment installed shall perform in accordance with the specifications
agreed upon between Government and Utility, as set forth in the applicable TO. In the event
the Utility provides O&M services, a separate warranty will be negotiated for such services, in
accordance with FAR Part 52, Subpart 52.246-20.
WR.2 No Other Warranties
The warranties set forth in WR.1 are exclusive and in lieu of all other warranties. The Utility
makes no other representations or warranties of any kind with respect to the services and
products it provides pursuant to this Agreement and subsequent TOs. The Utility does not
guarantee any level of energy or water savings or cost reductions.
WR.3 Utility Limitation of Liability
The Utility shall not be liable for any special, incidental, indirect, or consequential damages,
connected with or resulting from the performance or non-performance of work under this
Agreement or subsequent TOs. In addition, the Utility shall not be liable under its warranty to
the extent that damages are caused by Government negligence.
WR.4 Utility Default
The Government and Utility agree that Utility default provisions will be governed by those FAR
clauses applicable to specific circumstances. A determination of applicable FAR default clauses
will be made by the Contracting Officer for a specific TO.
WR.5 Prompt Payment
As required in FAR, Part 32, Subpart 32.903, the Government shall promptly pay ECM utility
bills. Late payments shall accrue interest as provided in FAR, Part 32, Subpart 32.907.

Air Force Civil Engineer
UESC Playbook
58 | P a g e
WR.6 Disputes
Disputes that arise under this Agreement and subsequent TOs shall be governed by the
applicable dispute provisions found at FAR, Part 33, Subpart 33.2.
WR.7 Differing Site Conditions
In the event site conditions differ materially from those contained in the TO, additional costs
incurred by the Utility due to the differing conditions shall be negotiated prior to work, and the
ECM Cost shall be increased to reflect an equitable adjustment as permitted in FAR, Part 36,
Subpart 36.502.
WR.8 Suspension of Work
In the event work is delayed, suspended, or stopped by the Government, FAR, Part 42, Subpart
42.13 shall apply.
FINANCING AND PAYMENT PROVISIONS
FP.1 Energy Savings and Financing
It is intended that the life-cycle energy and related savings achieved from the implementation
of an ECM funded or financed in a UESC project will produce financial savings to the
Government that are equal to or greater than the cost of implementing the ECM, including the
cost of financing, if applicable, provided under this Agreement. The payment term shall be in
accordance with Agency policy following current legislation, legal opinions, and Agency
guidance.
FP.2 Financial Incentives, Rebates, and Design Assistance
The Utility will provide to the Government the same financial incentives, rebates, design review,
goods, services, and/or any other assistance provided without charge that is generally available
to customers of a similar rate class or size. Incentives that may be available are to be identified
in the preliminary audit report provided according to paragraph GC.15 and the ECM
implementation proposal provided according to paragraph GC.20.4.
If rebates are available and have been applied for by the Government and such funds have been
set aside, then the Utility shall provide a separate letter of agreement clarifying timelines and
responsibilities of both parties and guaranteeing rebates and other incentives from the Utility to
the Government.
The Utility shall also be responsible for determining the source, value, and availability of any
applicable financial incentives to the project offered by the state and other jurisdictions in
which the facility is located, and if the value of the incentives exceeds the administrative costs
to be incurred by the Utility or the Government in acquiring such incentives.
The Utility shall be responsible for coordinating with the Agency Contracting Officer regarding
preparation of any and all documentation required to apply for any such applicable financial
incentives and to effectively apply such incentives to the capital cost of the project.
Rebate disbursement options include:
Option 1: The Utility shall apply rebates to the next payment due to reduce capital cost
of the project.

Air Force Civil Engineer
UESC Playbook
59 | P a g e
Option 2: Where allowable by the Public Utility Commission, the Government may
assign rebate to a third party to reduce the construction costs and thereby reduce the
total amount financed.
Option 3: Rebates may be accepted as a credit on the utility bill.
FP.3 Calculation of Payment
Payment for accepted ECMs shall be equal to the ECM Cost amortized over a negotiated term.
In accordance with 10 U.S.C. Section 2912, the cost of financing, if any, for any completed ECM
shall be recovered under terms and conditions no less favorable than those for others in the
same customer class. Monthly payments will commence on the date of the first Utility bill
following the 30-day period after the date the Government takes Possession of the ECM, and
after ECM Performance Verification Testing, as required by GC.12 and negotiated in the TO, is
satisfactorily completed.
FP.4 Buydown
The Government reserves the right at any time following Acceptance, but prior to final
payment, to buy down the outstanding TO payments without penalty by giving thirty (30) days’
written notice to the Utility. Upon such buydown, the Government shall pay to the Utility a
negotiated amount to include an additional finance charge based on an indexed formula, which
reduces the financier’s risk and reduces the cost of buydown to the Agency, or provide a
termination schedule. Monthly payments will continue at the same level, but the term of ECM
financing will be shortened to reflect the amount of the buydown payments.
FP.5 Pre-Acceptance Buyout
If the Government desires to terminate a TO for any reason (including, without limitation, for
convenience) prior to Acceptance, the Government may do so by giving written notice to the
Utility thirty (30) days prior to the effective date of such termination. The Government shall pay
to the Utility a negotiated amount to include an additional finance charge based on an indexed
formula, which reduces the financier’s risk and reduces the cost of buyout to the Agency, or
provide a termination schedule which will be described in Attachment A of the TO. If a
termination occurs for the convenience of the Government, the amount payable pursuant to
this paragraph shall be deemed as an allowable cost under FAR Part 17 and FAR Part 52,
Subpart 52.249-2.
FP.6 Post-Acceptance Buyout
In the event the Government desires to terminate a TO for any reason (including, without
limitation, for convenience) after Acceptance, the Government may do so by giving written
notice to the Utility 30 days prior to the effective date of such termination. The Government
shall pay to the Utility a negotiated amount to include an additional finance charge based on an
indexed formula, which reduces the financier’s risk and reduces the cost of buyout to the
Agency, or provide a termination schedule which will be described in Attachment B of the TO. If
a termination occurs for the convenience of the Government, the amount payable pursuant to
this paragraph shall be deemed as an allowable cost under FAR Part 17 and FAR Part 52,
Subpart 52.249-2.

Air Force Civil Engineer
UESC Playbook
60 | P a g e
FP.7 Assignment of Claims
Government payments under each TO executed pursuant to this Agreement may be assigned
pursuant to FAR Part 52, Subpart 52.232.23, “Assignment of Claims”. Any bank, trust company,
or other financing institution that participates in financing an ECM shall not be considered a
Subcontractor of the Utility. Any “Assignment of Claims” must comply with the provisions of
FAR Part 32, Subpart 32.8.
FP.8 Novation
The Parties agree that if, subsequent to the execution of this Agreement, it should become
necessary, or desirable, to execute a “Novation Agreement”, said Novation Agreement will
comply with the provisions of FAR Part 42, Subpart 42.12 and will be in the form as provided at
FAR Part 42, Subpart 42.1204.
SPECIAL REQUIREMENTS
SR.1 Environmental Protection
The Utility shall comply with all applicable federal, state, and local laws, regulations, and
standards regarding environmental protection ("Environmental Laws"). All environmental
protection matters shall be coordinated with the Contracting Officer or designated
representative. The Utility shall immediately notify the Contracting Officer of, and immediately
clean up, in accordance with all federal, state and local laws and regulations, all oil spills,
hazardous wastes (as defined at 42 U.S.C. §9601), and hazardous materials (as defined at 49 CFR
Part 172), collectively referred to as Hazardous Materials”, resulting from its operation on
Government property in connection with the implementation of ECMs. The Utility shall comply
with the instructions of the Government with respect to avoidance of conditions that create a
nuisance or create conditions that may be hazardous to the health of military or civilian
personnel.
SR.2 Environmental Permits
Unless otherwise specified, the Utility shall provide, at its expense, all required environmental
permits and/or permit applications necessary to comply with all applicable federal, state, and
local requirements prior to implementing any ECM in the performance of a TO executed
pursuant to this Agreement. If any such permit or permit application requires the signature or
other cooperation of the Government as owner/operator of the property, the Government
agrees to cooperate with the Utility in obtaining the necessary permit or permit application.
SR.3 Handling and Disposal of Hazardous Materials
Notwithstanding the provisions of the FAR Part 52, Subparts 52.236-2 “Differing Site
Conditions" and 52.236-3 "Site Investigations and Conditions Affecting Work," the Government
understands and agrees that (i) the Utility has not inspected, and will not inspect, the project
site in connection with a proposed ECM for the purpose of detecting the presence of pre-
existing Hazardous Materials that relate to an ECM or any project site; and (ii) the Government
shall retain sole responsibility for the proper identification, removal, transport, and disposal of
any fixtures, components thereof, or other equipment or substances incidentally containing
pre-existing Hazardous Materials, except as specifically agreed to by the Utility pursuant to
paragraphs SR.4 and SR.5 (below).

Air Force Civil Engineer
UESC Playbook
61 | P a g e
If the Utility, during performance of the work under a TO executed pursuant to this Agreement,
has reason to believe that it has encountered or detected the presence of pre-existing
Hazardous Materials, the Utility shall stop work and shall notify the Government. The
Government will evaluate the site conditions and notify the contractor of the results of this
evaluation. The Utility shall not be required to recommence work until this situation has been
resolved. Any delay resulting therefrom shall be grounds to request an increase in the ECM
Cost to the extent that such delay increases ECM costs.
SR.4 Asbestos and Lead-Based Paint
To the extent provided for in a TO executed pursuant to this Agreement, in connection with the
implementation of any ECM, the Utility may agree to remove pre-existing asbestos-containing
material or lead-based paint, incidental to implementation of an ECM. However, unless the
Utility explicitly agrees in said TO to perform any portion of the testing, removal, or abatement
of the pre-existing asbestos or lead-based paint as part of the scope of work for any ECM, and
unless the TO specifically references this paragraph SR.4, the Government shall be deemed to
be solely responsible as provided for in paragraph SR.3.
If the Utility, in the course of ECM implementation, disturbs suspected lead-based paint or
asbestos-containing material, the Utility may propose to the Government that the Utility will
perform any portion of the testing, removal, or abatement of the lead-based paint or asbestos-
containing material. Said proposal will include the requested increase in the ECM cost on
account of such additional work. The Utility will not commence work involving additional cost
without approval of the Contracting Officer. Provisions of paragraph SR.3 shall apply in the
absence of an agreement to the contrary. If the Utility agrees to include any portion of the
testing, removal, or abatement of the asbestos within the scope of work for an ECM
implemented as described previously in this section, the hazardous waste manifests or other
shipping papers shall identify the Government as the sole generator of the Hazardous Materials.
SR.5 Refrigerants, Fluorescent Tubes, and Ballasts
To the extent provided for in a TO executed pursuant to this Agreement in connection with the
implementation of any ECM, the Utility shall remove and/or dispose of all ozone-depleting
refrigerants, fluorescent tubes, and fluorescent magnetic core and coil ballasts incidental to an
ECM to the Hazardous Materials (HAZMAT) disposal site on the installation. If there is no
HAZMAT disposal site on the installation, the above HAZMAT will be disposed of in accordance
with all applicable federal, state, and local laws and regulations, provided however, that the
hazardous waste manifests or other shipping papers shall identify the Government as the sole
generator of the Hazardous Materials.
SR.6 Ozone-Depleting Refrigerants
All ozone-depleting (ODC) refrigerants will remain the property of the installation. The
Contractor will collect all ODCs and provide them to the installation in accordance with the
procedures in the TO.

Air Force Civil Engineer
UESC Playbook
62 | P a g e
Sample - Basic Statement of Work (SOW) for the “Letter of Interest”
The SOW for the “Letter of Interest” should be a broad overview and not specific. We want the Utility
to draw on their experience and expertise to review and analyze the current energy situation at your
location and provide an overview of all ECMs they recommend to improve energy conservation. The
utility will provide specifics in the Preliminary Analysis and the Investment Grade Audit or Feasibility
Study. Provide general areas you wish to explore and let the experts at the utility analyze the situation
and recommend a course of action. You can drop an ECM or ask the utility to add something at this
stage.
SOW
Joint Base (JB) Outstanding intends to enter into a UESC contract for energy conservation measures
(ECMs) which enhances or improves the bases energy usage. Various upgrades or improvements of all
types are being considered. Among them we are looking at controls, heating, ventilating and air
conditioning upgrades, high efficiency motors, piping insulation upgrade, lighting controls and water
conservation measures.
These upgrades will result in energy cost savings to JB Outstanding. In accordance with UESC
procedures, the utility will arrange for third party financing to be paid back within 10 years with the
energy savings.
Insulation: Furnish and install insulating jackets on domestic hot water heaters (electric and natural gas
fired units). Repair damaged or missing insulation on heating hot water and chilled water lines.
Insulation shall be rotary glass fiber insulation with a service jacket. Repair damaged or missing
insulation on refrigerant lines. Insulation shall be a minimum of 1.5 inches thick expanded closed cell
foam with vapor barrier and service jacket.
Condenser Coil Improvements: Furnish and apply protective corrosion inhibitor on air-cooled
condensers. The material shall be Adsil Microguard or an approved equivalent. The material shall be
installed in accordance with manufacturer’s recommendations.
Controls: Furnish and install programmable thermostats. The new thermostat shall be internet
compatible and integrated with all currently installed EMCS. Furnish and install an air quality sensor to
establish demand controlled ventilation.
HVAC Upgrades: Furnish and install new split system and roof mounted heating and cooling units to
replace aging units. The new units shall match existing capacities and have minimum efficiencies of
12.1 EER and 13.4 EER for the split systems and roof mounted units respectively. Furnish and install
new variable frequency drives on pump motors. Furnish and install new air-cooled condensing units.
High Efficiency Motors: Furnish and install new premium efficiency, inverter rated motors on air
handler fan motors.
Lighting and Lighting Controls: Furnish and install new linear fluorescent light and electronic ballasts
replacing existing incandescent and aging fluorescent lighting. Furnish and install new high bay
fluorescent T5 lamps replacing high intensity discharge lighting in the main shop area. Furnish and
install new wall and ceiling mounted occupancy sensors.

Air Force Civil Engineer
UESC Playbook
63 | P a g e
UESC Task Order (TO) Sample
TO # ____________________
GSA Area Wide GS-xxx
This TO is entered into by and between ____________________ (Utility) and ____________________
(Agency) for implementation of certain Energy Conservation Measures (ECMs) as described herein at
____________________ (installation/site).
All terms and conditions of the GSA Areawide Public Utility Contract apply to this TO, unless modified
by the paragraphs below. In the event of a conflict between the requirements of the GSA Areawide
Public Utility Contract and those of this TO, the requirements of this TO shall prevail.
1. Purpose (Note: change as required to cover your project purpose)
The intent of this project is to meet the objective of ____________________ (Agency) energy goals
and missions by increasing lighting efficiency, replacing and enhancing outdated building controls,
and reducing chilled water costs including the cost of fuel used to produce chilled water. It is
anticipated that energy will be optimized in each covered building to achieve
____________________ reduction in ____________________ and ____________________
reduction in energy intensity and advanced metering.
2. Scope of Work (Note: Add your scope here. This is a sample SOW)
The Contractor shall arrange for all initial capital for third-party financing for this project. The
Contractor shall provide all labor, material, equipment, and supervision to implement the ECMs
described below. The project work includes interfacing and connecting to existing facilities and
systems. Upon completion, inspection, and acceptance of Line Items 1, 2, and 3, including testing,
training, and delivery of all O&M manuals as required herein, ____________________ (Agency)
agrees to purchase the work described in this TO.
The Contractor shall provide Performance Assurance of all work associated with this TO for the first
12 months after acceptance of all Line Items.
All work for Line Items 1 and 2 described below shall be performed in accordance with Attachment
TO-1 – “Agency/Site/M&O Guidance.”

Air Force Civil Engineer
UESC Playbook
64 | P a g e
Line Item 1: Lighting Upgrades
Provide design and installation services to complete lighting upgrades in the following buildings:
ECM
Building #
Building location/name
ECM-1
ECM-2
ECM-3
ECM-4
ECM-6
ECM-8
ECM-9
ECM-10
ECM-11
ECM-12
This work described in the following documents:
Attachment TO-2 Lighting Statement of Work
Attachment TO-3 Lighting Equipment Specifications
Line Item 2: Controls Upgrades
Provide design and installation services to complete controls upgrades in the following buildings:
ECM #
Building #
Building Name
ECM X
Building X
Ipsum
ECM X
Building X
Ipsum
ECM X
Building X
Ipsum
ECM X
Building X
Ipsum
This work is described in the following documents:
Attachment TO-4 Controls Statement of Work
Attachment TO-5 Controls Equipment Specifications
Line Item 3: Chiller Plant Upgrade
Provide installation services to complete the Chiller Plant Upgrade (ECM X). This work is described
in the following documents:
Attachment TO-6 Specifications for Chiller Plant
Attachment TO-7 Construction Drawings (Bid Package X)
The Operations and Maintenance (O&M) contractor will provide Human Machine Interface (HMI)
screen modifications and additions, Programmable Logic Controller (PLC) and HMI programming,
including loading, debugging and checkout of the control programs, subsequent to the Contractor’s
completion of installation and confirmation of control wiring continuity. Control Panels as shown
on drawings ____________________ through ____________________ are existing, except as noted
on the drawings. ControlNet and redundancy connections to the panels are by the Contractor.

Air Force Civil Engineer
UESC Playbook
65 | P a g e
Line Item 4: Performance Assurance
A Performance Assurance Plan will be implemented to verify that the new equipment is operating
to specified operational standards and generating savings when compared to the existing systems
that were replaced. The Performance Assurance Plan is provided in Attachment TO-8. The
Performance Assurance process shall commence as specified in Attachment TO-8 for a period of 12
months after final acceptance by ____________________ (Agency) of Line Items 1, 2 and 3. At that
point, the Performance Assurance process will be turned over to the Agency.
Performance Assurance for Line Item 1: Lighting Upgrades, shall be based on the Calculation
Methodology included in Attachment 2. This work is described in Attachment 8: Performance
Assurance under Detailed Procedures – Lighting Upgrade.
Performance Assurance for Line Item 2: Controls Upgrades, shall be based on the Calculation
Methodology included in Attachment 4. This work is described in Attachment 8: Performance
Assurance, under Detailed Procedures – Energy Management System and Attachment 9: ECM
Calculations.
Performance Assurance for Line Item 3: Chiller Plant Upgrade, shall be performed in accordance
with Attachment 8: Performance Assurance, under Detailed Procedures – Chiller Plant Upgrade.
It is anticipated that energy will be optimized in each covered building to achieve 29% reduction in
Greenhouse Gas (GHG) and 31% reduction in energy intensity and advanced metering. However,
the Contractor does not guarantee that the ECMs installed pursuant to this TO will result in energy
savings to the Government, and the Government expressly recognizes and agrees that unrealized
energy savings are not a basis for failing to make payment as required by Paragraph 6.D.
3. SUBMITTALS
Required submittals are described in Attachment TO-14.
4. TERM
This TO shall be effective from the date that the Award document is signed by both Parties. In the
event the Parties sign this TO on different dates, the effective date shall be the latter of the two
dates.
This TO shall have a term of 10 years, consisting of an anticipated 18 month design and construction
period and a 9 year payment period. The term, not including the construction period, may not
exceed 10 years.
A. Notice to Proceed
The Contractor shall not commence work on the ____________________ (installation/site)
until ___________________ (Agency) issues a Notice to Proceed. The Notice to Proceed is
issued on receipt of all required bonds and insurance documents and on approval of the
Contractor’s Worker Safety & Health Program under 10 CFR 851 and the Contractor’s Health
& Safety Plan.
(Note: The Agency may want to specify in the TO the number of days allowed for submittal
of Performance and Payment bonds and the Certificate of Insurance, typically between 10
to 15 days after the date of award. The number of days allowed for submittal of the Safety
documents could be specified as well.)

Air Force Civil Engineer
UESC Playbook
66 | P a g e
The “Notice to Proceed” is issued with an “Agency/Site/M&O Safety Management” Form
which must be completed by every Subcontractor to be used in performance of this TO and
submitted to ____________________ (Agency) in accordance with Attachment TO-14,
Agency Reporting & Submittal Requirements.
Within 15 days after the Contractor receives the “Notice to Proceed,” the Contractor will
commence work. Prior to receipt of the “Notice to Proceed” the Contractor may prepare
and submit required submissions and may order materials and equipment that do not
require prior Agency approval.
B. Performance Schedule
The detailed performance schedule is contained in Attachment 15.
5. ACCEPTANCE
The Contractor shall request an inspection by the Agency as the Contractor completes Line Items 1,
2 and 3. The ____________________ (Agency) will inspect the work within 14 calendar days of the
request, and complete a “Certificate of Substantial Completion” for each Line Item. “Substantial
completion” means that the facilities are usable and the greater majority of the work is installed
and acceptable.
Any discrepancies or “punch list” items shall be described in writing. If the ____________________
(Agency) indicates acceptance, takes possession of the equipment, or uses the equipment for
beneficial use, this shall be construed as acceptance of the work that is completed, with the items
on the punch list representing work that is not accepted. The Contractor shall complete or correct
all items on the punch list within 30 calendar days and shall present the Agency with
documentation indicating completion. The Agency will indicate final acceptance in writing within
14 calendar days after completion of the punch list items. If the Agency fails to accept or reject the
completed punch list items within 14 calendar days after written notice from the Contractor
indicating completion, then the Agency shall be deemed to have accepted the work. Following
Agency acceptance of the work, the Contractor shall not be liable to the Agency for any liability, loss
or damage caused or alleged to be caused directly or indirectly by the equipment or by any
inadequacy thereof or deficiency or defect therein, except as provided in FAR 52.246-21, Warranty
(see Attachment A-1, FAR Clauses).
6. PRICE, BILLING, FINANCING, AND PAYMENT
A. Price
The total firm fixed price for execution of the project defined above is $xx,xxx,xxx.
B. Financing
____________________ (Agency) will not spend capital investment dollars. The Contractor
will finance the entire project price. The Contractor shall make all arrangements necessary
to deliver the project as described above and will arrange for financing during the design
and construction period. The total financed amount, including construction financing and
financing fees, will be $xx,xxx,xxx. Repayment will commence with the initial invoice
submitted in ____________________ (Month)__________ (Year) and payment due in
____________________ (Month)__________ (Year) as described in Paragraph D below.

Air Force Civil Engineer
UESC Playbook
67 | P a g e
C. Financial Incentives, Rebates, and Design Assistance
Note: The Agency may want to consider discussing incentives and rebates with the Utility
and negotiate taking any available rebates as a reduction in TO price, or having the amount
of the rebates identified and applied as a reduction to the installation’s Utility bill.
The Contractor will provide to the Agency the same financial incentives, rebates, design
review, goods, services, and/or any other assistance provided without charge, that is
generally available to customers of a similar rate class or size.
If rebates are available and have been applied for by the Agency and such funds have been
set aside, then the Contractor shall provide a separate letter clarifying timelines and
responsibilities of both parties and guaranteeing rebates and other incentives from the
Contractor to the Agency.
The Contractor, through its Subcontractor(s), is responsible for determining the source,
value, and availability of any applicable financial incentives to the project offered by the
state and others in which the ____________________ (installation/site) is located, and if
the value of the incentives exceeds the administrative costs to be incurred by the
Contractor or __________________ (Agency) in acquiring such incentives.
The Contractor, through its Subcontractor(s), is responsible for coordinating with the CO for
the preparation of all documentations required to apply for any such applicable financial
incentives.
The preferred method for applying financial rebates/incentives is to have the
rebates/incentives disbursed directly to the ESCO and applied to reduce the total price. If
this is not possible an alternative process must be considered in accordance with current
Government policy.
D. Payment
Following final acceptance of Line Items 1, 2, and 3 by ____________________ (Agency),
payments will be made annually in accordance with the Payment and Termination Schedule
(Attachment 16). The Contractor or its designee will submit an invoice for the first payment,
which will be due and payable within 30 days from final acceptance of Line Items 1, 2, and 3.
The Contractor will submit invoices annually thereafter. Each successive annual payment
will be due on the anniversary of the due date of the first payment.
It is the Contractor’s responsibility to arrange for an adjustment to the due date for the first
payment in the event of Contractor-caused delays in final acceptance of Line Items 1, 2, and
3. There shall be no additional cost to the Government or deviation from the dollar amount
or number of payments in the TO. Delays by ____________________ (Agency) that prevent
final acceptance and payment by the billing date will result in adjustment of the financing
cost of the project. Following the Agency’s acceptance, the Agency’s obligation to pay all of
the payments due hereunder is absolute and unconditional, and will not be entitled to any
abatement, reduction, set-off, counterclaim, defense, interruption, deferment, recoupment,
or deduction with respect to any payments due hereunder, including without limitation any
reduction for unrealized energy savings.
The Contractor enters into this TO as the franchised natural gas supplier to
____________________ (Agency). If the Agency terminates the natural gas service

Air Force Civil Engineer
UESC Playbook
68 | P a g e
agreement with the Contractor prior to the date of completing repayment for this project,
they will either continue to make the annual payment in accordance with the Payment and
Termination Liability Schedule or shall pay the Termination Amount identified in such
Payment and Termination Liability Schedule.
Upon final payment, the Contractor shall execute a release of all claims against the Agency
under this TO.
E. Buydown
____________________ (Agency) retains the right, at any time following final acceptance of
Line Items 1, 2, and 3, but prior to final payment, to buy down the outstanding TO payments
without penalty by giving the Contractor 30 days prior written notice. Upon such buydown,
the Agency will pay to the Contractor the pro rata termination amount specified in the
Payment and Termination Liability Schedule (Attachment 16). Payments will continue at the
same level but the term of ECM financing will be shortened to reflect the amount of the
buydown payments. Any such additional sums shall be used to reduce the outstanding
Termination Amount, maintaining the payments and shortening the payback period. Each
time an additional payment is made, the Payment and Termination Liability Schedule will be
recalculated to show the new payback period. ____________________ (Agency)
acknowledges and agrees that the payment of such amounts are reasonable and allowable
costs with respect to the TO.
F. Pre-Acceptance Buyout
In the event that ____________________ (Agency) desires to terminate this TO for any
reason (including, without limitation, for convenience) prior to final acceptance of Line
Items 1, 2 and 3, they may do so by giving written notice to the Contractor 30 days prior to
the effective date of such termination. ____________________ (Agency) will pay to the
Contractor an amount negotiated between the Agency and the Contractor that is equal to
the value of work verified as completed at the time of termination, plus allowable costs
related to such work. If a termination occurs for the convenience of the Government, the
amount payable pursuant to this paragraph shall be deemed as an allowable cost under FAR
Part 17 and Part 52, Subpart 52.249-2.
Note: The Agency should be aware that the terms in E and F above have in some cases
caused the lender to increase the interest rate or the termination liability amount to cover
the risk of such buydowns and buyouts.
G. Post-Acceptance Buyout
In the event that ____________________ (Agency) desires to terminate this TO for any
reason (including, without limitation, for convenience) after final acceptance of Line Items 1,
2 and 3, the Agency may do so by giving written notice to the Contractor 30 days prior to
the effective date of such termination. The Agency shall pay to the Contractor a
termination amount in accordance with the Payment and Termination Liability Schedule
(Attachment 16).
7. ASSIGNMENT OF CLAIMS
The Contractor may assign payments due from ____________________ (Agency) under this TO
pursuant to FAR 52.232-23, Assignment of Claims. The Agency agrees to complete any necessary

Air Force Civil Engineer
UESC Playbook
69 | P a g e
forms which acknowledge that assignment. Any bank, trust company or other financing institution
that participates in financing an ECM shall not be considered a Subcontractor of the Utility. Any
assignment of claims must comply with the provisions of FAR Part 32, Subpart 32.8.
8. WAGE RATES AND LABOR STANDARDS
The attached wage determination from the U.S. Secretary of Labor shall be implemented in
accordance with the statutes for labor standards requirements for contracts over $2,000.00
involving construction. (Attachment B– U.S. Department of Labor General Decision)
The following labor standards provisions apply to work performed under this TO as if they were set
forth herein in their entirety. For more information on clauses incorporated by reference see
Attachment A-1 – Terms and Conditions.
FAR Ref
Title
Date
52.222-6
Davis-Bacon Act
Jul 2005
52.222-7
Withholding of Funds
Feb 1988
52.222-8
Payrolls and Basic Records
Jun 2010
52.222-9
Apprentices and Trainees
Jul 2005
52.222-10
Compliance with Copeland Act Requirements
Feb 1988
52.222-11
Subcontracts (Labor Standards)
Jul 2005
52.222-12
Contract Termination – Debarment
Feb 1988
52.222-13
Compliance with Davis-Bacon and Related Act Regulations
Feb 1988
52.222-14
Disputes Concerning Labor Standards
Feb 1988
52.222-15
Certification of Eligibility
Feb 1988
52.222-23
Notice of Requirement for Affirmative Action to Ensure Equal Employment
Opportunity for Construction*
Feb 1999
52.222-27
Affirmative Action Compliance Requirements for Construction
Feb 1999
Note: Ensure all FAR clauses/references are reviewed and included in the TO.
Note: For purposes of the Notice, the “covered area” is ____________________ (County, State).
The goals for minority and female participation, expressed in percentage terms for the Contractor’s
aggregate workforce in each trade on all construction work in the covered area are as follows:
1. Goals for Minority Participation for Each Trade 5.8%
2. Goals for Female Participation for Each Trade 6.9%
These goals are applicable to all of the Contractor's construction work performed in the covered
area. If the Contractor performs construction work in a geographical area located outside of the
covered area, the Contractor shall apply the goals established for the geographical area where the
work is actually performed. Goals are published periodically in the Federal Register in notice form,
and these notices may be obtained from any Office of Federal Contract Compliance Programs office.
9. SAFETY REQUIREMENTS
All work under this TO shall be conducted in a safe manner and shall comply with the requirements
of Agency requirements. Furthermore, in performing work under this TO, the Contractor will

Air Force Civil Engineer
UESC Playbook
70 | P a g e
perform work in a manner that ensures adequate protection for employees, the public, and the
environment, and will be accountable for the safe performance of the work. The Contractor will
exercise a degree of care proportionate with the work and the associated hazards. The Contractor
will ensure that management of environment, safety and health (ES&H) functions and activities is
an integral and visible part of its planning and execution processes while performing work at the
site.
With respect to performance of any portion of the work under this TO that is performed on the
____________________ (installation/site), the Contractor agrees to comply with all State and
Federal ES&H regulations, and with all ES&H requirements of M&O, the site operating contractor.
Agency requirements include, but are not limited to, compliance with all OSHA standards, as well as
with any other ES&H reporting requirements that the CO may require.
Other specific requirements relative to safety are as follows:
A. Prior to commencing work, the Contractor shall meet with the COR’s to agree on
administration of the safety program.
B. The Contractor’s workplace may be inspected periodically for OSHA violations. Abatement
of violations is the Contractor’s responsibility. The Contractor will provide assistance to
Agency and Federal/State OSHA inspectors if a complaint is filed. Any fines levied on the
Contractor due to safety/health violations shall be paid promptly by the Contractor.
C. In accordance with FAR 52.236-13, Accident Prevention, as set forth in Paragraph 12 herein,
“Additional Provisions”, the Contractor is required to report to the CO all accidents within
24 hours of occurrence.
D. In accordance with FAR 52.236-13, Accident Prevention, as set forth in Paragraph 12 herein,
“Additional Provisions”, the Contractor shall submit to the COR a full report of damage to
Government property and equipment by Contractor employees or subcontractors, at any
tier within 24 hours of occurrence.
10. BONDS
Bonds are typically required within 15 days after award of the task order, since the contract price
will have been negotiated.
A. Within 30 days of TO award or acceptance of the Design and Construction Package,
whichever is later, the Contractor will furnish a certified copy and duplicate of a
performance bond (SF 25), with the project financier as co-beneficiary along with the
Agency. The performance bond shall be in a penal sum equal to 100% of the total firm fixed
price for all ECMs. The Contractor will furnish a payment bond (SF25A) in duplicate. The
payment bond shall be in a penal sum equal to 100% of the total firm fixed for all ECMs.
B. The performance and payment bonds will remain in effect during the total implementation
period for all ECMs. The ECM implementation period shall include all time required for
installation, testing, measuring initial performance, and Agency acceptance of all contractor-
installed ECMs. The payment bond shall be released upon receipt of satisfactory evidence
that all subcontractors, laborers, etc., have been paid in full.
C. The Contractor will not file any mechanics liens against the Agency for the TO projects and
this requirement shall flow down to all subcontractors. Therefore, the payment bond will

Air Force Civil Engineer
UESC Playbook
71 | P a g e
secure the Contractor’s obligations for payment of laborers, suppliers, and all
subcontractors.
11. INSURANCE
In accordance with FAR 52.228-5, “Insurance – Work on a Government Installation”, which is
incorporated herein by reference, the Contractor will, at no cost to the Government, maintain
policies providing the following insurance protection, which insurance will apply to all operations
of the Contractor hereunder and employees of the Contractor engaged therein.
A. Worker’s Compensation Coverage, as provided in the Worker's Compensation Law of the
State having jurisdiction, including occupational disease coverage for limits of $1,000,000
per person in any one case and additional Employees Liability of $1,000,000 per occurrence.
B. General Liability Insurance, with limits of $1,000,000/$2,000,000 for bodily injury liability
and $100,000 for property damage liability in the comprehensive liability form.
C. Automobile Liability Insurance, with limits of $250,000/500,000 for bodily injury liability and
$50,000 for property damage liability in the comprehensive policy form.
The Contractor will provide an endorsement to its liability policies naming the U.S. Government
and “Agency/Site/M&O” as additional insureds.
The Contractor will furnish the CO a certificate of insurance to show compliance with this
paragraph. The insurance certificate will be submitted within 14 days after award and prior to
issuance of a “Notice to Proceed”. The Contractor will also ensure that the certificate states that
the insurance carrier(s) will give ____________________ (Agency) 30 days prior written notice if
there is any cancellation or material change in such policies. The Contractor will ensure that the
certificates are kept up to date during the period of contract performance.
The Contractor agrees to insert the substance of this clause in all subcontracts hereunder at any
tier where work will be performed on the ____________________ (installation/site).
The Contractor may purchase such additional or other insurance protection, as it may deem
necessary, at its own expense.
Nothing herein shall relieve the Contractor of or limit the Contractor’s liability for losses and
damages to person or property as a result of its operations. The Contractor will indemnify, and
hold ____________________ (Agency), and any person acting on behalf of the Agency, harmless
from any and all liability, including attorneys’ fees and legal costs, associated with or resulting from
the Contractor’s operations under this TO.
12. CONTRACT ADMINISTRATION
The Contracting Officer (CO) is:
Name:
Email:
Telephone:
Fax:

Air Force Civil Engineer
UESC Playbook
72 | P a g e
The CO is the primary point of contact for all matters regarding this TO except technical/project
matters.
The Contracting Officer Representative (COR) is:
Name:
Email:
Telephone:
Fax:
The COR is the focal point for all technical/project matters related to this Task Order.
13. JOB COORDINATION
Note: Only use this M&O verbiage if you have an M&O contractor performing maintenance on
any affected equipment/ECM. The paragraph can be modified to include the authority section for
the CO, COR, Safety Officer.
____________________ (M&O Contractor) operates the ____________________
(installation/site) under Contract # __________ with ____________________ (Agency). Job
coordination for installation of the ECMs on the installation/site will be done through M&O’s
Facilities Improvements Office (FIO). After the “Notice to Proceed” as described in Paragraph 4.A
above, all day-to-day coordination regarding construction management from the M&O to the
Contractor will come from FIO in writing.
The Agency Contracting Office is the sole entity that can modify the TO or initiate change orders.
All direction to the Contractor must come from the Agency CO. The Agency COR will provide
answers for questions and/or issues involving construction only and has no authority to make any
changes whatsoever to the TO. The Safety Officer shall provide answers for questions and/or
issues involving safety only and has no authority to make any changes whatsoever to the TO. All
correspondence, including but not limited to: notifications, changes, or direction referred to in
this TO or other documents between the Contractor, Agency and M&O will be in writing. All
correspondence from the Contractor is to be addressed to the Agency CO; with copies to the
Agency COR and the M&O FIO.
The M&O FIO is responsible for documenting and reporting the daily monitoring and inspection of
all work activities at the site to the Agency COR. These responsibilities include and are not limited
to:
A. The assurance that all installed materials and systems meet the level of quality as
defined in the TO.
B. Ensuring that all work is completed in accordance with the Contractor’s ES&H program
and the ES&H provisions of this TO.
FIO is the first line of contact with the Contractor’s field organization on matters involving safety
and interface with installation/site operations. The Agency CO is responsible for all contracting
matters. The Agency Contracting Officer Technical Representative (COTR) is the first line of
contact between the Agency and the Contractor for all technical matters. The Contractor is to
take direction from no other sources within the Agency or M&O organization.

Air Force Civil Engineer
UESC Playbook
73 | P a g e
14. REPRESENTATIONS, CERTIFICATIONS, AND OTHER STATEMENTS OF OFFERORS
The Representations, Certifications, and Other Statements of Offerors completed by the
Contractor and certified in the Online Representation and Certifications Application (ORCA)
System, are hereby incorporated by reference.
15. SMALL BUSINESS SUBCONTRACTING PLAN
The Small Business Subcontracting Plan submitted and filed by Contractor and incorporated in the
Areawide Contract, including any annual plans, are hereby incorporated by reference.
16. TITLE TO, AND RESPONSIBILITY FOR, CONTRACTOR-INSTALLED EQUIPMENT
Title to all equipment installed by the Contractor will be vested in the Government after
acceptance by the Government, and will not relieve the Contractor’s responsibility for ECM
performance.
17. CONTRACTOR’S RESPONSIBILITIES
The Contractor is responsible for all damages to persons or property that occur as a result of the
Contractor’s fault or negligence. The Contractor is responsible for all materials delivered and
work performed until completion and acceptance of the entire work, except for any completed
unit of work, which may have been accepted under this TO. The Contractor’s responsibility
applies to activities of the Contractor, its agents, lower-tier subcontractors, and employees.
18. GENERAL PROVISIONS
The following general provisions are incorporated in and made a part of this TO:
Attachment
Title
A-1
Terms and Conditions – Federal Acquisition Regulation Clauses
A-2
Terms and Conditions – Agency Clauses
A-3
Terms and Conditions – Site-Specific Clauses
B
Wage Determination (ref)
C
ETL 13-10
19. LIST OF REFERENCED ATTACHMENTS (add or delete as desired by installation)
The following attachments referenced herein are incorporated in and made a part of this TO:
Attachment #
Description
TO-1
Agency/site/M&O guidance
TO-2
Lighting Statement of Work
TO-3
Lighting Specifications
TO-4
Controls Statement of Work
TO-5
Controls Specifications
TO-6
Specifications for Chiller Plant Upgrade – Identification of Specifications & Bid Package
TO-7
Chiller Construction Drawings
TO-8
Performance Assurance Plan

Air Force Civil Engineer
UESC Playbook
74 | P a g e
TO-9
ECM Calculations
TO-10
Lighting Calculation Spreadsheets
TO-11
Controls Calculation Spreadsheets
TO-12
Chiller Calculation Spreadsheet
TO-13
Measurement & Verification
TO-14
Agency Reporting & Submittal Requirements
TO-15
Performance Schedule (TBD)
TO-16
Payment & Termination Liability Schedule (TBD)

Air Force Civil Engineer
UESC Playbook
75 | P a g e
DEPARTMENT OF THE AIR FORCE
HEADQUARTERS UNITED STATES AIR FORCE
WASHINGTON, DC
AFGM2017-32-01
2 February 2017
MEMORANDUM FOR DISTRIBUTION C
MAJCOMs/FOAs/DRUs
FROM: AF/A4C
1800 Air Force Pentagon Washington
DC 20330-1800
SUBJECT: Air Force Guidance Memorandum, Civil Engineer Control Systems Cybersecurity
ACCESSIBILITY: Publication is available for downloading on the e-Publishing web site at
www.e-Publishing.af.mil.
RELEASABILITY: There are no releasability restrictions on this publication.
By Order of the Secretary of the Air Force, this Air Force Guidance Memorandum
(AFGM) immediately establishes cybersecurity policy for civil engineer (CE)-owned or operated
control systems (CS). This Memorandum details the unique operational characteristics of Air
Force (AF) CS, outlines roles and responsibilities for managing risk under the Risk Management
Framework, and implements guidance and policy for securing and mitigating risk to AF CE CS.
This Guidance Memorandum supersedes Engineering Technical Letter 11-1 and applies
to all military and civilian Air Force personnel, the Air Force Reserve and the Air National
Guard. Compliance with this Memorandum is mandatory. To the extent its directions are
inconsistent with other Air Force (AF) publications, the information herein prevails, IAW AFI
33-360, Publications and Forms Management.
Ensure all records created as a result of processes prescribed in this publication are
maintained IAW AFMAN 33-363, Management of Records, and disposed of IAW Air Force
Records Information Management System (AFRIMS) Records Disposition Schedule (RDS).
This Memorandum becomes void after one year from the date of this Memorandum, or upon the
publication of a new Instruction permanently establishing this guidance, whichever is earlier.
JOHN B. COOPER, Lieutenant General, USAF
DCS/Logistics, Engineering & Force Protection
2 Attachments:
1.
Control Systems Background
2.
Cybersecurity Policy for Civil Engineer Control Systems
AFGM Page 1

Air Force Civil Engineer
UESC Playbook
76 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
Attachment 1
CONTROL SYSTEMS BACKGROUND
A1.1. Control Systems Overview.
A1.1.1. Control systems are integrated hardware and software designed to monitor, or monitor and
control, the operation of equipment, infrastructure, or associated devices. Control Air Force Civil Engineer
UESC Playbook
systems consist of a combination of technology (computers, human-machine interfaces (HMI))
and control components (electrical switches, mechanical actuators, environmental sensors) that
act together upon underlying mechanical or electrical equipment to achieve a physical objective
(the transport of matter or energy, control of a dynamic process, or maintenance of a secure and
comfortable work environment, etc.) Generally, these special-purpose systems regulate the flow
of electricity, fluids, gases, air, traffic, and even people.
CS are comprised of several sub-groups of systems including building automation systems and
industrial control systems (ICS). Various categories of ICS include supervisory control and data
acquisition (SCADA), distributed control systems (DCS), programmable logic controllers (PLC),
intelligent HMI modules, and other dedicated CS configurations often found in the industrial sector
and support critical infrastructure.
A1.1.1.1. SCADA systems are highly distributed systems used to monitor and control
geographically-dispersed assets where centralized data acquisition, control, and status
reporting are critical to system operation. SCADA systems are used in distribution systems
such as water distribution and wastewater collection systems, oil and natural gas pipelines,
electrical power grids, and railway transportation systems.
A1.1.1.2. DCS are used to control industrial processes such as electrical power generation,
oil refineries, water/wastewater treatment, manufacturing production, and materiel
distribution. DCS are integrated control architectures that provide supervisory-level control
and integration over subsystems responsible for local process control.
A1.1.1.3. PLC are proprietary processor-based, solid-state devices found in almost all
industrial equipment and processes to provide logic algorithms for connected input and
output devices. They can vary in sophistication from simple, stand-alone microcontrollers to
sophisticated, multi-processor controllers that provide advanced motion control, network
capability, error detection, diagnostics, process recovery, and fail-safe redundancy. While
PLC are components of DCS and SCADA systems, they are often the solitary control device
for smaller CS configurations used to provide operational control of separate processes.
A1.1.1.4. A list of AF CE-owned CS can be referred to in section A1.2.
A1.1.2. Throughout the Air Force, CS are typically used to monitor and/or control electricity;
facility heating, ventilation, and air conditioning (HVAC); interior and exterior lighting; water and
wastewater; natural gas distribution; certain intrusion detection systems and fire/life safety
systems (such as fire alarm reporting systems and fire suppression systems). CS are a critical part
of automation and are used extensively to optimize resources supporting nearly all aspects of Air
Force core mission areas.
AFGM Page 2

Air Force Civil Engineer
UESC Playbook
77 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A1.1.3. Historically, CE CS were neither automated nor networked. Devices used for monitoring or
control had no computing resources, and those that were digitized typically used proprietary
protocols and PLCs rather than full computer control. As controllers became interconnected, they
were not designed with traditional IT system and security considerations, as they were expected to
operate as isolated systems running on their own dedicated network with proprietary
communication protocols and specialized hardware and software. This intentional separation from
AF-wide traditional IT (e.g., e-mail, web access, networked printing, or remote access) allowed CS
to be easily connected, open and accessible, highly stable, and readily serviced.
Today, however, CS are designed using standard platforms, operating systems, network protocols,
and access controls commonly found in traditional IT systems. The ever- increasing connectedness
of CS allows for greater operational capabilities, efficiencies, and automation. However, this
integration also introduces new vulnerabilities that expose both the CS and the underlying
network to threats.
A1.1.4. Special precautions must be taken when introducing IT security controls and solutions to
CS environments because of the unique ways CS communicate and operate. Interconnections
between CS and organizational networks/business systems are a particular point of focus for
security and should be carefully considered. In all cases, security solutions must be tailored to the
specific CS environment and verified to ensure their impact to the CS is not detrimental to a CS’s
operation.
A1.1.5. CS can have long life spans (often exceeding 20 years) and can be comprised of technology
that suffers rapid obsolescence. This longevity introduces several issues. Most importantly, older
hardware and software may no longer be supported by the manufacturer. Companies can go out of
business or terminate their support for an installed product. Because of this, patches and forward
support for compatibility with new operating systems may no longer be available as new
vulnerabilities are discovered.
A1.1.6. In the traditional IT domain, where data is the preeminent priority, cyber defenders often
focus on preventing the disclosure of information to unauthorized individuals or processes.
Consequently, confidentiality tends to be the most important attribute among the three
properties of the confidentiality – integrity – availability (CIA) triad. However, with CS, it is
paramount to actively manage or monitor physical processes and maintain high availability and
positive control of the system. Therefore, availability and integrity of the CS take precedent over
confidentiality. It is this difference in cybersecurity priorities that impacts what security controls
and procedures are appropriate to implement for CS compared with those of traditional IT.
A1.1.7. The goal of securing CS components is to prevent, deter, detect, and mitigate the
introduction, exposure, and propagation of malicious software to, within, and from the CS as
much as possible. Therefore, security controls such as intrusion detection software, antivirus
software and file integrity checking software should be utilized to the fullest extent technically
feasible. However, it is also recognized that CS have unique performance and reliability
requirements and often use operating systems and applications that may be considered
unconventional to typical IT processes. Furthermore, the goals of safety and efficiency
sometimes conflict with security in the design and operation of control systems.
AFGM Page 3

Air Force Civil Engineer
UESC Playbook
78 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A1.1.8. CS and their real-time operating systems are often resource-constrained systems that do
not include typical contemporary IT security capabilities. Legacy systems are often lacking
resources common on modern IT systems. Many systems may not have desired features including
encryption capabilities, error logging, and password protection.
Indiscriminate use of IT security practices in CS may cause availability and timing disruptions.
There may not be computing resources available on CS components to retrofit these systems with
current security capabilities. Adding resources or features may not be possible.
A1.2. Scope. AF CE-owned CS include, but are not limited to, the following types of systems (including
all points, devices, control panels, means of connectivity, software, controllers, computer workstations,
servers, etc.):
A1.2.1. SCADA Systems
A1.2.1.1. Protective relays (microprocessor-based)
A1.2.1.2. Cathodic protection systems
A1.2.1.3. Natural gas distribution systems
A1.2.1.4. Power generation systems, including renewable systems
A1.2.1.5. Water/wastewater distribution systems
A1.2.1.6. Water/waste treatment systems
A1.2.2. Building Automation Systems (BAS)
A1.2.2.1. Energy Management Control Systems (EMCS)
A1.2.2.2. Advanced Meter Reading Systems (AMRS)
A1.2.2.3. Interior/exterior lighting controls
A1.2.3. Fire/Life Safety systems
A1.2.3.1. Fire Alarm Reporting Systems (FARS)
A1.2.3.2. Fire Suppression Systems (FSS)
A1.2.3.3. Facility Mass Notifications Systems
A1.2.4. Utility Monitoring and Control Systems (UMCS)
A1.2.4.1. Electrical distribution systems
A1.2.4.2. Generator monitoring systems
A1.2.5. Airfield Control Systems
A1.2.5.1. Airfield Lighting Control Systems (ALCS)
A1.2.5.2. Aircraft Arresting Systems (AAS)
A1.2.5.3. Runway Ice Detection Systems (RIDS)
A1.2.5.4. Bird abatement systems
A1.2.5.5. Ramp lighting control systems
A1.2.6. Vehicle Traffic controls
A1.2.6.1. Drop-arm barriers
A1.2.6.2. Pop-up barriers
A1.2.6.3. Traffic signal systems
A1.2.7. CE-maintained Intrusion Detection Systems
AFGM Page 4

Air Force Civil Engineer
UESC Playbook
79 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
Attachment 2
CYBERSECURITY POLICY FOR CIVIL ENGINEER CONTROL SYSTEMS
A2.1. Applicability. Due to the unique nature of CS, there is a need for specific control system guidance
and policies to help secure, maintain, and provide mission assurance of the critical infrastructure and
missions these systems support.
A CS is considered operational technology (OT), which is IT adapted to directly monitor and/or control
physical devices, processes and events where availability is the primary operational concern.
Accordingly, OT is more sensitive to the application of cybersecurity measures and controls that can
affect its availability. The Authorizing Official (AO) assigned to the CS boundary is responsible for
managing the risk for OT and may tailor controls to balance security and availability.
Air Force CE CS consist of OT classified as either Real Property Installed Equipment (RPIE) or
Non-RPIE Equipment. Figure 1 represents the elements that comprise CS in addition to OT’s
affiliation with the Platform IT (PIT) category of Air Force IT, defined further in AFI 17-101.
Referencing AFI 17-101, Platforms and Non-RPIE Equipment would generally be classified as
types of “PIT Systems” or “PIT Subsystems.”
Figure 1: Categorization of AF IT and CS
Attachment 2 outlines some of the defensive cybersecurity policies to be adhered to throughout the life
cycle of CS operating on AF installations. These policies are not meant to supersede any established
Federal, Department of Defense (DoD) or AF policy, but instead are intended to supplement existing
policy (such as DoDI 8500.01) and DoD’s Risk Management Framework (RMF) (outlined in DoDI 8510.01)
by providing guidance on security measures.
1
From Unified Facilities Criteria 4-010-06, Cybersecurity of Facility-Related Control Systems, Appendix E
2
Equipment in CS Architecture Level 5 is considered Non-RPIE Equipment when installed as part of a CS enclave.
3
CS Architecture Level 2B is considered an Information System as a Base Area Network (BAN) access switch and
Non-RPIE Equipment when part of a CS in Levels 0-2.
AFGM Page 5

Air Force Civil Engineer
UESC Playbook
80 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.2. Standard Level of Cybersecurity Service. At a minimum, the standard cybersecurity level of
service for base CE organizations is to be compliant with this AFGM for the CE-owned, operated, or
managed on-base assets supporting identified Defense Critical Infrastructure (DCI) missions and
capabilities. These procedures and guidelines should also be followed in a prioritized manner for the
remaining infrastructure under CE’s ICS PIT AO boundary (introduced in section A2.4.1).
A2.3. Installations’ CS Inventory. Installations will conduct and maintain accurate inventories of all CS
under the purview of CE. The installations’ CS inventory should provide thorough awareness of existing
systems, their interconnections, and their link to the mission or function they serve. For more
information on the recommended content and CS inventory specificity, see NIST SP 800-82.
A2.3.1. The CS inventory at installations shall include both hardware (physical devices and
systems) and software (communications platforms and applications) down to Topology Tier Level
2 at a minimum. A diagram of CS topology, its associated levels and components are defined and
exemplified in Unified Facilities Criteria 4-010-06, Cybersecurity of Facility-Related Control
Systems, Appendix E.
A2.3.2. The inventory shall include descriptions of CS-supported assets and infrastructure, and
whether the CS supports DCI as determined by A3OA or locally-derived mission critical capabilities.
Actual names of critical infrastructure, Task Critical Assets (TCA), or Defense Critical Assets (DCA)
should not be listed in an unclassified environment. TCA and DCA are defined as part of the
Defense Critical Infrastructure Program (DCIP) detailed in DoD Manual 3020.45, Volume 1.
A2.4. Risk Management Framework. The AF CE community shall adhere to the NIST ICS guidelines
(NIST SP 800-82), DoD RMF guidance outlined in DoDI 8510.01, and subsequent AF RMF policy (AFI 17-
101) to the greatest extent possible in order to sufficiently manage the life cycle cybersecurity risk of
CS.
A2.4.1. RMF Roles and Responsibilities. The transition from the DoD Information Assurance
Certification and Accreditation Process (DIACAP) to RMF warrants changes in workflow, roles and
responsibilities to accompany the shift from compliance-based accreditation to a risk-based
approach to securing assets. To comply with RMF, the AF Chief, Information Dominance and Chief
Information Officer (SAF/CIO A6) has appointed the Deputy Director of Civil Engineers (A4C-2) as
the AO for CE ICS PIT. Upon appointment by the AF Chief Information Security Officer, the Air
Force Civil Engineer Center (AFCEC) Operations Directorate Director will be the Security Control
Assessor (SCA) for CE ICS PIT.
During the phase-in period to RMF, the role of Information System Security Manger (ISSM) will
be temporarily assumed by AFCEC. The roles of the Information System Owner (ISO) and the
Program Manager (PM) for CE CS will be performed, in the short- term, by the owning base’s
Deputy Base Civil Engineer (BCE). Funding for contract support to assume these roles and
responsibilities is currently in the process of being approved through the FY18 budgeting
process. The specific roles and responsibilities for performing continuous monitoring, as
required by RMF, are forthcoming. See section A2.17 for further details regarding FY18
funding and the transition plan to meet CS cybersecurity protocol expectations.
AFGM Page 6

Air Force Civil Engineer
UESC Playbook
81 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.4.2. Preliminary Baseline Classification. For assistance with determining the Potential Impact
Values for the RMF “Step 1 - Categorize System” process, please reference the EI&E PIT Control
System Master List located on the RMF Knowledge Service portal. The list provides a baseline
confidentiality – integrity – availability impact rating for various AF control systems. This baseline
rating is considered the minimum impact value for a given system based on its mission criticality.
A2.5. Acquisitions. Because a CS is related to the facility being constructed and tailored to the mission it
supports, acquisition and procurement of CS is currently a decentralized process in the AF. Until there is
a centralized CS Program Management Office (PMO) able to adequately conduct CS lifecycle
management, the CE community needs to collaborate with the Acquisitions community to accurately
define security requirements and prioritize CS acquisitions with cybersecurity measures already
incorporated into the design of the asset. Additionally, it is recommended to incorporate the best
practices from the Department of Homeland Security (DHS)’s Cyber Security Procurement Language for
Control Systems document into all future procurement and maintenance contracts.
A2.6. Segregated CS Network Environment. The AFCEC Operations Directorate’s Civil Engineer
Maintenance Inspection Repair Team (CEMIRT) Division will assist Base CE squadrons to establish an
accredited CS enclave in order to segregate CS and CS traffic from the base area network (BAN). The
enclave configuration will provide a defendable and monitored space protecting both the CS from
network vulnerabilities and the network from CS vulnerabilities. CS should be operated either as stand-
alone systems (no network connectivity), on an air-gapped network, or on a CS enclave. CS should not
be directly connected to the Internet through either static or dial-up connections except as described in
sections A2.9 and A2.16.
A2.7. Information Protection and Mission Assurance. A modified list of cybersecurity best practices to
follow and frequently review is listed below. Additionally, the technical references listed in section
A2.19 provide comprehensive procedures to follow for information protection and mission assurance.
A2.7.1. Apply security techniques such as encryption and/or cryptographic hashes to CS data
storage and communications where determined appropriate.
A2.7.2. Frequent backups of CS data should be conducted, maintained, and properly stored. It is
recommended to store copies of data and “golden image” configuration backups in a secure
location for business continuity and disaster recovery.
A2.7.3. When a CS is no longer required, the ISO should take appropriate action to ensure the
system and its data is properly disposed IAW established procedures detailed in NIST SP 800-
53r4 and NIST SP 800-82r2.
A2.7.4. Ensure response plans (Incident Response/Business Continuity) and recovery plans
(Incident Recovery/Disaster Recovery) are in place and managed IAW NIST SP 800-82.
AFGM Page 7

Air Force Civil Engineer
UESC Playbook
82 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.7.4.1. Response and recovery plans should contain specific tactics, techniques, and
procedures (TTP) for when adversarial activity is detected. Such a plan may include disconnecting
all Internet connections, running a properly scoped search for malware, disabling affected user
accounts, isolating suspect systems, and an immediate 100 percent password reset. The plan may
also define escalation triggers and actions, including incident response, investigation, and public
affairs activities.
See Advanced Cyber Industrial Control System Tactics, Techniques, and Procedures for
Department of Defense Industrial Control Systems for examples of applicable TTPs to be
considered for use or tailoring to base-specific conditions.
A2.7.4.2. Response and recovery plans should frequently be tested and reviewed. Personnel
should be aware of their roles and responsibilities in case of an incident.
A2.7.4.3. Have a restoration plan in place, including having “gold disks” ready to restore
systems to known good states.
A2.8. Access Control.
A2.8.1. Abide by strict access control protocols to prevent unauthorized physical access to all
components of the CS (focusing on control nodes) and the unauthorized introduction of new
hardware, infrastructure, and communications interfaces where feasible.
A2.8.2. Adhere to strict access control protocols for logical access to systems – limit to authorized
users on an as-needed basis with permissions pertinent to the users’ role.
A2.8.3. Enforce separate authentication mechanisms and credentials for users of the CS network
and the BAN (i.e., CS network accounts do not use BAN user accounts).
A2.9. Connectivity. All non-BAN connectivity to CS (including, but not limited to, dial-up, Internet,
Bluetooth, wireless, and cellular) are considered external connections. These connections bring
substantial vulnerabilities warranting additional scrutiny and cybersecurity safeguards.
A2.9.1. Any data transmitted by commercial wireless devices, services, and technologies will
implement end-to-end data encryption over an assured channel (AC). The security level of data
encryption shall be dictated by the sensitivity of the data and validated under the “Cryptographic
Module Validation Program,” specified in FIPS PUB 140-2. Per DoDD 8100.02, individual exceptions to
unclassified wireless encryption may be granted on a case-by-case basis after an operational risk
assessment is conducted and approval is granted by the AO.
A2.9.2. CS with dial-up modem connections to the Defense Switched Network (DSN), such as direct
subscriber lines (DSL), require AF Enterprise AO approval and ATC prior to use. The DSN is a primary
information transfer network for the Defense Information Systems Network (DISN) and provides the
worldwide non-secure voice, secure voice, data, facsimile, and video teleconferencing services for the
DoD and other Federal agencies. All dial-up modem requests shall be submitted through eMASS for CE’s
ICS PIT AO and the AF Enterprise AO approval. Until approved, all dial-up modem connections are
immediately prohibited.
AFGM Page 8

Air Force Civil Engineer
UESC Playbook
83 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.9.3. A DoD Chief Information Officer (CIO) waiver is required before procuring any of the following
commercial services: Internet Service Provider (ISP), networking, system hosting, satellite and cloud
computing. The DoD CIO grants DoD Information Network (DODIN) (formally Global Information Grid
(GIG)) waivers to use non-DISN commercial IT services when in the best interest of DoD and when
Defense Information Systems Agency (DISA) services cannot support mission requirements. Requests
are evaluated from a Joint Information Enterprise (JIE) perspective for efforts such as cybersecurity,
information sharing, budgeting, interoperability and mission scope.
A2.9.4. Use of a commercial ISP is not authorized unless a DODIN waiver has been approved for this
service. Immediately cease all unapproved commercial ISP connections. Seek a DODIN waiver from the
DoD CIO. Neither the Installation Commander, Mission Support Group Commander, nor CE’s ICS PIT AO
have the authority to approve commercial ISP connections. Unauthorized Commercial ISP connections
result in a Denial of Authorization to Operate (DATO).
A2.9.4.1. Visit the DISA website for the DODIN Waiver Process.
A2.10. Solid State Devices and Removable Media. As recommended by NIST SP 800-82, no removable
media is to be connected to a CS or CS enclave other than as described in section A2.15.4. Provisions should
be made to prohibit the connection of unauthorized items, including vendor-owned devices. Make any
necessary adjustments to the Service Level Support Agreement or service contract with the system
maintainer or vendor.
A2.10.1. In the instance Solid State Hard Drives, Thumb Drives, Dongles, DVDs, CDs, and other
removable media and storage devices are connected to a CS or CS enclave, ensure compliance with
requirements outlined in USCYBERCOM CTO 10-084 and AF Network Operations Center NETOPS
Tasking Order 2008-323-001.
A2.11. Switches. The use of switches within the CS should be kept to a minimum and should use managed
switches to restrict port access to the CS. These devices have Security Technical Implementation Guides
applicable to them, and their configurations will be assessed during the RMF lifecycle. The use of hubs is not
permitted. In instances where replacing unmanaged switches becomes an enormous cost and labor burden,
the best practice is to replace unmanaged switches with managed switches at the end of the asset’s life
cycle, however operating unmanaged switches will be taken into account by the SCA and AO.
All switches should have physical security measures. Ensure switches are stored in a locked, secure
area/cabinet, and add necessary tamper-proof features to restrict access to these devices.
A2.12. Handheld Personal Devices. The use of a Personal Data Assistant (PDA) to access, monitor or control
CE-owned CS is not authorized. The discovery of such a connection can result in issuance of a DATO and thus
disconnection from the AF Information Network (AFIN).
AFGM Page 9

Air Force Civil Engineer
UESC Playbook
84 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.13. Device Security.
A2.13.1. Operating Systems. NIST SP 800-82 notes that CS operating systems and control networks
are often quite different from their IT counterparts, requiring different skill sets, experience, and
levels of expertise. Control networks are typically managed by control engineers, not IT personnel.
Assumptions that differences are not significant can have disastrous consequences on system
operations.
A2.13.1.1. To the greatest extent practicable given acceptable levels of risk and final approval by
the Lifecycle System Owners, AF CS’ operating systems should be upgraded and maintained to
the most current operating system and patch levels approved by the Air Force for the
workstation baseline.
A2.13.1.2. In instances when the CS operating system cannot be upgraded for technical or
operational reasons, the risk, mitigating actions, and a Plan of Actions and Milestones must be
documented and approved through the RMF process by the appropriate approval roles.
A2.13.2. Anti-Virus. Use security controls such as antivirus software and file integrity checking
software where technically feasible to prevent, deter, detect, and mitigate malware on CS.
A2.13.2.1. Antivirus tools only function effectively when installed, configured, run full-time, and
are maintained properly against the state of known attack methods and payloads. However,
while antivirus tools are common security practice in IT computer systems, their use with CS may
require adopting special practices including compatibility checks, change management issues,
and performance impact metrics.
These special practices should be utilized whenever new signatures or new versions of anti-
virus software are installed.
A2.13.2.2. Windows, Unix, Linux systems, etc. used as consoles, engineering workstations, data
historians, HMIs and general purpose SCADA and backup servers generally can be secured just
like enterprise IT equipment: install push- or auto- updated antivirus and patch management
software with updates distributed via an antivirus server and patch management server located
inside the CS network and auto-updated from the BAN.
A2.13.2.3. Follow vendor recommendations on all other servers and computers (DCS, PLC,
instruments) that have time-dependent code, modified or extended operating systems or any
other change that makes it different from a standard device. Expect the vendor to make periodic
maintenance releases that include security patches.
A2.13.3. Ports / Services. Because the specific function of dedicated CS devices should be determined
and documented, it is relatively easy to identify those ports and input/output devices that are
unnecessary.
A2.13.3.1. Disable all unused ports and services on CS devices after testing to ensure this will not
impact the CS operation.
A2.13.3.2. Ensure that unused ports and services remain disabled.
A2.13.3.3. Uninstall any programs, applications and services not strictly necessary for operation of
the control system.
A2.14. Configuration / Patch Management. An essential aspect of life cycle cybersecurity management is
patch management to mitigate known vulnerabilities of CE-owned CS.
AFGM Page 10

Air Force Civil Engineer
UESC Playbook
85 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.14.1. Appropriate configuration change processes and procedures should be instituted and followed
to ensure any changes to the baseline configuration are approved and coordinated with the ISO and
Mission Owner (MO). The ISO should track any system modifications and document them in the
installation’s CS inventory IAW NIST SP 800-53.
A2.14.2. Ideally, in order to evaluate the operational impact of installation new software prior to
being applied to an operational environment, system patches and upgrades should first be assessed
in a testing environment, on a backup/redundant system, or on an offline system. Then, the
operational risk to the availability of the system should be weighed against the unpatched security
risk to the system by the appropriate approval authority for the system or subsystem.
A2.14.3. While recognizing that an enterprise-wide CS cyber test range does not exist yet, it is
recommended to work with the system vendor or manufacturer through hardware and software
maintenance agreements to provide operational testing and evaluation. Bases are not expected to
procure separate testbed environments for every CS.
A2.14.4. Systems should be patched or updated only with digitally-signed or hashed software
from trusted authoritative sources.
A2.14.5. Procedures for on-site maintenance and patches for CS are outlined in sections A2.15.4
and A2.15.5.
A2.14.6. For further guidance on patch management, refer to NSA Guidelines for
Configuration / Patch Management in Industrial Control Systems.
A2.15. On-site Maintenance. System maintenance practices to be followed are listed below. Further details
of these practices can be found in NIST SP 800-82.
A2.15.1. To the greatest extent possible, maintenance and support should be performed on- site only
(not remotely).
A2.15.2. Plan for or enforce having (if a plan exists) only government-owned computers connect to
CS and CS enclaves (for maintenance or other authorized uses).
A2.15.3. Government-owned maintenance assets will be maintained by CE and must remain in
government control. These maintenance assets must adhere to the following restrictions:
A2.15.3.1. Maintain the cybersecurity practices and procedures also required for NIPRNet
machines.
A2.15.3.2. Uninstall any programs, applications, and services not strictly necessary.
A2.15.3.3. Disable any Wi-Fi, cameras, or microphones, preferably at the hardware or physical
level.
A2.15.3.4. As stated in NIST SP 800-46 procedures, when existing contracts do not allow for
maintenance using government-owned assets, ensure assets used by vendors and service
personnel are thoroughly scanned for viruses and malware and have anti- virus software enabled
before the asset is allowed to connect to a CS enclave or related infrastructure.
A2.15.3.5. For future CS maintenance-related contracts, incorporate contracting language
ensuring the use of government-owned assets for CS maintenance.
Suggested CS contracting language is detailed in DHS’s Cyber Security Procurement Language for
Control Systems.
AFGM Page 11

Air Force Civil Engineer
UESC Playbook
86 | P a g e
AFGM 2017-32-01
Civil Engineer Control Systems Cybersecurity
A2.15.4. CS that support Tier 1 TCAs should be on air-gapped networks and not directly connected to
either a CS enclave, the NIPRNet, or the Internet. On-site maintenance and patches for DCI-
supporting CS will be accomplished using the following procedures:
A2.15.4.1. Download digitally-signed or hashed software from trusted authoritative sources to
a CD/DVD.
A2.15.4.2. Scan the CD/DVD on a computer having classified scanning signatures to ensure it is
malware-free.
A2.15.4.3. Insert the CD/DVD into a government-owned maintenance computer (per section
A2.15.3) to connect to the stand-alone system or air-gapped CS network.
A2.15.4.4. After patching or upgrading the system, destroy the CD/DVD media to ensure it
cannot be used in another device.
A2.15.5. CS that do not support DCI, whether stand-alone or connected to a CS enclave, can be
maintained according to defined base maintenance, configuration, and patch management
processes.
A2.15.6. Ensure CS maintenance and repair is performed and logged in a timely manner with
approved tools IAW this AFGM and existing policy.
A2.16. Remote Maintenance. When on-site maintenance and support (per section A2.15) absolutely
cannot be accommodated for existing contractual or cost-effective reasons, remote maintenance access to
CS is allowed as an option of last resort only for CS not supporting DCI. If remote access is employed, bases
must adhere to the following recommendations and restrictions:
A2.16.1. Follow security measures recommended in NIST SP 800-46, NIST SP 800-82, and
DHS/CPNI’s Configuring and Managing Remote Access for Industrial Control Systems such as
requiring encryption and token-based, multi-factor authentication.
A2.16.2. Remote access to the CS or CS enclave should be of limited duration – allowed only for the
time necessary to accomplish the established maintenance task. The allotted time, initial time of
access, and reason for access should be coordinated between the base and vendor in order for
remote access to be enabled and monitored.
A2.16.3. Any remote access to the CS or CS enclave outside of the pre-arranged window should be
blocked by disabling the modem or by other technical means.
A2.16.4. All remote access events should be logged and monitored. Access and events should be
reviewed on a regular schedule. Additionally, the legitimacy and necessity of access should be
verified.
A2.16.5. Remote access to CS is to be phased out. On-site maintenance requirements, cybersecurity
procedures and Service Level Support Agreements are to be written into new, renewed or updated
maintenance and support contracts.
A2.16.6. Other remote access to the CS or CS enclave not meeting these specifications is prohibited.
A2.16.7. Remote access to CS supporting DCI is prohibited.
AFGM Page 12

Air Force Civil Engineer
UESC Playbook
87 | P a g e
A2.17. Transition Plan. Funding for contract support to assume these roles and responsibilities is currently in
the process of being approved through the FY18 budgeting process.
A2.17.1. To alleviate the burden and to support compliance with these RMF and cybersecurity
requirements, funding for contract support is in the approval process for FY18 to provide CE CS
cybersecurity expertise at the base level in a prioritized manner. These full-time cybersecurity
professionals will be dedicated to managing the CS cybersecurity efforts for the CE functional
community, including conducting and maintaining accurate inventories, conducting mission support
analysis, managing and configuring the type-accredited CS enclaves, conducting self-assessments of
security controls and performing cybersecurity maintenance and lifecycle management of CE-
owned CS.
A2.17.2. Inventories and the full implementation of cybersecurity controls on critical
infrastructure-related CS need to be completed and in place by the end of FY19. Until bases
receive dedicated manpower, bases are expected to plan for and comply with the remainder of
guidance contained in this AFGM to the greatest extent possible given availability of resources
and expertise.
A2.17.3. At this time, the exact roles and responsibilities for a Cybersecurity Defense Service Provider
(CDSP) to provide defensive cyber operations and continuous monitoring for CE-owned CS and CS
enclaves have not yet been determined.
A2.17.4. Further training material and templates are forthcoming to assist in base execution of this
AFGM’s requirements.
A2.18. Technical Support. For specific CS-related technical support and guidance, AFCEC’s CEMIRT Division
supports the accreditation of CE CS and guidance for implementing the enclave for CE-owned CS. CEMIRT
can be reached by phone at DSN 523-6989/6929 or by e- mail at afcec.comi.icshelp[email protected],
afcec.comi.ics@us.af.mil.
A2.19. Technical References. For specific technical guidance on the policies outlined above and on
additional CE CS security controls, consult the following references which detail procedures on
cybersecurity best practices and on system classification for tailoring security controls.
A2.19.1. NIST SP 800-82 A2.19.2.
NIST SP 800-53
A2.19.3. NIST Framework for Industrial Control System Cybersecurity
A2.19.4. NSA Information Assurance Directorate Guidance for Industrial Control Systems
A2.19.5. Advanced Cyber Industrial Control System Tactics, Techniques, and Procedures for
Department of Defense Industrial Control Systems
A2.19.6. Federal Information Processing Standards Publications (FIPS PUBS)
A2.19.7. CNSSI No. 1253, Security Control Overlays for Industrial Control Systems
A2.19.8. DHS ICS-CERT Standards and References
A2.19.9. Air Force Control Systems Community
AFGM Page 13

Air Force Civil Engineer
UESC Playbook
88 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
DEPARTMENT OF THE AIR FORCE
HEADQUARTERS AIR FORCE CIVIL ENGINEER SUPPORT AGENCY
30 MAR 2011
FROM: HQ AFCESA/CEO
139 Barnes Drive Suite 1 Tyndall AFB
FL 32403-5319
SUBJECT: Engineering Technical Letter (ETL) 11-1: Civil Engineer Industrial Control
System Information Assurance Compliance
1. Purpose. This ETL provides technical guidance and criteria for information assurance
(IA) of civil engineering (CE) industrial control systems (ICS). This ETL applies to all
ICSs that utilize any means of connectivity to monitor and control industrial processes,
including supervisory control and data acquisition (SCADA) systems, distributed
control systems (DCS), and other control system configurations such as
programmable logic controllers (PLC), which are often found in industrial equipment
and critical infrastructures.
Note: The use of the name or mark of any specific manufacturer, commercial product,
commodity, or service in this ETL does not imply endorsement by the Air Force.
2.
Application. This ETL supersedes ETL 09-11, Civil Engineering Industrial Control
System Information Assurance Compliance, dated October 26, 2009. Requirements in
this ETL are mandatory. The interpreting authority for this ETL is the Air Force Civil
Engineer Support Agency, Operations and Programs Support Division, Engineer
Support Branch (HQ AFCESA/CEOA).
2.1.
Authority: Air Force instruction (AFI) 32-1063, Electric Power Systems.
2.2.
Effective Date: Immediately.
2.3.
Intended Users:
Major command (MAJCOM) engineers
Base civil engineers (BCE)
ICS information assurance managers (IAM)
2.4.
Coordination:
MAJCOM engineers responsible for CE ICSs
The Air Force Civil Engineer, Resources Division, Information Technology
Branch (HQ AF/A7CRT)
Air Force Network Integration Center, Information Assurance Directorate
(AFNIC/EV) and Air Force certifying authority (CA)
Chief, Cyberspace Surety Division (SAF/A6OI), on behalf of Director,
Cyberspace Operations (SAF/A6O) and Air Force senior information
assurance officer (SIAO)
APPROVED FOR PUBLIC RELEASE: DISTRIBUTION UNLIMITED
ETL 11-1 Pg 1

Air Force Civil Engineer
UESC Playbook
89 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
3.
Referenced Publications.
3.1.
Air Force (departmental publications available at http://www.e-
publishing.af.mil/):
Air Force policy directive (AFPD) 16-14, Information Protection
AFI 31-401, Information Security Program Management
AFI 31-501, Personnel Security Program Management
AFI 32-1063, Electric Power Systems
AFI 33-112, Information Technology Hardware Asset Management
AFI 33-114, Software Management
AFI 33-115V1, Network Operations (NETOPS)
AFI 33-115V2, Licensing Network Users and Certifying Network Professionals
AFI 33-200, Information Assurance (IA) Management
AFI 33-210, Air Force Certification and Accreditation (C&A) Program
(AFCAP)
AFI 33-230, Information Assurance Assessment and Assistance Program
AFNIC EV 2010-08, Guide for Submission of Platform Information
Technology (PIT) Determination Concurrence Requests, 18 August 2010
Information Technology Investment Policy Guidance Memorandum,
9 June 2008, HQ USAF/A7C
3.2.
United States Code (U.S.C.):
Title 40 U.S.C. 1401(3), The Clinger-Cohen Act of 1996
3.3.
Code of Federal Regulations (CFR):
Title 47, CFR, Part 15, Radio Frequency Devices, http://www.gpo.gov/
3.4.
Department of Defense (DOD):
DOD 8570.01-M, Information Assurance Workforce Improvement Program,
incorporating Change 2, 20 April 2010, http://www.dtic.mil/whs/
DOD Directive (DODD) 8000.01, Management of the Department of Defense
Information Enterprise, 10 February 2009,
http://www.dtic.mil/whs/directives/corres/pdf/800001p.pdf
DODD 8100.02, Use of Commercial Wireless Devices, Services, and
Technologies in the Department of Defense (DOD) Global Information Grid
(GIG), 14 April 2004, http://www.dtic.mil/whs/directives/corres/dir.html
DODD 8500.01E, Information Assurance (IA), 24 October 2002,
http://www.dtic.mil/whs/directives/corres/dir.html
DOD Instruction (DODI) 5000.02, Operation of the Defense Acquisition
System, 8 December 2008, http://www.dtic.mil/whs/directives/
DODI 8500.2, Information Assurance (IA) Implementation, 6 February 2003,
http://www.dtic.mil/whs/directives/corres/ins1.html
DODI 8510.01, DOD Information Assurance Certification and Accreditation
Process (DIACAP), 28 November 2007
http://www.dtic.mil/whs/directives/corres/ins1.html
ETL 11-1 Pg 2

Air Force Civil Engineer
UESC Playbook
90 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
3.5.
National Institute of Standards and Technology (NIST):
Federal Information Processing Standards Publication (FIPS PUB) 140-2,
Security Requirements for Cryptographic Modules, 25 May 2001,
http://csrc.nist.gov/
FIPS PUB 197, Advanced Encryption Standard (AES), 26 November 2001
http://csrc.nist.gov/
NIST Special Publication (SP) 800-53, Recommended Security Controls for
Federal Information Systems and Organizations, Revision 3, August 2009,
http://csrc.nist.gov/publications/nistpubs/
NIST SP 800-82, Guide to Industrial Control Systems (ICS) Security, Final
Public Draft, September 2008, http://csrc.nist.gov/publications/drafts/
NIST SP 800-18, Guide for Developing Security Plans for Federal Information
Systems, Revision 1, February 2006,
http://csrc.nist.gov/publications/nistpubs/
3.6.
Other Government References:
Committee on National Security Systems Instruction (CNSSI) No. 4012,
National Information Assurance Training Standard for Senior System
Managers, June 2004, Committee on National Security Systems,
http://www.cnss.gov/Assets/pdf/cnssi_4012.pdf
Federal Information Security Management Act (FISMA) of 2002, Section 301:
Information Security, http://iase.disa.mil/fisma/index.html
National Security Telecommunications and Information Systems Security
Instruction (NSTISSI) No. 4015, National Training Standard for System
Certifiers, December 2000, Committee on National Security Systems,
http://www.cnss.gov/Assets/pdf/nstissi_4015.pdf
Office of Management and Budget (OMB) Circular A-76, Performance of
Commercial Activities, 29 May 2003, http://www.whitehouse.gov/
OMB Circular A-130, Management of Federal Information Resources,
28 November 2000, http://www.whitehouse.gov/
National Telecommunications and Information Administration, Manual of
Regulations and Procedures for Federal Radio Frequency Management,
September 2010 Revision of the 2008 Edition, http://www.ntia.doc.gov/
4.
Acronyms and Terms. See Attachment 2.
5.
Background.
5.1.
ICS Overview.
5.1.1.
Industrial control system (ICS) is a general term for several types of control
systems, including SCADA systems, DCSs, and other control system
configurations such as skid-mounted or panel-mounted PLCs often found in
the industrial sector and critical infrastructure. ICSs are typically used in
infrastructure/utility/industrial systems such as electrical, water and
wastewater, oil and natural gas, chemical, transportation, pharmaceutical,
pulp and paper,
ETL 11-1 Pg 3

Air Force Civil Engineer
UESC Playbook
91 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
food and beverage, and discrete manufacturing (e.g., automotive,
aerospace, and durable goods).
5.1.1.1.
SCADA systems are highly distributed systems used to control
geographically dispersed assets, often scattered over thousands of square
miles, where centralized data acquisition and control are critical to system
operation. SCADA systems are used in distribution systems such as water
distribution and wastewater collection systems, oil and natural gas pipelines,
electrical power grids, and railway transportation systems.
5.1.1.2.
DCSs are used to control industrial processes such as electrical
power generation, oil refineries, water/wastewater treatment, and
manufacturing production. DCSs are integrated as a control architecture
containing a supervisory level of control overseeing multiple integrated
subsystems responsible for controlling the details of a localized process.
5.1.1.3.
PLCs are computer-based, solid-state devices controlling almost all
industrial equipment and processes. While PLCs are control system
components used throughout DCS and SCADA systems, PLCs are often the
primary components in smaller control system configurations used to provide
operational control of separate processes.
5.1.2.
For Air Force CE, real property ICSs include, but are not limited to, the following
types of systems (including all points, devices, control panels, means of
connectivity, software, controllers, computer workstations, servers, etc.):
Supervisory control and data acquisition (SCADA) systems
–
Fuel distribution systems
–
Protective relays
–
Cathodic protection systems
–
Power generation systems, including renewable systems
–
Natural gas distribution systems
Energy management and control systems (EMCS)
Automated meter reading (AMR)/utility systems, including water metering
systems
Fire alarm/fire suppression/mass notification systems
Utility monitoring and control (UMAC) systems
–
Electrical distribution systems
–
Generator monitoring systems
–
Water system controls
–
Natural gas distribution systems
Airfield control systems
–
Lighting system controls
–
Aircraft arresting system (AAS) controls
Traffic signal controls and vehicle barriers
ETL 11-1 Pg 4

Air Force Civil Engineer
UESC Playbook
92 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
CE-maintained intrusion detection systems (IDS) (by CE/Security Forces
memorandum of agreement only). Note: IDSs are not considered real
property installed equipment.
5.1.3.
Initially, many CE ICSs had little resemblance to traditional information
technology (IT) systems in that ICSs were isolated systems running
proprietary control protocols using specialized hardware and software.
Widely available, low cost Internet Protocol (IP) devices are now replacing
proprietary solutions, which increases the possibility of cyber security
vulnerabilities and incidents. As ICSs are adopting IT solutions to promote
corporate business systems connectivity and remote access capabilities,
and are being designed and implemented using industry standard
computers, operating systems, and network protocols, ICSs are starting to
resemble IT systems. This integration supports new IT capabilities, but it
provides significantly less isolation for ICSs from the outside world than
predecessor systems, creating a greater need to secure these new systems.
While security solutions have been designed to deal with these security
issues in typical IT systems, special precautions must be taken when
introducing these same solutions to ICS environments. In some cases, new
security solutions are needed that are tailored to the ICS environment.
5.1.4.
Many ICS characteristics differ from those of traditional IT systems, including
different risks and priorities. Some of these ICS characteristics include
significant risk to the health and safety of human lives and serious damage to
the environment. ICSs have different performance and reliability
requirements and use operating systems and applications that may be
considered unconventional to typical IT support personnel. Furthermore, the
goals of safety and efficiency can sometimes conflict with security in the
design and operation of control systems. For example, requiring password
authentication and authorization should not hamper or interfere with
emergency actions for the ICS. For additional information concerning the
distinct differences between ICSs and typical IT systems, see NIST SP 800-
82, Guide to Industrial Control Systems (ICS) Security, section 3.1.
5.2.
Information Assurance (IA) of ICSs.
5.2.1. The Air Force Chief Information Officer (CIO) has issued policy guidance for
the identification and IA of all legacy and future information systems (IS). For
the CE community, these systems include the ICSs identified in paragraph
5.1.2 whether or not they are physically connected to the base local area
network (LAN) or Air Force Global Information Grid (AF-GIG). ICSs that do
not have a direct connection to the AF-GIG (see Attachment 2 for definition)
are considered platform IT (PIT) systems. If a connection to the AF-GIG
exists, that connection is considered a PIT interconnection (PITI).
ETL 11-1 Pg 5

Air Force Civil Engineer
UESC Playbook
93 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
5.2.2. Platform IT (PIT) Systems.
5.2.2.1.
A PIT system is considered a special purpose system using computing
resources (i.e., hardware, firmware, and [optionally] software) that are
physically embedded in, dedicated to, or essential in real time to the
mission performance of the system. A PIT system performs only (i.e., is
dedicated to) the information processing assigned to the PIT system by its
hosting special purpose system. Examples include, but are not limited to,
SCADA-type systems, certain medical devices, training simulators, and
diagnostic test and maintenance equipment.
Note: PIT point-to-point interconnections using an Air Force installation’s
backbone infrastructure for the purpose of connecting to remote sensors or
to another PIT capability (within the same base/enclave) are not considered
to be PITIs as long as they are logically or physically separated/isolated
from the base common user infrastructure and systems (see AFNIC EV
2010-08, Guide for Submission of Platform Information Technology (PIT)
Determination Concurrence Requests). See section 8.1.6 of this ETL for
additional guidance on virtual local area networks (VLAN).
5.2.2.2.
ICS PIT Certification and Accreditation (C&A). ICS PIT C&A is required for
any new or existing ICS. ICS PIT C&A is not to be confused with the Air
Force Certification and Accreditation Program (AFCAP) that utilizes the
Defense Information Assurance Certification and Accreditation Process
(DIACAP). The ICS PIT C&A process is illustrated in Attachment 1, with
step-by-step instructions provided in section 7. New system acquisitions
must incorporate security and IA requirements into the design
specifications, and systems already in operation require IA controls as
prescribed in current policy and guidance. PIT systems require IA risk
assessment (RA) and periodic review as directed by the PIT designated
accrediting authority (DAA).
5.2.3. Platform IT Interconnections (PITIs).
5.2.3.1.
A PITI is the interface/connection between a PIT and the AF-GIG or any
other DOD communications network. Examples of PITIs that require
security considerations include, but are not limited to, PIT communications
interfaces for data exchanges with the AF-GIG for mission planning or
execution, remote administration, remote sensing, remote alerting
(including one-way communication), and remote upgrade, query, or
reconfiguration.
5.2.3.2.
PITI C&A.
5.2.3.2.1.
When a PIT system requires connection to the AF-GIG or any other DOD
network to exchange information as part of the mission of the ICS, the IA
requirements for the exchange must be explicitly addressed as part of the
interconnection. These interconnections are subject to the AFCAP and
ETL 11-1 Pg 6

Air Force Civil Engineer
UESC Playbook
94 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
DIACAP as outlined in AFI 33-210, Air Force Certification and
Accreditation (C&A) Program (AFCAP), and DODI 8510.01, DOD
Information Assurance Certification and Accreditation Process (DIACAP),
respectively.
5.2.3.2.2.
PITI C&A requires documenting any additional measures required by the
AF-GIG to extend IA services or to protect the PIT from interconnection
risk. The IA controls and level of robustness must be selected as
applicable and shall consider the mission assurance category (MAC) and
confidentiality level of both the PIT and its interconnecting means. IA
controls provide a common management language for establishing IA
needs, promoting consistency for testing and validating the implemented
IA solutions, reducing complexity when managing changes to the
validated baseline, providing a common pivot point when negotiating
interconnections, and increasing accuracy for reporting IA readiness.
Note: IA controls listed in DODI 8500.2, Information Assurance (IA) Implementation, and
NIST SP 800-53, Recommended Security Controls for Federal Information Systems and
Organizations, Appendix I (“Industrial Control Systems”), are designed to complement
each other in addressing the uniqueness of PIT or PITI. When IA controls conflict, the
MAC of the interconnected system will drive the security objectives of the PIT or PITI
ICS.
Note: All IT is subject to IA policy, but PIT is excluded from the AFCAP; however, PITIs
are specifically subject to the AFCAP, per AFI 33-210.
5.2.4. Figure 1 shows the applicability of IA policy for PIT systems and IA policy and the
AFCAP for PITIs to the AF-GIG.
ETL 11-1 Pg 7

Air Force Civil Engineer
UESC Playbook
95 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
6.
Designated Personnel: General Roles, Responsibilities, and Qualifications.
6.1.
Within CE are base-level ICS IAMs, MAJCOM ICS functional area managers (FAM),
the ICS program manager (PM), the ICS PIT certifying authority (CA), the ICS
portfolio manager (PfM), and the ICS PIT DAA. Their general roles, responsibilities,
and qualifications are as follows:
6.1.1.
Base-level ICS IAM. The BCE shall appoint, in writing, a primary and alternate
ICS IAM for the civil engineer group (CEG) or civil engineer squadron (CES). The
ICS IAMs are responsible for ensuring that base CE ICSs are certified and
accredited in accordance with DOD and Air Force IA directives and instructions.
6.1.1.1.
The primary ICS IAM must have Information Assurance Technical (IAT) Level
II or Information Assurance Management (IAM) Level I certification in
accordance with DOD 8570.01-M, Information Assurance Workforce
Improvement Program, within six months of BCE appointment. (Note:
Security+ certification satisfies either IAT Level II or IAM Level I certification.)
If the CEG or CES has IT support personnel, it is recommended that the BCE
assign an IT system administrator as the primary ICS IAM. Many Air Force
CE IT specialists have IAT Level I or higher certification. In addition to the
primary ICS IAM, an alternate ICS IAM must be appointed to assist the
primary with the functional and technical aspects of ICSs. The alternate ICS
IAM must be a qualified ICS operator/technician, and IAT/IAM certification is
desired but not required. The alternate ICS IAM’s primary role is to provide
the necessary technical support/expertise to the primary ICS IAM to achieve
ICS IA certification and accreditation. These two individuals will leverage each
other’s expertise to achieve IA of our ICSs.
6.1.1.2.
The primary ICS IAM shall:
Approve and manage all access privileges to ICS software and
systems; validate all access privileges annually; and re-evaluate
frequency requirements every three years or at any mission
change, system change, or other significant change to operating
requirements.
Ensure appropriate access privileges for all individuals based on
their training, qualification, and functional duties.
Manage CE ICS access by ensuring that accounts are deactivated
or activated in a controlled manner. Personnel designated to make
configuration decisions and responsible for IA controls for both PIT
and PITI shall be certified to IAT Level II or IAM Level I in
accordance with DOD 8570.01-M.
Have full administrative rights to install software updates/patches.
Have access to review, modify, and edit the Enterprise Information
Technology Data Repository (EITDR) entries as approved by the
ICS FAM.
ETL 11-1 Pg 8

Air Force Civil Engineer
UESC Playbook
96 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Document and track system configurations for each CE-owned,
-operated, and -maintained ICS throughout the system life cycle,
including any Air Force CE ICSs operated and maintained by
contractors. For each ICS, the ICS IAMs will assemble a PIT
determination package in accordance with section 7.1.1 of this ETL
and forward the package to the respective ICS FAM.
Provide an annual report entitled “Industrial Control System
Security Status Report” to the MAJCOM ICS FAM. The report will
include a summary of current systems and system changes and will
indicate compliance/non-compliance with IA security requirements.
This report is due to the ICS FAM in October of each year.
6.1.1.3.
The alternate ICS IAM shall:
Document and track system configurations for each CE-owned,
-operated, and -maintained ICS throughout the system life cycle,
including any Air Force CE ICSs operated and maintained by
contractors. For each ICS, the ICS IAMs will assemble a PIT
determination package in accordance with section 7.1.1 of this ETL
and forward the package to the respective ICS FAM.
Provide an annual report entitled “Industrial Control System
Security Status Report” to the MAJCOM ICS FAM. The report will
include a summary of current systems and system changes and will
indicate compliance/non-compliance with IA security requirements.
This report is due to the ICS FAM in October of each year.
6.1.2.
MAJCOM ICS FAM. The ICS FAM is designated in writing by the MAJCOM A7O
(Operations) or equivalent. The ICS FAM is responsible for collecting the base-
level PIT determination packages, reviewing them for completeness, and sending
them to the ICS PM. In addition, the ICS FAM will submit an annual report
entitled “Industrial Control System Security Status Report” to the ICS PfM. This
report will contain a summary of current systems and system changes and will
indicate compliance/non-compliance with IA security requirements. This report is
due in November of each year. The ICS FAM may have access to create, modify,
or delete EITDR entries as approved by the ICS PM or ICS PfM.
6.1.3.
ICS PM. The ICS PM is designated in writing by HQ AFCESA/CEO. The ICS PM
is responsible for ensuring appropriate scheduling of all IA aspects of the
program to meet the ultimate goals of IA compliance. The ICS PM is also
responsible to ensure that the following tasks are accomplished:
Review and submit ICS PIT packages to Air Force CA for a PIT
determination statement.
Complete initial EITDR entries for CE ICS PITs.
Provide updates to MAJCOM FAMs on the status of C&A activities of their
respective systems.
Establish a PIT integrated product team (IPT) of engineers, testers, etc.
ETL 11-1 Pg 9

Air Force Civil Engineer
UESC Playbook
97 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Coordinate and oversee execution of IA RAs.
Ensure that all IA testing requirements are performed.
6.1.4.
ICS PIT CA. The PIT CA is the technical authority for the IA aspects of a PIT
system within their control. The PIT CA is responsible for ensuring clear definition
of the IA requirements at the earliest stage possible. The PIT CA is then
responsible for ensuring the implementation of the IA requirements to the extent
possible based on program or system cost, schedule, and technical trade- offs.
One of the primary functions of the PIT CA is to review the RA completed by the
IPT. The ultimate goal of the RA is to mitigate or reduce remaining risks to an
acceptable level. The PIT CA should agree with the RAs and help structure any
mitigations for those risks not considered low. The PIT CA has the responsibility
to advise the PIT DAA in making a final IA RA of the system. The PIT CA is
designated in writing by the Air Force SIAO. The Air Force SIAO has designated
HQ AFCESA/CEO as the ICS PIT CA.
6.1.4.1.
The ICS PIT CA may have the following roles and responsibilities:
Act as the focal point for the CE ICS IA compliance program and
ETL.
Coordinate CE ICS IA-related tasks with ICS PfM/ICS PIT DAA.
Review and approve CE ICS IA strategy and implementation.
Act as the technical authority for ICS-related IA issues.
Certify the ICS IA design and implementation.
Advise the ICS PIT DAA on IA-related issues.
6.1.4.2.
Technical aspects of an ICS that may be reviewed include the following:
ICS IA requirements
Threat assessments
Accreditation boundary/demilitarized zone (DMZ)
Topology, block, and data flow diagrams
Software, hardware, and firmware analysis
Network connection compliance analysis
Integrity analysis of integrated products
Risk/vulnerability assessment results/findings
Mitigation recommendations/techniques/shortfalls
6.1.4.3.
Air Force SIAO-Directed Training, Certification, and Reporting Requirements:
Maintain compliance with training and certification criteria outlined
in National Security Telecommunications and Information Systems
Security Instruction (NSTISSI) No. 4015, National Training
Standard for System Certifiers, and DOD 8570.01-M.
ETL 11-1 Pg 10

Air Force Civil Engineer
UESC Playbook
98 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Submit monthly reports to SAF/A6OI providing the status of all
HQ AF/A7 CE ICS certified over the specified period at
6.1.5.
ICS PfM. The ICS PfM has oversight responsibility for IT initiatives and systems
for which they have lead funding responsibility. The ICS PfM is required to certify
to the Air Force CIO annually, based on the ICS security status reports received
from the ICS FAMs, that the provided IT portfolio management information is
complete, accurate, and in accordance with current Air Force IT portfolio
management direction as provided in budgetary documents (policy, annual
planning and programming guidance, program objective memorandum
preparation instructions, etc.). The ICS PM assists the ICS PfM by ensuring that
all ICSs are registered in the EITDR. The ICS PfM resides at HQ AF/A7CRT and
is responsible for CE portfolio management and annual reviews to maximize the
value of IT investments and minimize the risk.
6.1.6.
ICS PIT DAA. The PIT DAA is designated in writing by the Air Force CIO. The
PIT DAA has a level of authority commensurate with accepting, in writing, the
risk of operating all PIT systems under their jurisdiction. The PIT DAA must be
independent of any particular program, but has the authority to influence
programs from a global perspective. The PIT DAA consults with the PIT CA in
making decisions but is not bound by the recommendation of the PIT CA. The
PIT DAA takes into account the command’s technical and programmatic needs in
rendering a decision. The Air Force CIO has designated HQ AF/A7C-2 as the CE
ICS PIT DAA. See Attachment 3.
6.1.6.1.
ICS PIT DAA Responsibilities. The PIT DAA may have the following
responsibilities:
Ensure that IA requirements are identified and integrated into the
systems engineering and acquisition processes as appropriate.
Review/approve the accreditation decision package that includes
an IA RA and mitigation approach.
Accredit/deny systems for test or operation.
Submit the system accreditation package to the Air Force DAA for
network connection to the AF-GIG (if required) and acknowledge
any PITIs in their accreditation decisions.
6.1.6.2.
ICS PIT DAA Decisions. The PIT DAA may grant the following accreditation
decisions to PIT ICSs under their purview:
1.
Interim Authority to Test (IATT): Special case for authorizing testing
in an operational environment or with live data for a specified time
period. An IATT is for testing purposes only.
2.
Interim Authority to Operate (IATO): A temporary authorization to
operate under the conditions or constraints enumerated in the
accreditation decision. An IATO is normally granted for up to
ETL 11-1 Pg 11
Air Force Civil Engineer
UESC Playbook
99 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
180 days. The DAA may not grant consecutive IATOs totaling more
than 360 days.
3.
Authority to Operate (ATO): Accreditation by the DAA for the
system to operate without restriction. All IA risks are considered low
or mitigations are in place, and the DAA agrees that any residual
risk is acceptable under the circumstances. An ATO is required
prior to initial operating capability (IOC). An ATO may be granted
up to three years.
4.
Denial of Authorization to Operate: A DAA decision that the
information system cannot operate because of inadequate IA
design, failure to adequately implement assigned IA requirements,
or lack of adequate security.
6.1.6.3.
Air Force CIO-Directed Training, Certification, and Reporting
Requirements:
Complete training and maintain appropriate IA certification in
accordance with DOD 8570.01-M, Chapter 5, and Committee on
National Security Systems Instruction (CNSSI) No. 4012, National
Information Assurance Training Standard for Senior System
Managers, prior to appointment. Proof of training (e.g., certificate)
will be included as an artifact to the PIT accreditation decision
package.
Submit semi-annual reports to SAF/A6OI providing the status of all
CE PIT ICSs accredited over the specified period at
7.
CE ICS C&A Process. The C&A process for PIT systems, with or without
interconnections, commences at issuance of this ETL. The C&A process is divided into
three phases: Phase 1, ICS PIT Determination; Phase 2, ICS PIT C&A; and Phase 3,
PITI AFCAP. Figure 2 summarizes the CE ICS C&A process flow chart provided in
Attachment 1.
ETL 11-1 Pg 12

Air Force Civil Engineer
UESC Playbook
100 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Figure 2. CE ICS C&A Process Overview
7.1.
Phase 1: PIT Determination.
7.1.1.
ICS IAMs shall document system configurations for each CE-owned,
-operated and -maintained ICS, including any ICS operated and maintained by
contractors. For each ICS, the ICS IAM will assemble a PIT determination
package composed of the following information and forward that package to the
respective ICS FAM.
7.1.1.1.
Provide a single line block diagram of each type of ICS architecture. These
diagrams should show the ICS network topology (i.e., its interconnections,
data flow, components, and external connections).
System connectivity
–
How the data flows
–
Where the data is coming in and out
–
Connection type(s) – wireless radio frequency (RF), Cat5, fiber,
modem, etc.
–
Firewall location(s), if applicable
System interconnectivity (i.e., other systems to which the ICS is
connected, whether PIT, PITI, commercial Internet service provider,
World Wide Web (WWW), GIG, LAN, etc.)
Key components, including:
–
Make and model
–
IP address, if applicable
Accreditation boundary (or boundaries), DMZ, or security boundary.
The ICS security boundary shall be identified and well defined on all
single line diagrams and network topologies for each ICS. The ICS
ETL 11-1 Pg 13

Air Force Civil Engineer
UESC Playbook
101 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
security boundary is the demarcation of connection to the AF-GIG or
other DOD network.
Firewalls, if applicable
–
Vendor, make, model, software version
Cyber intrusion prevention/detection, if applicable
–
Vendor, make, model, software version
IP addresses, if applicable. Do not use Xs. Network and ranges must
be expressed correctly.
Note: The diagram must allow the Air Force CA to clearly understand and identify the
hardware, software, and other IT components as well as the mission the platform
supports.
7.1.1.2.
Complete the Modified DIACAP Implementation Plan (MDIP) template for
each ICS (see paragraph 5.1.2 for a list of common ICSs). Include any ICS
architecture and installation specifications for each type of ICS architecture.
Note: ICS architecture and installation instructions are typically provided by the
vendor and can be supported through vendor-specific literature, white papers, and/or
configuration guides.
7.1.1.3.
Complete the PIT determination checklist. This data is required by the ICS
PM for input into the EITDR.
7.1.1.4.
Describe the ICS in narrative form, and describe how, in real time, the ICS
supports the operation and functionality of the special purpose system.
7.1.1.5.
Submit the above information to the ICS FAM via a digitally signed and
encrypted e-mail message.
7.1.2.
ICS FAMs should submit the packages to the ICS PM via an encrypted and
digitally signed e-mail message.
7.1.3.
The ICS PM reviews the PIT(I) determination packages for completeness and
submits them to the Air Force CA for a PIT(I) determination. The ICS PM will
request in writing an Air Force CA evaluation to determine if the ICS is PIT(I). If
the ICS requires the use of interconnections not connected to the AF-GIG, the
ICS PM must state the justification for requesting exemption from the AFCAP,
including rationale for the ICS as PIT.
7.1.4.
The Air Force CA will evaluate the package and determine if the ICS is PIT. If the
Air Force CA determines that the submission represents PIT, the PIT
determination letter will indicate concurrence that the ICS meets the criteria for
designation as PIT and is exempt from the formal AFCAP. Non-concurrence by
the Air Force CA means the system is not a PIT system or the system has an
ETL 11-1 Pg 14

Air Force Civil Engineer
UESC Playbook
102 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
interconnection to the AF-GIG. The AFCAP will be required for those systems
and interconnections in accordance with AFI 33-210.
7.1.5.
The ICS PM shall receive the PIT(I) determination letter from the Air Force CA,
review for changes to the original ICS architecture, recommend best security
practices using, as a minimum, NIST SP 800-53, Appendix I, and provide
additional instructions for Phase 2 of the CE ICS C&A process. The ICS PM will
also provide system security and IA strategies.
7.1.5.1.
If the ICS PM does not agree with the Air Force CA’s PIT determination, the
ICS PIT CA may appeal Air Force CA’s determination to the Air Force SIAO
for reconsideration. The Air Force SIAO’s decision is final. If the ICS PM does
not wish to appeal Air Force CA’s determination, then the ICS PM will update
the PIT package indicating PITI reclassification to the ICS PfM and to the ICS
FAM.
7.1.5.2.
The ICS PM will forward to the ICS FAM the Air Force CA PIT(I)
determination statement, proposed security requirements, and IA controls
required for each approved PIT(I) ICS. The ICS PM will enter the system into
the EITDR with assistance from the ICS PfM.
7.1.6.
Upon receipt of the PIT(I) determination statement, the ICS FAM will notify the
respective ICS IAMs of the Air Force CA’s determination and any required
security actions. Transition to Phase 2 of the CE ICS C&A process is now
authorized.
7.2.
Phase 2: ICS PIT C&A.
7.2.1.
The ICS PM will provide the ICS PIT CA with an overview of, and any changes
to, the CE ICS C&A process. PIT CA approval of the RA strategy, templates,
tools, and test team activation is required prior to scheduling and supporting site
visits at active and reserve bases. The Civil Engineer Maintenance, Inspection,
and Repair Team (CEMIRT) currently provides, among other areas of expertise,
ICS technical support to the ICS PIT IPT. That support is expanding to include
CEMIRT RA teams to help base ICS IAMs assess ICS threats, vulnerabilities,
and risks. CEMIRT will also identify, implement, and/or recommend risk
mitigation strategies, techniques, and/or solutions. The CEMIRT RA team will
generate an IA RA and mitigation report within two weeks after the RA. CEMIRT
will not coordinate and schedule site visits until all site-specific PIT determination
statements are received from the Air Force CA, thus preventing multiple site
visits.
7.2.2.
The ICS PM goal will be to review and validate the IA RA and mitigation report
and assemble the accreditation decision package (ADP) for the PIT CA within 30
calendar days of receipt.
ETL 11-1 Pg 15

Air Force Civil Engineer
UESC Playbook
103 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
7.2.3.
The PIT CA will review the ADP and submit a recommendation to the PIT DAA
for consideration.
7.2.4.
The PIT DAA will issue an ATO once all compliance actions are certified by the
PIT CA. An IATO may be issued at the PIT DAA’s discretion prior to a formal
ATO to reduce or eliminate known risks/vulnerabilities. If the PIT DAA issues an
IATO or ATO, the ICS FAM and ICS IAM will be provided with a copy of the C&A
approval, and the ICS IAM is responsible for continuously monitoring the
approved PIT configuration as defined in the PIT package for security
compliance of the ICS and for making EITDR updates as necessary or as
prescribed by the ICS FAM. Changes in submitted topology or component
configuration shall be staffed to the ICS PM for approval prior to implementation.
7.3. Phase 3: ICS PITI C&A.
7.3.1.
If the PIT system has a previously identified interconnection to the AF-GIG, the
formal AFCAP commences. The AFCAP will not begin until the PIT receives an
IATO or ATO. The ICS PM will submit the entire package, with the proposed
system design or legacy system interface description, along with the ICS PIT
DAA signed ATO letter, to the Air Force CA.
7.3.2.
Using the ICS system configuration submittals from the ICS FAM, the ICS PM
and ICS PfM have the responsibility to work together and submit the package for
C&A in accordance with AFI 33-210. If the ICS requires an on-site evaluation to
validate IA controls, an IATT will be requested and submitted as part of the C&A
package.
7.3.3.
If the Air Force DAA/CA issues ATO and authority to connect (ATC) for the PITI,
the ICS PM shall work with the ICS FAM and ICS IAM to implement any
additional security actions to meet established AFCAP requirements
(i.e., continuous monitoring and annual FISMA reporting requirements). The ICS
IAM is responsible for maintaining accreditation and security for each ICS PITI. If
the Air Force DAA and/or the Air Force CA disapproves interconnect,
instructions/directions/rationale will be provided to the ICS PIT DAA and ICS PIT
CA for corrective action.
8.
Technical Requirements. This section outlines hardware and operational requirements
for existing and new PIT ICSs and for existing PITI ICSs to operate while awaiting C&A
and/or AFCAP approval.
8.1.
Base-level ICS IAMs shall ensure that ICSs comply with the requirements in the
following paragraphs. The MAJCOM ICS FAM is responsible for technical oversight
of the requirements in this section of the ETL and shall consult with the HQ AFCESA
ICS PM for clarification or interpretation of these requirements.
ETL 11-1 Pg 16

Air Force Civil Engineer
UESC Playbook
104 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Note: ICSs on OCONUS military installations (outside the continental United States
and its possessions [US&P]) or military installations not owned or operated by the
DOD are installed and maintained under the rules and regulations of the host nation
government. Personnel granted access to these systems shall comply with host
nation and Air Force minimum training and experience requirements. Waivers to this
policy require approval from the BCE, installation commander, MAJCOM CE,
HQ AFCESA/CC, and the host nation governing body.
Note: For certification of supporting ICSs under host nation control and/or ownership,
identify the ICS and forward technical information through the ICS FAM to the ICS PM
for further guidance.
8.1.1.
Because of inherent security risks, all commercial wireless networking devices
are considered “external” connections to both PIT and PITI systems and warrant
additional scrutiny before being implemented into the ICS architecture.
8.1.1.1.
At a minimum, any data transmitted by commercial wireless devices, services,
and technologies will implement data encryption from end to end over an
assured channel (AC) (see clarification in Note below) and shall be validated
under the Cryptographic Module Validation Program as meeting
requirements, per Federal Information Processing Standards Publication
(FIPS PUB) 140-2, Security Requirements for Cryptographic Modules, Overall
Level 1 or Level 2, as dictated by the sensitivity of the data. Historically, ICS
devices were not designed with encryption capabilities. In cases where
commercial wireless must be employed but the ICS device(s) cannot provide
FIPS PUB 140-2 encryption capabilities, the architecture must be carefully
designed to provide an AC and additional defense-in-depth risk mitigation
strategies to complement the IA controls to achieve an adequate level of
security. The minimum acceptable cryptographic standard is the Advanced
Encryption Standard (AES) using a cryptographic key length of 128 bits as
outlined in FIPS PUB 197, Advanced Encryption Standard (AES).
Note: To clarify, an AC is a network communication link protected by a security
protocol providing authentication, confidentiality, and data integrity, and employs US
government-approved cryptographic technologies whenever cryptographic means are
used. Examples of protocols and mechanisms sufficient to meet the requirements of
authentication, confidentiality, and data integrity protection for an AC are Internet
Protocol Security (IPSec); Secure Sockets Layer (SSL) v3; Transport Layer Security
(TLS); and systems using National Security Agency (NSA) -approved high assurance
guards with link encryption methodology.
Exception: Fire alarm reporting systems do not require data encryption for signaling
to/from the fire alarm control panel (FACP). See paragraph 8.1.5.3 for requirements
for sensitive compartmented information facilities (SCIF).
ETL 11-1 Pg 17

Air Force Civil Engineer
UESC Playbook
105 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
8.1.1.2.
Substituting wireless for wired technology introduces numerous vulnerabilities
into the network, which may be unacceptable or not cost-effective to mitigate.
Convenience and/or minimal cost savings shall not be the sole justification for
the use of wireless technologies.
8.1.1.3.
Adding commercial wireless technologies to an existing approved network
configuration boundary is considered a major configuration change and
requires a review of security controls and the accreditation decision.
Note: Data hashing, regardless of the method, is not a form of encryption.
8.1.2.
Telephone Modems.
8.1.2.1.
PIT systems with modem connections to the Defense Switched Network
(DSN) require PITI C&A (i.e., AFCAP) on those connections.
8.1.2.2.
All telephone modems shall be a secure, dial-back (call-back) type. These
exceptions apply:
Dial-out modems for voice annunciation only are not required to be of
the dial-back type.
Conventional modems over DSN lines are permitted for control of
AASs.
8.1.2.3.
All telephone modems shall be configured to communicate with on-base or
DSN numbers only.
8.1.2.4.
Submit a request to the Network Operations and Security Center (NOSC)
administrator to block all incoming commercial callers to specific modem
control numbers that access ICSs and to block modem dial-out numbers from
going off base.
8.1.2.5.
The base-level ICS IAM shall provide these numbers to the voice protection
system (VPS) personnel at the NOSC.
Note: If the PIT is connecting to one or more phone lines, the phone lines must be
identified to the respective NOSC (East, West, Air National Guard). The voice
protection team at the NOSC will assist in locking down the point of telephone service
(POTS) line to further secure the PIT.
8.1.2.6.
Establish audit procedures to record and archive modem usage, blocked
calls, and rule violations. This audit record is an IA control and shall be
accomplished annually or more often if situations dictate. These records shall
be available for a minimum of six years.
ETL 11-1 Pg 18

Air Force Civil Engineer
UESC Playbook
106 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
8.1.3.
ICS passwords shall be as follows:
8.1.3.1.
Top-level access portions of the ICS, such as system host or client stations or
computers, must comply with the following IA password safeguards.
8.1.3.1.1.
Passwords shall not be factory default settings.
8.1.3.1.2.
Passwords shall be at least 15 characters in length (for new system
acquisitions) or the maximum supportable, using the following criteria:
Do not use a password that has been used in the past.
Use a minimum of two numbers, two special characters (e.g., $, %),
two capital letters, and two lower-case letters. If special characters
are not supported by the ICS, use the broadest combination of
password features supported.
Do not create a password that includes a phone number, home
address, birth date, or personal specific dates.
Do not use a word listed in a dictionary.
Do not use simple or default passwords (e.g., 1234, data).
8.1.3.1.3.
Passwords on all systems shall be changed every 90 days.
8.1.3.1.4.
Password control shall incorporate a lock-out requirement.
8.1.3.2.
Password-capable field devices (i.e., remote terminal units or field control
devices) shall have their passwords changed from manufacturer defaults, and
thereafter, as directed by the ICS IAM. The ICS IAM shall provide written
certification to the MAJCOM ICS FAM that all password-capable field device
passwords have been changed from manufacturer defaults. This certification
shall be included as an artifact for final accreditation as PIT or PITI.
8.1.4.
Radios used on any wireless ICS within the US&P that will transmit/receive within
the Federal or military spectrum require frequency approval from base-level
spectrum managers. A DD Form 1494, Application for Equipment Frequency
Allocation, commonly referred to as the J-12 process, shall be approved before a
spectrum allocation is issued. If the ICS uses an unlicensed frequency that
complies with Federal Communications Commission (FCC) Part 15B (see Title
47 CFR, Part 15, Radio Frequency Devices), notify the base-level spectrum
manager of the use of this unlicensed frequency. If a wireless solution is
proposed for use outside the US&P, the MAJCOM ICS FAM shall contact the
MAJCOM spectrum manager for host nation approval.
8.1.4.1.
Develop contingency plans to manually control ICSs when RF interference
disrupts monitoring or control.
ETL 11-1 Pg 19

Air Force Civil Engineer
UESC Playbook
107 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Note: Non-licensed device operations must accept any interference from any Federal
or non-Federal authorized radio station, other non-licensed devices, or industrial,
scientific, and medical (ISM) equipment. The agency operating a non-licensed device
that causes interference to an authorized radio station shall promptly take steps to
eliminate the interference. Upon notification by the base spectrum manager that the
device is causing interference, the operator of the non-licensed device shall cease all
radiations from the device. Operations shall not resume until the condition causing
the interference has been corrected.
Note: Non-licensed devices, since they operate on a non-interference basis, may not
provide sufficient reliability for critical radio communications functions affecting
human life or property; however, non-licensed devices may provide valuable and
unique supplemental or expendable radio communications services where needed.
To ensure adequate regulatory protection, Federal entities should rely only on
devices with frequency assignments in the Federal or military spectrum and in the
government master file as principal radio communication systems for safeguarding
human life or property.
8.1.4.2.
Any wireless transmission in the 2.4 gigahertz (GHz) unlicensed frequency
range that is not a Combat Information Transport System Program
Management Office (CITS PMO) -installed access point should be
(618) 229-5666), for possible interference.
8.1.5.
Fire Alarm Reporting Systems.
8.1.5.1.
Manually connect/disconnect remote system access (RSA) on all FACPs
and/or servers (e.g., D-21) when RSA actions are needed/complete. Section
8.1.2 of this ETL identifies modem connection requirements.
8.1.5.2.
Communications modems shall comply with section 8.1.2.
8.1.5.3.
Fire alarm reporting from any SCIF to FACPs shall be wired (e.g., copper,
fiber) systems, not wireless, and require an (air gap) isolation device if the
available notification appliance device is a speaker. Fire alarm reporting
signals sent from the SCIF FACP to the central monitoring station must be
encrypted.
8.1.6.
Virtual Local Area Networks (VLANs).
8.1.6.1.
VLANs divide physical networks into smaller logical networks to increase
performance, improve manageability, and simplify network design. VLANs are
achieved through the use of managed Ethernet switches. A managed switch
provides all the features of an unmanaged switch, plus the ability to
configure the switch to allow greater control over how the data
ETL 11-1 Pg 20

Air Force Civil Engineer
UESC Playbook
108 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
travels over the network and who has access to it. Each VLAN consists of a
single broadcast domain that isolates traffic from other VLANs. Just as
replacing hubs with switches reduces collisions, using VLANs limits the
broadcast traffic, as well as allowing logical subnets to span multiple physical
locations. There are two categories of VLANs:
Static, often referred to as port-based, in which switch ports are
assigned to a VLAN so that it is transparent to the end user.
Dynamic, in which an end device negotiates VLAN characteristics with
the switch or determines the VLAN based on the IP or hardware
addresses.
8.1.6.2.
Although more than one IP subnet may coexist on the same VLAN, the
general recommendation is to use a one-to-one relationship between subnets
and VLANs. This practice requires the use of a router or multi-layer switch to
join multiple VLANs. Many routers and firewalls support tagged frames so that
a single physical interface can be used to route between multiple logical
networks.
8.1.6.3.
VLANs are not typically deployed to address host or network vulnerabilities in
the way that firewalls or IDSs are deployed; however, when properly
configured, VLANs do allow switches to enforce security policies and
segregate traffic at the Ethernet layer. Properly segmented networks can also
mitigate the risks of broadcast storms that may result from port scanning or
worm activity.
8.1.6.4.
Switches have been susceptible to attacks such as media access control
(MaC) address spoofing, table overflows, and attacks against the spanning
tree protocols, depending on the device and its configuration. VLAN hopping,
the ability for an attack to inject frames to unauthorized ports, has been
demonstrated using switch spoofing and double tagging. These attacks
cannot be conducted remotely and require local physical access to the switch.
A variety of features such as MaC address filtering, port-based authentication
using IEEE 802.1x, and specific vendor-recommended practices can be used
to mitigate these attacks, depending on the device and implementation.
8.1.6.5.
VLANs have been deployed effectively in ICS networks, with each automation
cell assigned to a single VLAN to limit unnecessary traffic flooding and allow
network devices on the same VLAN to span multiple switches. ICSs
connected to a VLAN shall incorporate the following:
8.1.6.5.1.
Firewalls separating base network traffic from external base traffic and the
ICS VLAN. The configuration of the ICS VLAN must ensure that no ICS
traffic exits the base firewall.
8.1.6.5.2.
Hypertext Transfer Protocol Secure (HTTPS) for remote control of the ICS
from the LAN. If Web services are provided to Nonsecure
ETL 11-1 Pg 21

Air Force Civil Engineer
UESC Playbook
109 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
Internet Protocol Router Network (NIPRNet) systems, implementation of
an AC is required.
8.1.7. Replace any unmanaged switch with a managed switch. While awaiting
replacement, add physical security measures, house unmanaged switches in a
locked secure area, and/or add tamper-proof features. The ICS PM shall approve
interim measures.
9.
Additional Guidance.
9.1.
Privatized ICSs.
9.1.1.
For the purposes of this ETL, privatization is defined as the transfer of ownership
and operations of Air Force utility systems and associated industrial
monitoring/control systems to the private sector. The private sector includes all
privately owned and publicly owned entities.
9.1.2.
DOD and Air Force directives and instructions pertaining to IA and DIACAP
requirements apply only to DOD-owned systems, including outsourced services
such as operation and maintenance (O&M) by a private entity (e.g., Office
of Management and Budget (OMB) Circular A-76, Performance of Commercial
Activities, outsourced CE O&M or AF Form 9, Request for Purchase, service
contract). A privatized utility is no longer a DOD-owned asset, including the
privatized ICS that monitors and controls the privatized utility distribution system.
Therefore, this formal real estate transaction relieves the US government from
any and all planning, financing, designing, constructing, operating, and
maintaining responsibilities of this utility infrastructure and associated monitoring
and control system.
9.1.3.
RF spectrum utilization by a privately owned or publicly owned entity while in
garrison requires base or regional spectrum management notification and/or
approval.
9.2.
Outsourced O&M of ICSs. The following information applies to any OMB Circular A-
76 outsourced CE O&M of ICSs, including AF Form 9 service contracts. DOD IA
requirements apply to government-owned PIT and PITI ICSs that are operated and
maintained by a private entity. Specific guidance for outsourced IT processes is
located below and in section 6.9 of DODI 8510.01.
9.2.1.
Outsourced IT-based processes that may also support non-DOD users or
processes must still be certified and accredited by DOD entities. IA requirements
for DOD information in an outsourced environment are determined by the
information’s MAC and classification or sensitivity and need to know, just as for
other DOD ISs. However, the following also apply:
9.2.2.
Technical security of the outsourced environment is the responsibility of the
service provider.
ETL 11-1 Pg 22

Air Force Civil Engineer
UESC Playbook
110 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
9.2.3.
Outsourced applications that are accessed by DOD users from DOD enclaves
are subject to DOD enclave boundary defense IA controls for incoming traffic
(e.g., ports and protocols and mobile code).
9.2.4.
Responsibility for procedural and administrative security is shared between the
service provider and the supported DOD entity contracting for the service.
9.2.5.
The security responsibilities of the service provider down to the control level are
made explicit in the contract, along with any other performance and service level
parameters by which the DOD shall measure the IA profile of the outsourced IT-
based process for the purpose of C&A.
9.2.6.
Any baseline IA controls not explicit in the contract or otherwise covered by a
service level agreement are categorized as NC. All such NC IA controls must be
documented in an IT security plan of action and milestones (POA&M) that
explains the acceptability of the risk of operating the outsourced IT-based
process with the control in an NC status.
9.2.7.
The security roles and responsibilities are to be made explicit in the acquisition,
along with the performance and service level parameters by which the DOD shall
measure the IA profile of the outsourced IT-based process. The PM for an
outsourced IT-based process should carefully define and assess the functions to
be performed and identify the technical and procedural security requirements that
must be satisfied in the acquisition to protect DOD information in the service
provider’s operating environment and interconnected DOD ISs.
9.3.
Type Accreditation. DODI 8510.01 defines type accreditation as “the official
authorization to employ identical copies of a system in specified environments.” This
form of C&A allows a single DIACAP package to be developed for an archetype
(common) version of an IS that is deployed to multiple locations, along with a set of
installation and configuration requirements or operational security needs, that will be
assumed by the hosting location. Automated information system (AIS) applications
accreditations are type accreditations. Stand-alone IS and DMZ accreditations may
also be type accreditations.
9.3.1.
HQ AFCESA believes the majority of Air Force ICSs vary greatly in system
hardware and software configurations, and consequently, a type accreditation is
not warranted.
9.3.2.
See AFI 33-210, section 3.14, for additional requirements regarding type
accreditations.
9.4.
Air Force Civil Engineer IT Investment Policy. In accordance with HQ
USAF/A7C’s Information Technology Investment Policy Guidance Memorandum,
dated 9 June 2008, all IT investments with functionality supporting a
ETL 11-1 Pg 23

Air Force Civil Engineer
UESC Playbook
111 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
CE capability must be approved by the A7C IT governance structure prior to any
development or sustainment activities or funds being committed or obligated. HQ
AF/A7CRT, as the CE CIO, is the office of primary responsibility (OPR) for all CE IT
investment processes, including IT portfolio management. The main purpose for the A7C
IT governance structure is to analyze, control, select, and evaluate IT investments across
the enterprise by standardizing capabilities, reducing duplication, and maximizing
functionality across existing IT resources.
10.
Points of Contact. The HQ AFCESA ICS PM has interpretive authority for the ICS IA
and security issues contained in this ETL. The authority having jurisdiction over the
content of this ETL is HQ AFCESA/CEOA.
10.1.
HQ AFCESA ICS PM. To reach the ICS PM, e-mail
[email protected], call DSN 523-6995 or commercial
(850) 283-6995, or mail to 139 Barnes Drive, Suite 1, Tyndall AFB, FL 32403-5319.
Subject line: ATTN HQ AFCESA ICS PM.
10.2.
HQ AFCESA/CEOA. To reach HQ AFCESA/CEOA, e-mail
523-6995 or commercial (850) 283-6995, or mail to 139 Barnes Drive, Suite 1,
Tyndall AFB, FL 32403-5319.
DAVID J. ANASON, Lt Col, USAF 4 Atchs
Chief, Operations and Programs Support Division 1. CE ICS C&A Process
2. Acronyms and Terms
3. CE ICS PIT DAA Appointment
4. Distribution List
ETL 11-1 Pg 24

Air Force Civil Engineer
UESC Playbook
112 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
ETL 11-1 Pg 25

Air Force Civil Engineer
UESC Playbook
113 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
ACRONYMS AND TERMS
Acronyms
AAS - aircraft arresting system
AC - assured channel
ADP - accreditation decision package
AES - Advanced Encryption Standard
AF-CA - Air Force certifying authority
AFCAP - Air Force Certification and Accreditation Program
AF-DAA - Air Force designated accrediting authority
AF-GIG - Air Force Global Information Grid
AFI - Air Force instruction
AFNIC - Air Force Network Integration Center
AFNIC/EV - Air Force Network Integration Center, Information Assurance
Directorate
AFPD - Air Force policy directive
AIS - automated information system
AMR - automated meter reading
ATC - authority to connect
ATO - authority to operate
BCE - base civil engineer
CA - certifying authority
C&A - certification and accreditation
CA - certifying authority
CCA - Clinger-Cohen Act
CE - civil engineering
CEG - civil engineer group
CEMIRT - Civil Engineer Maintenance, Inspection, and Repair Team
CES - civil engineer squadron
CFR - Code of Federal Regulations
CIO - chief information officer
CITS PMO - Combat Information Transport System Program Management
Office
Config - configuration
DAA - designated accrediting authority
DCS - distributed control system
DIACAP - DOD Information Assurance Certification and Accreditation
Process
DMZ - demilitarized zone
DOD - Department of Defense
DODD - Department of Defense Directive
DODI - Department of Defense Instruction
DSN - Defense Switched Network
EITDR - Enterprise Information Technology Data Repository
EMCS - energy management and control system
ETL - Engineering Technical Letter
ETL 11-1 Pg 26

Air Force Civil Engineer
UESC Playbook
114 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
FACP - fire alarm control panel
FAM - functional area manager
FCC - Federal Communications Commission
FIPS PUB - Federal Information Processing Standard Publication
FISMA - Federal Information Security Management Act
GHz - gigahertz
GIG - Global Information Grid
HQ AF/A7C-2 - The Air Force Deputy Civil Engineer
HQ AF/A7CRT - The Air Force Civil Engineer, Resources Division, Information
Technology Branch
HQ AFCESA - Air Force Civil Engineer Support Agency
HQ AFCESA/CC - Air Force Civil Engineer Support Agency Commander
HQ AFCESA/CEO - Air Force Civil Engineer Support Agency, Operations and
Programs Support Division
HQ AFCESA/CEOA - Air Force Civil Engineer Support Agency, Operations and
Programs Support Division, Engineer Support Branch
HTTPS - Hypertext Transfer Protocol Secure (combination of the
Hypertext Transfer Protocol and a cryptographic protocol)
IA - information assurance
IAM - information assurance manager or management
IAO - information assurance officer
IAS - information assurance strategy
IAT - information assurance technical
IATO - interim authority to operate
IATT - interim authority to test
IAW - in accordance with
ICS - industrial control system
IDS - intrusion detection system
IOC - initial operating capability
IP - Internet Protocol
IPSec - Internet Protocol Security
IPT - integrated product team
IS - information system
ISM - industrial, scientific, and medical
IT - information technology
LAN - local area network
Ltr - letter
MAC - mission assurance category
MaC - media access control
MAJCOM - major command
MDIP - Modified DIACAP Implementation Plan
NIPRNet - Nonsecure Internet Protocol Router Network
NIST - National Institute of Standards and Technology
NIST SP - NIST Special Publication
NOSC
- Network Operations and Security Center
NSA
- National Security Agency
NSTISSI
- National Security Telecommunications and information
Systems
Security Instruction
ETL 11-1 Pg 27

Air Force Civil Engineer
UESC Playbook
115 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
OCONUS - outside the continental United States
O&M - operation and maintenance
OMB - Office of Management and Budget
OPR - office of primary responsibility
PfM - portfolio manager
PIT - platform information technology
PIT-CA - platform information technology certifying authority
PIT-DAA - platform information technology designated accrediting
authority
PITI - platform information technology interconnection
Pkg - package
PLC - programmable logic controller
PM - program manager
POA&M - plan of action and milestones
POC - point of contact
POTS - point of telephone service
RA - risk assessment
Rep - representative
RF - radio frequency
RSA - remote system access
SCADA - supervisory control and data acquisition
SCIF - sensitive compartmented information facility
SIAO - senior information assurance officer
SSL - Secure Sockets Layer
TLS - Transport Layer Security
UMAC - utility monitoring and control
US&P - United States and its possessions
U.S.C. - United States Code
VLAN - virtual local area network
VPS - voice protection system
WWW - World Wide Web
Terms
Accreditation – A management decision by a senior agency official to authorize
operation of a PIT-designated system based on the results of a certification analysis and
other relevant considerations. The PIT DAA can grant system accreditation but cannot
grant connection approval to the AF-GIG. Only the Air Force DAA may grant an ATC.
The current Air Force DAA is AFSPC/A6.
Certification – A comprehensive analysis of the technical and non-technical aspects of
an information system in its operational environment to determine compliance to stated
security requirements and controls. The current Air Force CA is AFNIC.
Computing Environment – A computing environment has a server with multiple stations
working from it. The stations can be standard computers, remote sensors, satellite feeds,
etc.
Computer Network – The constituent element of an enclave responsible for connecting
computing environments by providing short-haul data transport capabilities, such as
ETL 11-1 Pg 28

Air Force Civil Engineer
UESC Playbook
116 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
LANs, or long-haul data transport capabilities, such as wide area and backbone
networks.
Demilitarized Zone (DMZ) – A secure interface between systems or components of
systems or a perimeter network that adds an extra layer of protection between internal
and external networks by enforcing the internal network’s IA policy for external
information exchange. A DMZ, also called a “screened subnet,” provides external,
untrusted sources with restricted access to releasable information while shielding the
internal network from outside attacks.
Enclave – A collection of computing environments connected by one or more internal
networks under the control of a single approval authority and security policy, including
personnel and physical security.
Global Information Grid (GIG) – The globally interconnected, end-to-end set of
information capabilities for collecting, processing, storing, disseminating, and managing
information on demand to warfighters, policy makers, and support personnel. The GIG
includes owned and leased communications and computing systems and services,
software (including applications), data, security services, other associated services, and
National Security Systems. Non-GIG includes stand-alone, self contained, or embedded
IT that is not, and will not be, connected to the enterprise network. (DODD 8000.01)
Information Assurance (IA) – Measures that protect and defend information and
information systems by ensuring their availability, integrity, authentication, confidentiality,
and non-repudiation. This includes providing for restoration of information systems by
incorporating protection, detection, and reaction capabilities.
IA Control – An objective IA condition of integrity, availability, or confidentiality achieved
through the application of specific safeguards or through the regulation of specific
activities that is expressed in a specified format, i.e., a control number, a control name,
control text, and a control class. Specific management, personnel, operational, and
technical controls are applied to each DOD information system to achieve and
appropriate level of integrity, availability, and confidentiality in accordance with OMB
Circular A-130. (DODI 8500.2)
Information System (IS) – A discrete set of information resources organized for the
collection, storage, processing, maintenance, use, sharing, dissemination, disposition,
display, or transmission of information. (Note: Includes AIS applications, enclaves,
outsourced IT-based processes, and PITIs.)
Information Technology (IT) – Any equipment or interconnected system or subsystem
of equipment used in the automatic acquisition, storage, manipulation, management,
movement, control, display, switching, interchange, transmission, or reception of data or
information. This includes equipment used by the executive agency directly or used by a
contractor under a contract with the executive agency, which (i) requires the use of such
equipment, or (ii) requires the use, to a significant extent, of such equipment in the
performance of a service or the furnishing of a product. The term “information
technology” includes computers, ancillary equipment, software, firmware, and similar
ETL 11-1 Pg 29

Air Force Civil Engineer
UESC Playbook
117 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
procedures, services (including support services), and related resources.
Notwithstanding the preceding, the term "information technology” does not include any
equipment that is required by a Federal contractor incidental to a Federal contract.
Mobile Code – Software modules obtained from remote systems, transferred across a
network, and then downloaded and executed on local systems without explicit installation
or execution by the recipient.
Privileged User – An authorized user who has access to system control, monitoring, or
administration functions.
Type Accreditation – DODI 8510.01 defines type accreditation as “the official
authorization to employ identical copies of a system in specified environments.” This form
of C&A allows a single DIACAP package (i.e., System Identification Profile, DIACAP
Implementation Plan, supporting documentation for certification, DIACAP Scorecard, and
IT security POA&M [if required]) to be developed for an archetype (common) version of
an IS that is deployed to multiple locations, along with a set of installation and
configuration requirements or operational security needs, that will be assumed by the
hosting location. AIS applications accreditations are type accreditations. Stand-alone IS
and DMZ accreditations may also be type accreditations.
ETL 11-1 Pg 30

Air Force Civil Engineer
UESC Playbook
118 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
ETL 11-1 Pg 31

Air Force Civil Engineer
UESC Playbook
119 | P a g e
ETL 11-1
Civil Engineer Industrial Control Systems
Information Assurance Compliance
DISTRIBUTION LIST
SPECIAL INTEREST ORGANIZATIONS
Information Handling Services
15 Inverness Way East
(1)
Construction Criteria Database (1)
National Institute of Bldg Sciences
Englewood, CO 80150
Washington, DC 20005
ETL 11-1 Pg 32
